Source: www.schneier.com – Author: Bruce Schneier A new paper presents a polynomial-time quantum algorithm for solving certain hard lattice problems. This could be a big deal...
Month: April 2024
Upcoming Speaking Engagements – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier About Bruce Schneier I am a public-interest technologist, working at the intersection of security, technology, and people. I’ve been writing...
Attacking AWS – Offensive Security Aproach
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Artificial Intelligence and Cybersecurity Research 2023
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Using the LockBit builder to generate targeted ransomware – Source: securelist.com
Source: securelist.com – Author: Eduardo Ovalle, Francesco Figurelli, Cristian Souza, Ashley Muñoz The previous Kaspersky research focused on a detailed analysis of the LockBit 3.0 builder...
Zambia arrests 77 people in swoop on “scam” call centre – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley Law enforcement officers in Zambia have arrested 77 people at a call centre company they allege had employed local school-leavers...
All about Security Operations Center
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A Guide to Building a Secure SDLC – Which Scanning Tools Should I look at, and where do they go?
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2023 Mobile Banking Heists Report
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
40 under 40 in CyberSecurity 2024
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
40 Days in DeepDark Web About Crypto Scam
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
8 Principles of Supply Chain Risk Management
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
USENIX Security ’23 – How to Bind Anonymous Credentials to Humans – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX Security ’23 – How to Bind Anonymous Credentials to Humans...
Iran Launches Wave of Retaliatory Strikes at Israel – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Critical Infrastructure Security , Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Reports: 100s of Drones and Missiles Shot Down;...
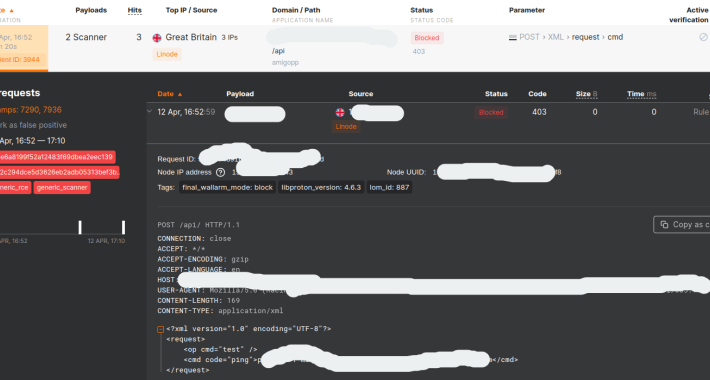
How to track and stop CVE-2024-3400: Palo Alto Devices API Exploit Causing Critical Infrastructure and Enterprise Epidemics – Source: securityboulevard.com
Source: securityboulevard.com – Author: wlrmblog On Friday April 12, Palo Alto disclosed that some versions of PAN-OS are not only vulnerable to remote code execution, but...
What is Web Application Security Testing? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Shikha Dhingra Web application security testing aims to detect, prevent, and address security vulnerabilities within web applications. Flaws in web application coding...
Firebird RAT creator and seller arrested in the U.S. and Australia – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A joint police operation between the Australian Federal Police (AFP) and the FBI has led to the arrest and charging...
Hacker claims Giant Tiger data breach, leaks 2.8M records online – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ax Sharma Canadian retail chain Giant Tiger disclosed a data breach in March 2024. A threat actor has now publicly claimed responsibility for...
Palo Alto Networks zero-day exploited since March to backdoor firewalls – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Suspected state-sponsored hackers have been exploiting a zero-day vulnerability in Palo Alto Networks firewalls tracked as CVE-2024-3400 since March 26,...
UK flooded with forged stamps despite using barcodes — to prevent just that – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ax Sharma Royal Mail, the British postal and courier service began switching all snail mail stamps to barcoded stamps last year. The...
Threat Hunter’s Handbook – Using Log Analytics to Find and Neutralize Hidden Threats in Your Environment
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Hunters Handbook Endgame’s Guide to Adversary Hunting
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
THE EU’S MOST THREATENING by EUROPOL
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Responding to a cyber incident – a guide for CEOs
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CREDENTIAL DUMPING
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Pwning the Domain Lateral Movement
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Implementing the Health Insurance Portability and Accountability Act(HIPAA) Security Rule
This publication aims to help educate readers about the security standards included in the Health Insurance Portability and Accountability Act (HIPAA) Security Rule [Sec. Rule], as...
Data Confidentiality: Identifying and Protecting Assets Against Data Breaches
NIST SPECIAL PUBLICATION 1800-28 CHALLENGE An organization must protect its information from unauthorized access and disclosure. Data breaches large and small can have far-reaching operational, financial,...
PING Basic IP Network Troubleshooting
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The NIST Cybersecurity Framework (CSF) 2.0
The NIST Cybersecurity Framework (CSF) 2.0 provides guidance to industry, government agencies, and organizations of all sizes and sectors to manage cybersecurity risks effectively. It offers...