Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Free unofficial patches are available for a new Windows zero-day flaw dubbed EventLogCrasher that lets attackers remotely crash the Event Log...
Day: February 2, 2024
CISA orders federal agencies to disconnect Ivanti VPN appliances by Saturday – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan CISA has ordered U.S. federal agencies to disconnect all Ivanti Connect Secure and Policy Secure VPN appliances vulnerable to multiple...
Heimdal Partners with Jupiter Technology to Distribute Cybersecurity Solutions in Japan – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Madalina Popovici We have partnered with Jupiter Technology Corporation, who will distribute our cybersecurity products across Japan as part of a long-term...
USENIX Security ’23 – Cas Cremers, Charlie Jacomme, Aurora Naska – Formal Analysis of Session-Handling in Secure Messaging: Lifting Security from Sessions to Conversations – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Thursday, February 1, 2024 Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News...
Diving into the 2024 Security Megatrends – Source: securityboulevard.com
Source: securityboulevard.com – Author: Team Nuspire Cybersecurity is a fast-paced and constantly changing industry. Ongoing technological advancements, new paradigms and evolving threat actor techniques make the...
Telegram is a Wide-Open Marketplace for Phishing Tools – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt The encrypted messaging app Telegram has become a veritable marketplace for bad actors who want to launch effective phishing campaigns...
The SOC 2 Effect: Elevating Security and Trust in Netography Fusion – Source: securityboulevard.com
Source: securityboulevard.com – Author: Raymond Kirk The SOC 2 Effect: Elevating Security and Trust in Netography Fusion Raymond Kirk, Product Manager Satisfying the System and Organization...
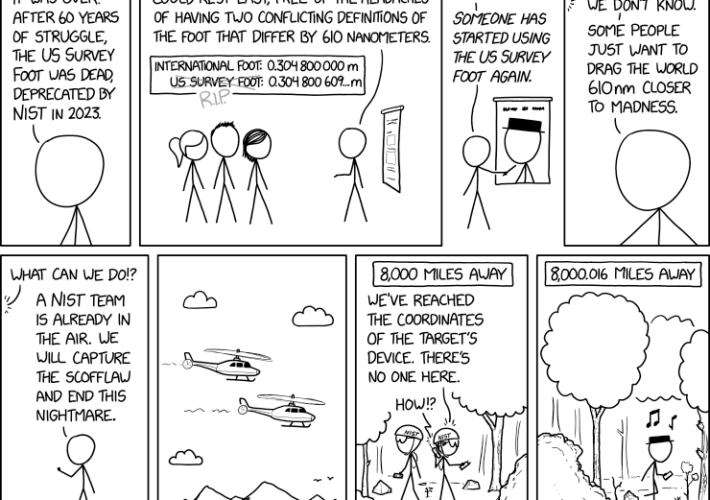
Randall Munroe’s XKCD ‘US Survey Foot’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the comic artistry and dry wit of Randall Munroe, creator of XKCD Permalink *** This is a Security Bloggers...
Improved Security Agility and Adaptability with Dynamic Runtime Lists | Impart Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Impart Security Blog We’re proud to announce Impart Security’s newest release, Dynamic Runtime Lists, which are purpose-built to enable security teams...
Optimize Control Health Management Across Business Levels: Introducing Scopes – Source: securityboulevard.com
Source: securityboulevard.com – Author: Hyperproof Team Managing controls across multiple business units becomes increasingly challenging and costly as operational requirements evolve. To help compliance leaders efficiently...
FBI Warning: China Will Hack US Infra. (via Router Botnet) – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings FBI head Wray won’t tolerate China’s “real-world threat to our physical safety.” Harsh rhetoric against the People’s Republic yesterday at...
USENIX Security ’23 – TreeSync: Authenticated Group Management for Messaging Layer Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Sponsorships Available Author/Presenters: Théophile Wallez, Inria Paris; Jonathan Protzenko, Benjamin Beurdouche, Karthikeyan Bhargavan Inria Paris Distinguished Paper Award Winner and...
Aim Security to Limit Exposure of Sensitive Data to Generative AI Services – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard Aim Security this week emerged from stealth to launch a platform that leverages large language models (LLMs) to prevent end...
Uber Fined 10 Million Euros by Dutch Data Regulator – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 General Data Protection Regulation (GDPR) , Standards, Regulations & Compliance Ride-Hailing Company Fined for Inadequate Data Transparency Practices Under GDPR Akshaya...
How Long Will FBI’s ‘Volt Tycoon’ Router Interdiction Stick? – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Governance & Risk Management Volume of Poorly Secured, Legacy IoT That...
Breach Roundup: CIA Hacking Tool Leaker Gets 40 Years – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Governance & Risk Management Also: Cloudflare Was Hacked With Stolen Okta Token Anviksha More...
Webinar | Your Hybrid Cloud Is Under Attack: Protect It With Zero Trust! – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Dennis Payton Sr. Product Marketing Manager, Software Firewalls, Palo Alto Networks Dennis has a full career in telecommunications, networking, enterprise applications...
FTC Blasts Blackbaud’s ‘Shoddy’ Practices in Ransomware Hack – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Healthcare , Industry Specific FTC Is Latest Agency to Rebuke Fundraising Firm for Lax Security in...
Palo Alto Told to Pay Centripetal $150M for Patent Theft – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Legislation & Litigation , Standards, Regulations & Compliance Federal Court Says Palo Alto Networks Violated Centripetal’s Patent Rights Chris Riotta (@chrisriotta)...
‘Commando Cat’ Is Second Campaign of the Year Targeting Docker – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Saro O Neal via Alamy Stock Photo In findings released by Cado researchers, they discovered a malware campaign,...
New NCCoE Guide Helps Major Industries Observe Incoming Data While Using Latest Internet Security Protocol – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE Companies in major industries such as finance and health care must follow best practices for monitoring incoming data for cyberattacks....
ProcessUnity Introduces Industry’s All-In-One Third-Party Risk Management Platform – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE BOSTON–(BUSINESS WIRE)– ProcessUnity, provider of comprehensive end-to-end third-party risk management and cybersecurity solutions to leading enterprises, today announced the completed...
Delinea Research Reveals that Ransomware Is Back on the Rise As Cybercriminals’ Motivation Shifts to Data Exfiltration – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE SAN FRANCISCO, Jan. 30, 2024 /PRNewswire/ — Delinea, a leading provider of solutions that seamlessly extend Privileged Access Management (PAM), today published its...
Feds Confirm Remote Killing of Volt Typhoon’s SOHO Botnet – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Jeremy Walter via Alamy Stock Photo US law enforcement has disrupted the infrastructure of...
CISA Orders Ivanti VPN Appliances Disconnected: What to Do – Source: www.darkreading.com
Source: www.darkreading.com – Author: Fahmida Y. Rashid, Managing Editor, Features, Dark Reading Source: EyeEm via Alamy Stock Photo The United States Cybersecurity and Infrastructure Security Agency...
Ukraine Military Targeted With Russian APT PowerShell Attack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer Source: Design Pics Inc via Alamy Stock Photo A sophisticated Russian advanced persistent threat (APT) has launched a...
China Infiltrates US Critical Infrastructure in Ramp-up to Conflict – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: BeeBright via Shutterstock The People’s Republic of China is accelerating the development of its military capabilities —...
FritzFrog Botnet Exploits Log4Shell on Overlooked Internal Hosts – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Picture Partners via Alamy Stock Photo A new variant of an advanced botnet called “FritzFrog” has been...
The Imperative for Robust Security Design in the Health Industry – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nielet D’mello Source: Olekcii Mach via Alamy Stock Photo COMMENTARY In an era dominated by digital innovation and technological advancements, healthcare companies...