Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Jan Zwoliński via Alamy Stock Photo Despite the LockBit ransomware-as-a-service (RaaS) gang claiming to...
Day: April 3, 2024
More Than Half of Organizations Plan to Adopt AI Solutions in Coming Year, Reports Cloud Security Alliance and Google Cloud – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE SEATTLE – April 3, 2024 – A new survey from the Cloud Security Alliance (CSA), the world’s leading organization dedicated...
CyberRatings.org Announces Test Results for Cloud Network Firewall – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE Austin, TX – April 3, 2024 – CyberRatings.org (CyberRatings), the non-profit entity dedicated to providing confidence in cybersecurity products and services...
TAG Report Reveals Endpoint Backup Is Essential to Improving Data Resiliency – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE MINNEAPOLIS, April 2, 2024 – Businesses are facing a critical gap when it comes to protecting endpoint data, according to...
TruCentive Enhances Privacy With HIPAA Compliant Personal Information De-identification – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE PALO ALTO, Calif., April 2, 2024/PRNewswire-PRWeb/ — TruCentive, a leader in incentive automation solutions, announced a significant enhancement to its...
How Soccer’s 2022 World Cup in Qatar Was Nearly Hacked – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: rarrarorro via Shutterstock About six months before the 2022 FIFA World Cup soccer tournament in Qatar, a...
Oil & Gas Sector Falls for Fake Car Accident Phishing Emails – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: Frode Koppang via Alamy Stock Photo An updated version of the Rhadamanthys malware-as-a-service (MaaS) is...
Omni Hotel IT Outage Disrupts Reservations, Digital Key Systems – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 2 Min Read Source: Andrew Shurtleff via Alamy Stock Photo Omni Hotels & Resorts last week reportedly experienced an...
Streamlining supply chains | The impact of IoT on transportation and logistics – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau By Antoinette Hodes, a Check Point Global Solutions Architect and Evangelist with the Check Point Office of the CTO. IoT is...
U.S. Treasury warns financial sector, AI threats “outpacing” security – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: According to a new U.S. Treasury Department report, the financial services industry is extremely vulnerable to cyber threats that...
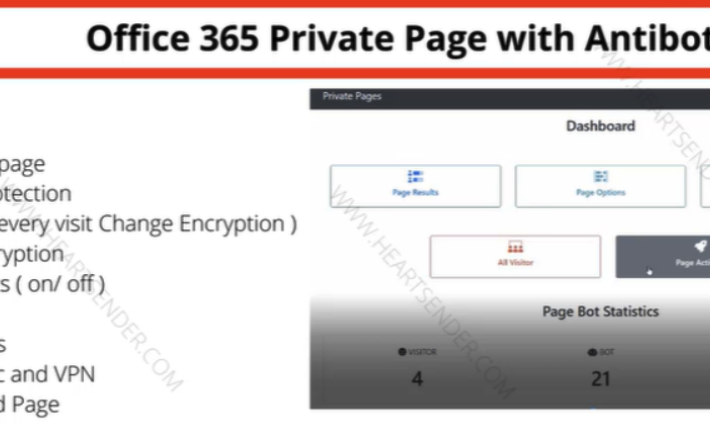
‘The Manipulaters’ Improve Phishing, Still Fail at Opsec – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs Roughly nine years ago, KrebsOnSecurity profiled a Pakistan-based cybercrime group called “The Manipulaters,” a sprawling web hosting network of phishing and...
Windows Malware Investigations
“We were targeted by a sophisticated, advanced persistent threat.” The document provides a comprehensive overview of malware analysis, with a specific focus on the Qbot malware,...
Windows Hacking
A long time ago there existed a time and space where the 6502 processor was everywhere. There was no internet, there was no cell phone and...
The Threat Intelligence Handbook Second Edition
Moving Toward a Security Intelligence Program Today, cyber threats are coming from everywhere — the open web and dark web, but also partners and other third...
State of the UAE Cybersecurity Landscape
In the dynamic cyber landscape of the United Arab Emirates (UAE), a startling statistic serves as a clarion call to action: the Nation currently hosts at...
Cyber Safety Review Board Report Slams Microsoft Security Failures in Government Email Breach – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Microsoft has been blamed for “cascade of security failures” that enabled Chinese threat actors to access US government officials’ emails in...
Prudential Financial Notifies 36,000 Individuals of Data Breach – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Prudential Financial last Friday commenced the process of informing over 36,000 individuals about a data breach that occurred in early February...
Infostealers Prevalent in Retail Sector Cybercrime Trends – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Infostealers, IoT botnets and remote access tools have been identified as the primary weapons employed by cyber-attackers targeting retail organizations over...
Bridging IT and OT Cybersecurity with AI – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Reduce Alerts by 57% with Difenda AIRO By Andrew Hodges, VP Service Delivery & Product Development, Difenda In a technology-driven...
Accelerate the path to PCI DSS 4.0 adoption – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Héctor Guillermo Martínez, President of GM Sectec With the release of a new version of the PCI DSS 4.0...
Protective Security Guide for CSOs
The role of the Chief Security Officer (CSO) is the key to ensuring the secure delivery of Government business. As a CSO, you are tasked with...
Global Threat Intelligence Report March 2024 by Blackberry Cybersecurity
As we enter 2024, we mark a full calendar year of quarterly BlackBerry® Global Threat Intelligence Reports. And what a year it has been. Over the...
Implement Network Segmentation Encryption Cloud Envir by NSA
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Active Directory Security Guide
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Microsoft warns Gmail blocks some Outlook email as spam, shares fix – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft has confirmed that some Outlook.com users are experiencing issues with emails being blocked and marked as spam when trying...
Winnti’s new UNAPIMON tool hides malware from security software – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The Chinese ‘Winnti’ hacking group was found using a previously undocumented malware called UNAPIMON to let malicous processes run without...
Omni Hotels experiencing nationwide IT outage since Friday – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Omni Hotels & Resorts has been experiencing a chain-wide outage that brought down its IT systems on Friday, impacting reservation,...
New Chrome feature aims to stop hackers from using stolen cookies – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Google announced a new Chrome security feature called ‘Device Bound Session Credentials’ that ties cookies to a specific device, blocking...
Google agrees to delete Chrome browsing data of 136 million users – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Google has agreed to delete billions of data records collected from 136 million Chrome users in the United States, as...