Source: securityboulevard.com – Author: Shriram Sharma RSA Conference 2024, taking place at San Francisco’s Moscone Center from May 6-9, is set to gather the world’s foremost...
Day: April 16, 2024
MY TAKE: GenAI revolution — the transformative power of ordinary people conversing with AI – Source: securityboulevard.com
Source: securityboulevard.com – Author: bacohido By Byron V. Acohido San Francisco, Calif. — The amazing digital services we have today wouldn’t have come to fruition without...
Roku: Credential Stuffing Attacks Affect 591,000 Accounts – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Almost 600,000 Roku customers had their accounts hacked through two credential stuffing attacks several weeks apart, illustrating the ongoing risks...
MSP Guide: How to Safeguard Your Clients During a Ransomware Attack – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kevin Smith As a managed service provider (MSP), you are tasked with keeping clients from malicious software infections and ransomware attacks. Even...
USENIX Security ’23 – An Empirical Study & Evaluation of Modern CAPTCHAs – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters: *Andrew Searles, Yoshimichi Nakatsuka, Ercan Ozturk, Andrew Paverd, Gene Tsudik, Ai Enkoji* Many thanks to USENIX for publishing their...
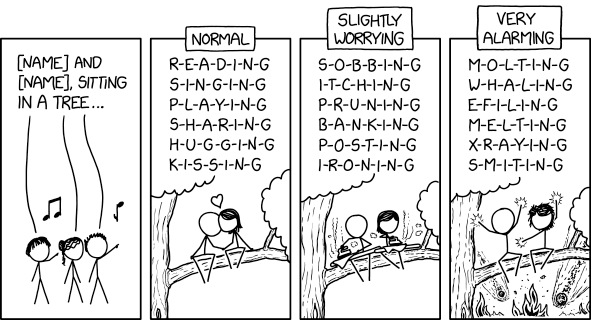
Randall Munroe’s XKCD ‘Sitting in a Tree’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
Zscaler to Acquire Airgap Networks to Segment Endpoint Traffic – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard Zscaler plans to acquire Airgap Networks to apply network segmentation in a way that improves security without requiring organizations to...
Likely State Hackers Exploiting Palo Alto Firewall Zero-Day – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Endpoint Security Company Released a Hotfix to the Command Injection Vulnerability Mihir Bagwe (MihirBagwe) • April 15, 2024 Likely...
FTC Bans Online Mental Health Firm From Sharing Certain Data – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Governance & Risk Management , Healthcare Proposed Action Also Orders Cerebral Inc. to Pay $7M Penalty...
Law Firm to Pay $8M to Settle Health Data Hack Lawsuit – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Healthcare , Industry Specific , Legislation & Litigation Orrick Herrington Cyberattack Compromised Clients’ Data, Affected Nearly 638,000 Marianne Kolbasuk McGee (HealthInfoSec)...
Sisense Breach Highlights Rise in Major Supply Chain Attacks – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , Governance & Risk Management Experts Warn of Growing Threat From Supply Chain Attacks After High-Profile Breach...