Source: securityboulevard.com – Author: Team Nuspire Several cybersecurity advisories and agencies recommend not caving into ransomware gangs’ demands and paying their ransoms. For a while, though,...
Day: February 14, 2024
Improving Software Quality with the OWASP BOM Maturity Model – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deb Radcliff By Deb Radcliff, industry analyst and editor of CodeSecure’s TalkSecure educational blogs and podcasts (syndicated at Security Boulevard, YouTube, and...
Qmulos Launches Q-Compliance Core for Businesses in Need of a Modern Compliance Approach – Source: securityboulevard.com
Source: securityboulevard.com – Author: Alison Underdown As cyber threats grow alongside penalties for negligence, risk and compliance management has become a higher priority function across organizations,...
USENIX Security ’23 – Chenghong Wang, David Pujol, Kartik Nayak, Ashwin Machanavajjhal – Private Proof-of-Stake Blockchains using Differentially-Private Stake Distortion – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX Security ’23 – Chenghong Wang, David Pujol, Kartik Nayak, Ashwin...
Exploiting Kubernetes through Operator Injection – Source: securityboulevard.com
Source: securityboulevard.com – Author: Thomas Tan Intro The Kubernetes documentation describes operators as “software extensions to Kubernetes that use custom resources to manage applications and their components.” These...
News alert: Kiteworks named as a founding member of NIST’s new AI safety consortium – ‘AISIC’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: bacohido San Mateo, Calif., Feb. 13, 2023 – The U.S. White House announced groundbreaking collaboration between OpenPolicy and leading innovation companies, including...
‘Incompetent’ FCC Fiddles With Data Breach Rules – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings While Rome burns, Federal Communications Commission is once again behind the curve. The FCC is telling telcos to tell them about data...
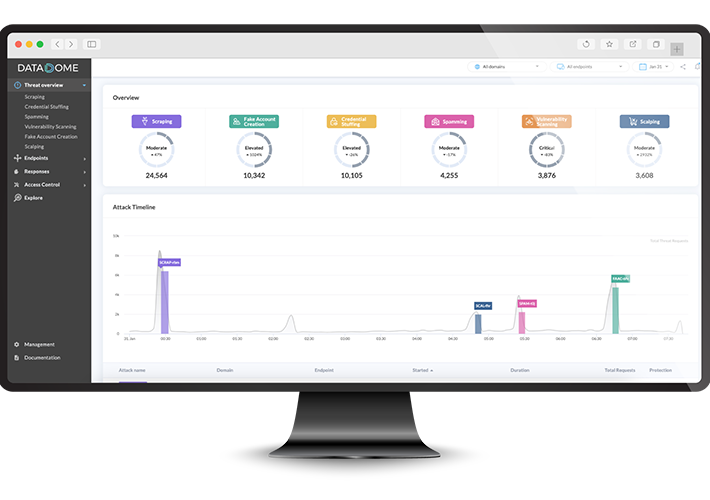
Guide to Advanced Fraud Monitoring & Proactive Detection in 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: DataDome If you sell anything online or store any sensitive information digitally, you’re at risk of fraud. Online payment fraud losses doubled...
Comic Agilé – Mikkel Noe-Nygaard, Luxshan Ratnaravi – #278 – The Non-Senior Consultant – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Wednesday, February 14, 2024 Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News...
Reshaping Trust and Security for the Realities of 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jenn Markey The new year is always a time for reflection, and after a year shaped by AI, biometrics, and nation-state attacks...
Europe’s AI Act Poised To Become Law After Committees Vote – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Legislation & Litigation , Next-Generation Technologies & Secure Development ACt Will Require Developers to Allows...
Responsible Use of Artificial Intelligence – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Governance & Risk Management , Next-Generation Technologies & Secure Development A Practical Guide for Cybersecurity...
Generative AI and the Brave New World of Work – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development , Professional Certifications & Continuous Training CyberEd.io’s Steve King on...
USPTO: AI Can Assist Inventors But Can’t Hold Patents – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development Humans Must Show Significant Role in AI-Assisted Cases for Inventor...
More Signs of a Qakbot Resurgence – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Endpoint Detection & Response (EDR) , Fraud Management & Cybercrime Qakbot Wouldn’t Be the First Trojan to Come Back...
They’re Back? HHS OCR Is Eyeing the Return of HIPAA Audits – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Healthcare , Industry Specific , Standards, Regulations & Compliance The Agency Is Surveying Previous Auditees to Reassess the Dormant Program Marianne...