Source: www.techrepublic.com – Author: Megan Crouse The number of Microsoft vulnerabilities has mostly flattened in 2023, with elevation of privilege and identity attacks being particularly common,...
Month: April 2024
OpenAI’s GPT-4 Can Autonomously Exploit 87% of One-Day Vulnerabilities, Study Finds – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Fiona Jackson The GPT-4 large language model from OpenAI can exploit real-world vulnerabilities without human intervention, a new study by University of...
Women in Cybersecurity: ISC2 Survey Shows Pay Gap and Benefits of Inclusive Teams – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Megan Crouse Only 17% of respondents to the ISC2 Cybersecurity Workforce Study were women, showing a continued struggle for workplaces to recruit...
Get a Lifetime Subscription of FastestVPN for just $40 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Academy Published April 25, 2024 We may earn from vendors via affiliate links or sponsorships. This might affect product placement on...
Prompt Hacking, Private GPTs, Zero-Day Exploits and Deepfakes: Report Reveals the Impact of AI on Cyber Security Landscape – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Fiona Jackson AI’s newfound accessibility will cause a surge in prompt hacking attempts and private GPT models used for nefarious purposes, a...
Can a VPN Be Hacked? – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Luis Millares A virtual private network is one of the easiest ways users can protect their online activity. Through what’s called a...
Server Inventory Checklist (Free Download) – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Threats from malware, cryptographic infections and compromised networks have never been greater. Headlines regularly attest to such widespread problems, from infection-felled organizations...
NIST Cybersecurity Framework: A Cheat Sheet for Professionals (Free PDF) – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: The tech world has a problem: Security fragmentation. There’s no standard set of rules or even language for mitigating cyber risk used...
ToddyCat is making holes in your infrastructure – Source: securelist.com
Source: securelist.com – Author: Andrey Gunkin, Alexander Fedotov, Natalya Shornikova We continue covering the activities of the APT group ToddyCat. In our previous article, we described...
Assessing the Y, and How, of the XZ Utils incident – Source: securelist.com
Source: securelist.com – Author: GReAT High-end APT groups perform highly interesting social engineering campaigns in order to penetrate well-protected targets. For example, carefully constructed forum responses...
Zero Trust strategies for navigating IoT/OT security challenges – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau Travais ‘Tee’ Sookoo leverages his 25 years of experience in network security, risk management, and architecture to help businesses of all...
GUEST ESSAY: Here’s why securing smart cities’ critical infrastructure has become a top priority – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Zac Amos Critical infrastructure like electrical, emergency, water, transportation and security systems are vital for public safety but can be...
Breaking Down Cybersecurity: The Real Meaning Behind the Jargon – Source: securityboulevard.com
Source: securityboulevard.com – Author: Matt Palmer Cyber security is often conflated with the term confidentiality, but that is not correct. Traditionally, professionals tend to define it...
Russian FSB Counterintelligence Chief Gets 9 Years in Cybercrime Bribery Scheme – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs The head of counterintelligence for a division of the Russian Federal Security Service (FSB) was sentenced last week to nine years...
LabHost Phishing Platform is Latest Target of International Law Agencies – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt The takedown this week of a massive phishing-as-a-service (PhaaS) operation spanned law enforcement agencies from both sides of the Atlantic...
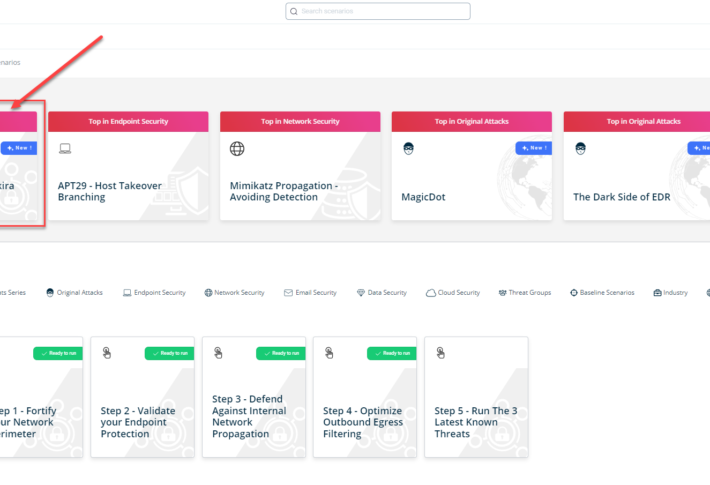
Choosing SOC Tools? Read This First [2024 Guide] – Source: securityboulevard.com
Source: securityboulevard.com – Author: Shriram Sharma Security operations centers (SOCs) are the front lines in the battle against cyber threats. They use a diverse array of...
USENIX Security ’23 – GAP: Differentially Private Graph Neural Networks with Aggregation Perturbation – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters: *Sina Sajadmanesh, Ali Shahin Shamsabadi, Aurélien Bellet, Daniel Gatica-Perez* Many thanks to USENIX for publishing their outstanding USENIX Security...
SafeBreach Coverage for AA24-109A (Akira Ransomware) – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kaustubh Jagtap Author: Kaustubh Jagtap, Product Marketing Director, SafeBreach On April 18th, the United States’ Federal Bureau of Investigation (FBI), Cybersecurity and...
Taking Time to Understand NIS2 Reporting Requirements – Source: securityboulevard.com
Source: securityboulevard.com – Author: Brian Robertson The newest version of the European Union Network and Information Systems directive, or NIS2, came into force in January 2023....
Daniel Stori’s ‘WC’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the inimitable Daniel Stori at Turnoff.US! Permalink *** This is a Security Bloggers Network syndicated blog from Infosecurity.US authored...
USENIX Security ’23 – Inductive Graph Unlearning – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX Security ’23 – Inductive Graph Unlearning by Marc Handelman on...
From DAST to dawn: why fuzzing is better solution | Code Intelligence – Source: securityboulevard.com
Source: securityboulevard.com – Author: Natalia Kazankova Security testing allows you to evaluate the robustness of applications and systems and identify potential weaknesses that attackers may exploit....
Cybersecurity Insights with Contrast CISO David Lindner | 4/19/24 – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Lindner, Director, Application Security Insight #1 One of the most significant errors an organization can make is assuming they are not...
UK ICO Weighs Role of ‘Accuracy’ in Generative AI – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Governance & Risk Management , Next-Generation Technologies & Secure Development But Accurate Data Doesn’t Always...
Live Webinar | Modernizing Identity Management: From Legacy Systems to Cutting-Edge Security – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
Hacker Threatens to Expose Sensitive World-Check Database – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime ‘GhostR’ Claims to Have 5.3 Million Records from Major Screening Database Chris Riotta (@chrisriotta) •...
Mitre Says Hackers Breached Unclassified R&D Network – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Incident & Breach Response , Patch Management Threat Actor Exploited Ivanti Zero-Day Vulnerabilities in Cyberattack Chris...
CEO Andre Durand on Why Ping, ForgeRock Are Better Together – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Identity & Access Management , Security Operations , Video How Ping-ForgeRock Merger Provides Enhanced Deployment Flexibility, More Services Michael Novinson (MichaelNovinson)...
Friday Squid Blogging: Squid Trackers – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments Jerome • April 19, 2024 8:20 PM @Clive Robinson RE Bondi Junction incident. I guess its an internationally...
The Importance of Cyber Hygiene for Businesses – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Stevin By Rigo Van den Broeck, Executive Vice President, Cyber Security Product Innovation at Mastercard Cybercrime is set to cost $10.3 trillion...















![choosing-soc-tools?-read-this-first-[2024-guide]-–-source:-securityboulevard.com](https://ciso2ciso.com/wp-content/uploads/2024/04/128699/choosing-soc-tools-read-this-first-2024-guide-source-securityboulevard-com-710x500.jpg)