Source: www.techrepublic.com – Author: Cedric Pernet Highlights from CrowdStrike’s 2024 report: Identity-based and social engineering attacks still take center stage. Cloud-environment intrusions have increased by 75%...
Day: February 27, 2024
4 Best Free VPNs for 2024 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Luis Millares Best overall free VPN: Proton VPN Best for basic protection: hide.me VPN Best for multiple devices: Windscribe VPN Best beginner...
Apple Announces Post-Quantum Encryption Algorithms for iMessage – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier Apple announced PQ3, its post-quantum encryption standard based on the Kyber secure key-encapsulation protocol, one of the post-quantum algorithms selected...
Malicious Packages in npm, PyPI Highlight Supply Chain Threat – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Threat groups continue to look to open source software repositories to launch supply-chain attacks, with cybersecurity vendor Phylum reporting about...
USENIX Security ’23 – Synchronization Storage Channels (S2C): Timer-less Cache Side-Channel Attacks on the Apple M1 via Hardware Synchronization Instructions – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters: Jiyong Yu, Aishani Dutta, Trent Jaeger, David Kohlbrenner, Christopher W. Fletcher Many thanks to USENIX for publishing their outstanding...
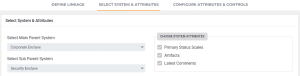
Save Time and Steps with Ignyte’s Control Inheritance Automation – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ignyte Team If you are managing multiple GRC frameworks for multiple environments, then you know how powerful it is to have clearly-defined...
Making Companies Whole: The Impact of Cyber Insurance on Materiality – Source: securityboulevard.com
Source: securityboulevard.com – Author: Axio Hot Topics Malicious Packages in npm, PyPI Highlight Supply-Chain Threat USENIX Security ’23 – Synchronization Storage Channels (S2C): Timer-less Cache Side-Channel...
Randall Munroe’s XKCD ‘Light Leap Years’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the comic artistry and dry wit of Randall Munroe, creator of XKCD Permalink *** This is a Security Bloggers...
USENIX Security ’23 – Daniel Katzman, William Kosasih, Chitchanok Chuengsatiansup, Eyal Ronen, Yuval Yarom – The Gates of Time: Improving Cache Attacks with Transient Execution – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Many thanks to USENIX for publishing their outstanding USENIX Security ’23 Presenter’s content, and the organizations strong commitment to Open...
LockBit Ransomware Group Returns After Law Enforcement Operation – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt The LockBit ransomware group is swinging back days after U.S. and UK law enforcement agencies announced they had disrupted the...
The xSPM Trend: Security Posture Management for Everything – Source: securityboulevard.com
Source: securityboulevard.com – Author: Gilad David Maayan Before we dive into the xSPM trend, let’s define what security posture management (SPM) is. SPM refers to the...
Profiling the xDedic Cybercrime Service Enterprise – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dancho Danchev The popular cybercrime-friendly xDedic service was recently shut down and in this analysis we’ll take an in-depth look inside the...
Lost to the Highest Bidder: The Economics of Cybersecurity Staffing – Source: securityboulevard.com
Source: securityboulevard.com – Author: Maria Chachas Mastakas For about a decade, much has been written about the scarcity of qualified cybersecurity talent. There’s no lack of...
North Korean Group Seen Snooping on Russian Foreign Ministry – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Government Espionage Groups Deploy Info Stealer to Monitor Russia’s Diplomatic Moves...
SSH Exec Rami Raulas Named Interim CEO in Finnish Shakeup – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Encryption & Key Management , Governance & Risk Management , Operational Technology (OT) Teemu Tunkelo Left SSH Abruptly After License Sales...
Groups Warn Health Sector of Change Healthcare Cyber Fallout – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , Fraud Management & Cybercrime , Governance & Risk Management Some Researchers Confident ConnectWise ScreenConnect Flaw Was...
NIST Unveils Second Iteration of Cybersecurity Framework – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Critical Infrastructure Security , Governance & Risk Management New CSF Adds ‘Governance’ to Core Functions Chris Riotta (@chrisriotta) • February 26,...