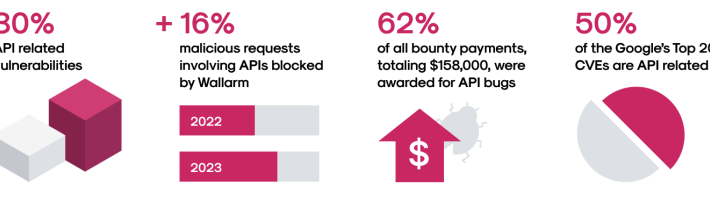
Source: securityboulevard.com – Author: girishwallarm The Wallarm Security Research team is pleased to share the latest version of our API ThreatStats report. This report serves as...
Month: January 2024
Cybersecurity Incident Shuts Down New Jersey Schools – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime Thousands of Students Forced to Stay Home Amid Cybersecurity Incident Chris Riotta (@chrisriotta) • January...
Insurance Broker Notifying 1.5 Million of Health Info Hack – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Healthcare , Incident & Breach Response , Industry Specific California Firm Said August Attack Affected Clients’ Data Marianne Kolbasuk McGee (HealthInfoSec)...
Securing Your Workforce with Datto RMM: Automating Patching, Hardening, and Backups – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
How An Ex-IRS Contractor Covertly Leaked Trump’s Tax Returns – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime Prosecutors Say Charles Littlejohn Developed ‘Detailed Plan’ to Evade Detection Chris Riotta (@chrisriotta) • January...
Italian Regulator Again Finds Privacy Problems in OpenAI – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development ChatGPT Maker Has 30 Days to Respond Akshaya Asokan (asokan_akshaya)...
Keenan & Associates Reports Data Breach Exposing Social Security Numbers of More Than 1.5M – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE MARLTON, N.J., Jan. 29, 2024 /PRNewswire/ — Approximately 1.5 million consumers are being notified that their Social Security numbers and other confidential information were compromised...
PoC Exploits Heighten Risks Around Critical New Jenkins Vuln – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: TippaPatt via Shutterstock Some 45,000 Internet-exposed Jenkins servers remain unpatched against a critical, recently disclosed arbitrary file-read...
SolarWinds Files Motion to Dismiss SEC Lawsuit – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading 2 Min Read Source: Maurice Norbert via Alamy Stock Photo In a new filing with the US...
Iran’s ‘Cyber Centers’ Dodge Sanctions to Sell Cyber Operations – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Gago Design via Shutterstock Public records combined with documents leaked by Iranian anti-government groups suggest that several...
New Jersey School District Shut Down by Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading 1 Min Read Source: Sean Pavone via Alamy Stock Photo On Jan. 28, the Freehold Township...
Top 3 Data Breaches of 2023, and What Lies Ahead in 2024 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Gad Rosenthal Source: Anthony Brown via Alamy Stock Photo COMMENTARY The migration to the cloud, coupled with the rise of artificial intelligence...
Israeli Government: Smallest of SMBs Hit Hardest in Cyberattacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Hakan Gider via Alamy Stock Photo Some 33,000 small and medium-size businesses in Israel experienced some form of...
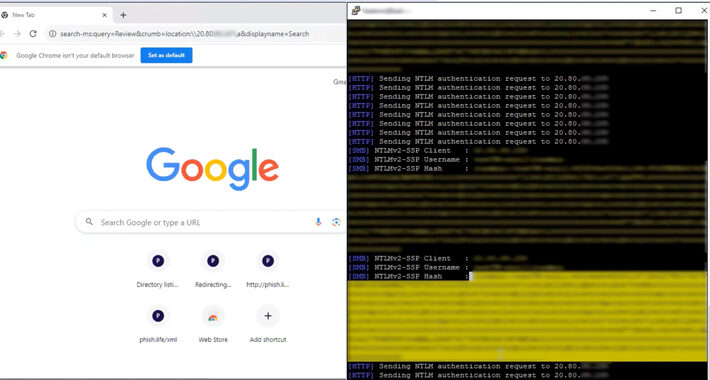
Researchers Uncover How Outlook Vulnerability Could Leak Your NTLM Passwords – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 29, 2024NewsroomVulnerability / NTML Security A now-patched security flaw in Microsoft Outlook could be exploited by threat actors to access...
493 Companies Share Their SaaS Security Battles – Get Insights in this Webinar – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 29, 2024The Hacker NewsSaaS Security / Webinar In today’s digital world, security risks are more prevalent than ever, especially when...
Albabat, Kasseika, Kuiper: New Ransomware Gangs Rise with Rust and Golang – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 29, 2024NewsroomRansomware / Malware Cybersecurity researchers have detected in the wild yet another variant of the Phobos ransomware family known...
Ransomware’s Impact Could Include Heart Attacks, Strokes & PTSD – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Cedric Pernet Ransomware incidents cause significant harm at many levels, including to physical and mental health; new research from U.K. security think...
Phobos Ransomware Family Expands With New FAUST Variant – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security researchers have recently uncovered a new variant of the notorious Phobos ransomware family named FAUST. Phobos, which first emerged in...
US Senator Exposes NSA Purchase of Americans’ Internet Records – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 US Senator Ron Wyden of Oregon has unveiled documents last week substantiating claims that the National Security Agency (NSA) is actively...
Nigerian ‘Yahoo Boys’ Behind Social Media Sextortion Surge in the US – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Teenagers from Western English-speaking countries are increasingly targeted by financial sextortion attacks conducted by Nigeria-based cybercriminals, the Network Contagion Research Institute...
Microsoft Provides Defense Guidance After Nation-State Compromise – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Microsoft has provided new details for responders to the Russian nation-state attack that compromised its systems earlier in January, and issued...
Dark Web Drugs Vendor Forfeits $150m After Guilty Plea – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A prolific dark web drugs vendor has pleaded guilty and agreed to forfeit $150m, the largest single seizure ever taken by...
CI/CD at Risk as Exploits Released For Critical Jenkins Bug – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Software developers have been told to urgently patch their Jenkins servers after exploits were published for a new critical vulnerability in...
Experts detailed Microsoft Outlook flaw that can leak NTLM v2 hashed passwords – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Experts detailed Microsoft Outlook flaw that can leak NTLM v2 hashed passwords A flaw in Microsoft Outlook can be exploited...
NSA buys internet browsing records from data brokers without a warrant – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini NSA buys internet browsing records from data brokers without a warrant The U.S. National Security Agency (NSA) admitted to buying...
Ukraine’s SBU arrested a member of Pro-Russia hackers group ‘Cyber Army of Russia’ – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Ukraine’s SBU arrested a member of Pro-Russia hackers group ‘Cyber Army of Russia’ Ukraine’s security service, the SBU, announced that it...
Multiple PoC exploits released for Jenkins flaw CVE-2024-23897 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Multiple PoC exploits released for Jenkins flaw CVE-2024-23897 Multiple proof-of-concept (PoC) exploits for recently disclosed critical Jenkins vulnerability CVE-2024-23897 have...
NSA Admits Secretly Buying Your Internet Browsing Data without Warrants – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 29, 2024NewsroomSurveillance / Data Privacy The U.S. National Security Agency (NSA) has admitted to buying internet browsing records from data...
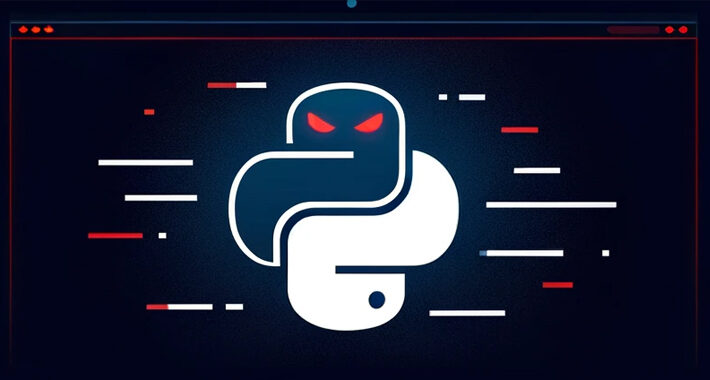
Malicious PyPI Packages Slip WhiteSnake InfoStealer Malware onto Windows Machines – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 29, 2024NewsroomPyPI Repository / Malware Cybersecurity researchers have identified malicious packages on the open-source Python Package Index (PyPI) repository that...
Exploits released for critical Jenkins RCE flaw, patch now – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Multiple proof-of-concept (PoC) exploits for a critical Jenkins vulnerability allowing unauthenticated attackers to read arbitrary files have been made publicly...