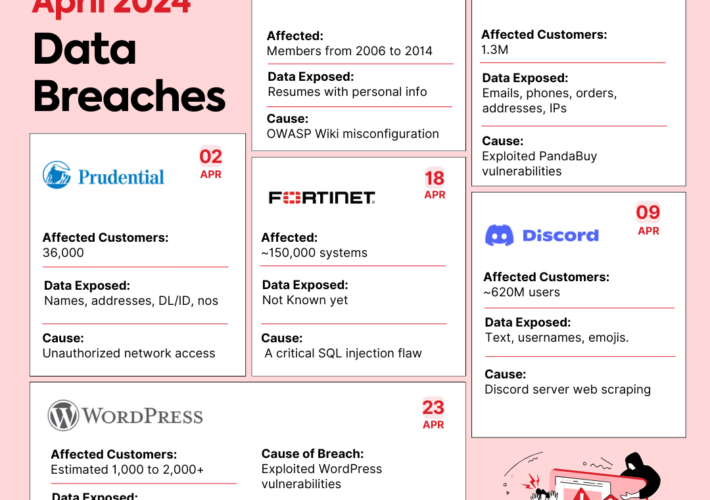
Source: securityboulevard.com – Author: Shubham Jha Data breaches are like uninvited guests at a party – they show up unexpectedly, take what they want, and leave...
Month: May 2024
Intel 471 Acquires Cyborg Security to Expand Its Cyber Threat Intelligence Portfolio with Innovative Threat Hunting Capabilities – Source: securityboulevard.com
Source: securityboulevard.com – Author: Cyborg Security The fusion of Cyborg Security with Intel 471 delivers advanced behavioral detections and unprecedented insight into the threat actor landscape....
RSAC 2024 Innovation Sandbox | VulnCheck: A Solution to the Challenge of Vulnerability Prioritization – Source: securityboulevard.com
Source: securityboulevard.com – Author: NSFOCUS The RSA Conference 2024 will kick off on May 6. Known as the “Oscars of Cybersecurity,” the RSAC Innovation Sandbox has...
Navigating the Future: Insights From the M&A Symposium at Kaseya Connect Global – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kaseya The technology industry continually evolves, and managed service providers (MSPs) are often at the forefront of this transformation. We brought MSPs,...
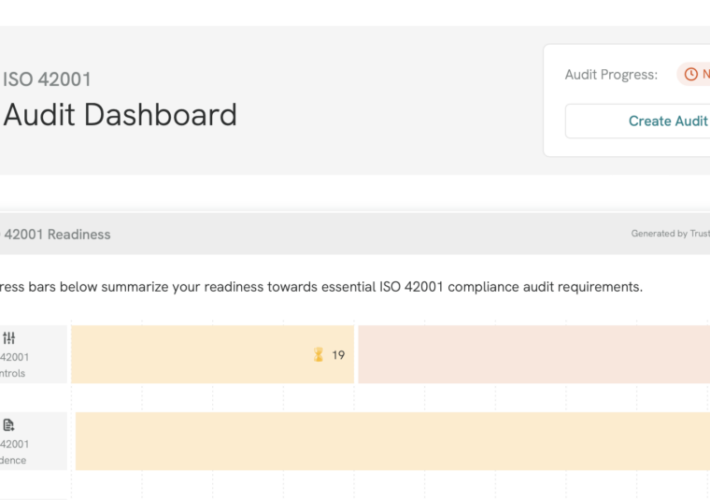
Introducing ISO 42001 and NIST RMF Frameworks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tejas Ranade While AI has created exciting new opportunities for business, it has created urgent questions around ethics, responsible use, development, and...
PIPEDA Compliance with Accutive Data Discovery and Masking: Understanding and protecting your Canadian sensitive data – Source: securityboulevard.com
Source: securityboulevard.com – Author: Accutive Security What is PIPEDA, Canada’s Personal Information Protection and Electronic Documents Act? PIPEDA, or the Personal Information Protection and Electronic Documents...
TrustCloud Product Updates: April 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tejas Ranade You know us: Every month we’re cooking up something new! Here are the updates that hit TrustCloud this month. TrustShare...
News alert: Cybersixgill unveils ‘Third-Party Intelligence’ to deliver vendor-specific threat intel – Source: securityboulevard.com
Source: securityboulevard.com – Author: bacohido Tel Aviv, Israel – April 30, 2024 – Cybersixgill, the global cyber threat intelligence data provider, broke new ground today by introducing its Third-Party Intelligence module....
April Recap: New AWS Services and Sensitive Permissions – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tally Shea Amazon Web Services (AWS) has over 200 cloud services available to help organizations innovate, build business, and secure their data....
AI Voice Scam – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments Clive Robinson • May 1, 2024 8:28 AM @ Bruce, ALL, In a world that is moving rapidly...
WhatsApp in India – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments numberri • April 30, 2024 7:42 AM I know another case earlier this year is when India threatened...
Island Gets $175M Series D Funding, Doubles Valuation to $3B – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Endpoint Security Investments in Island Led by Coatue and Sequoia Support Global Expansion, R&D, M&A Michael Novinson (MichaelNovinson) • April 30,...
How Personal Branding Can Elevate Your Tech Career – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Training & Security Leadership Your Personal Brand Is as Crucial as Any Skill in Your Tech Toolkit Brandy Harris • April...
DHS: AI-Enhanced Nuclear and Chemical Threats Are Risk to US – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development New Report Says Global Threat Actors May Use AI to...
Defining a Detection & Response Strategy – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
Live Webinar | From Risk-Based Vulnerability Management to Exposure Management: The Future of Cybersecurity – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Zaira Pirzada VP of Product Marketing, Hive Pro Zaira Pirzada is the VP of Product Marketing at Hive Pro. Prior to...
Verizon Breach Report: Vulnerability Hacks Tripled in 2023 – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Video , Vulnerability Assessment & Penetration Testing (VA/PT) Data Breach Report Lead Author Alex Pinto Discusses...
Patched Deserialization Flaw in Siemens Product Allows RCE – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Critical Infrastructure Security The Siemens Simatic Energy Manager Used an Unsafe BinaryFormatter Method Prajeet Nair (@prajeetspeaks) • April 30, 2024 ...
New Latrodectus malware attacks use Microsoft, Cloudflare themes – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Latrodectus malware is now being distributed in phishing campaigns using Microsoft Azure and Cloudflare lures to appear legitimate while making...
Philadelphia Inquirer: Data of over 25,000 people stolen in 2023 breach – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Daily newspaper Philadelphia Inquirer revealed that attackers behind a May 2023 security breach have stolen the personal and financial information...
R language flaw allows code execution via RDS/RDX files – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A new vulnerability has been discovered in the R programming language that allows arbitrary code execution upon deserializing specially crafted RDS and RDX files....
Google now pays up to $450,000 for RCE bugs in some Android apps – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Google has increased rewards for reporting remote code execution vulnerabilities within select Android apps by ten times, from $30,000 to...
Millions of Docker repos found pushing malware, phishing sites – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Three large-scale campaigns targeted Docker Hub users, planting millions of repositories that pushed malware and phishing sites since early 2021. As...
New Wpeeper Android malware hides behind hacked WordPress sites – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A new Android backdoor malware named ‘Wpeeper’ has been spotted in at least two unofficial app stores mimicking the Uptodown...
Change Healthcare hacked using stolen Citrix account with no MFA – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas 4/30/24: Update added below about Change Healthcare Citrix credentials previously stolen by information-stealing malware. UnitedHealth confirms that Change Healthcare’s network was...