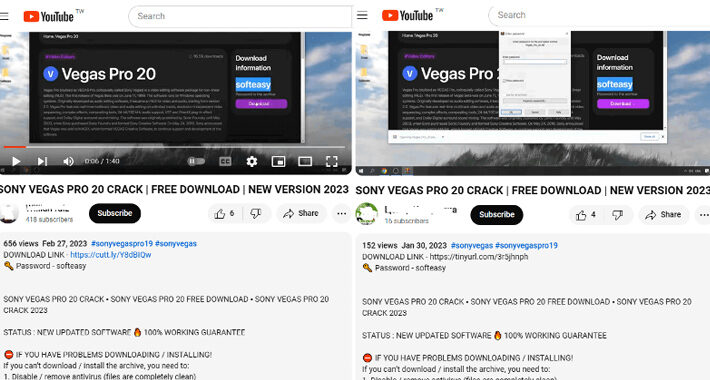
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Linaiimages via Shutterstock Attackers have been spreading a variant of the Lumma Stealer via YouTube channels that...
Month: January 2024
It’s Time to Close the Curtain on Security Theater – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jason Rebholz Source: Brownstock via Alamy Stock Photo COMMENTARY Another day, another ransomware attack or security breach at a brand-name company. And that’s just...
TitanHQ Launches PhishTitan to Combat Advanced Phishing Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE GALWAY, Ireland & SHELTON, Conn., Jan. 09, 2024 (NEWSWIRE) — TitanHQ, the leading cloud-based email security solutions provider for over...
Chertoff Group Affiliate Completes Trustwave Acquisition – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Srabin via iStock MC2 Security Fund, a growth equity fund and affiliate of The Chertoff Group, has completed...
Executing Zero Trust in the Cloud Takes Strategy – Source: www.darkreading.com
Source: www.darkreading.com – Author: Glen Pendley Source: ArtemisDiana via Alamy Stock Photo Zero trust is a high-level strategy that assumes that individuals, devices, and services attempting...
Award Winning Antivirus, On Sale for $25, Offers Elite Protection from Malware – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Academy Published January 9, 2024 Updated January 8, 2024 We may earn from vendors via affiliate links or sponsorships. This might...
The best Windows 11 features added in 2023 – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Mayank Parmar The year 2023 marks a significant milestone for Windows 11 with the introduction of several new features and improvements. This...
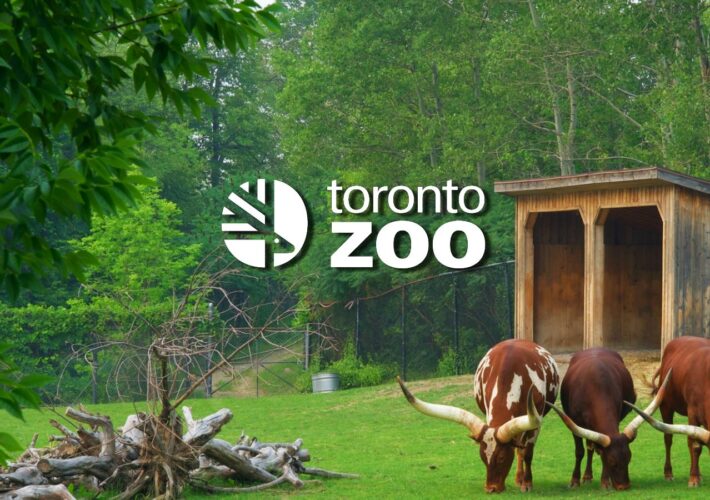
Toronto Zoo: Ransomware attack had no impact on animal wellbeing – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Toronto Zoo, the largest zoo in Canada, says that a ransomware attack that hit its systems on early Friday had...
Netgear, Hyundai latest X accounts hacked to push crypto drainers – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The official Netgear and Hyundai MEA Twitter/X accounts (together with over 160,000 followers) are the latest hijacked to push scams...
Turkish hackers Sea Turtle expand attacks to Dutch ISPs, telcos – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The Turkish state-backed cyber espionage group tracked as Sea Turtle has been carrying out multiple spying campaigns in the Netherlands, focusing...
Twilio will ditch its Authy desktop 2FA app in August, goes mobile only – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The Authy desktop apps for Windows, macOS, and Linux will be discontinued in August 2024, with the company recommending users...
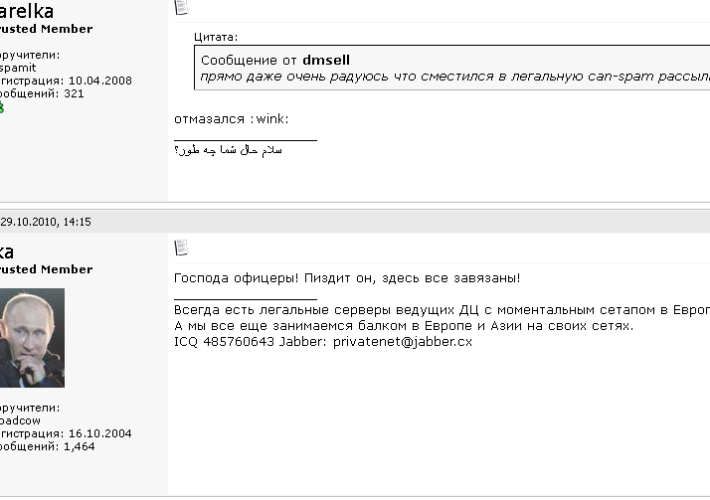
Meet Ika & Sal: The Bulletproof Hosting Duo from Hell – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs In 2020, the United States brought charges against four men accused of building a bulletproof hosting empire that once dominated the...
Alert: New Vulnerabilities Discovered in QNAP and Kyocera Device Manager – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 09, 2024NewsroomNetwork Security / Data Protection A security flaw has been disclosed in Kyocera’s Device Manager product that could be...
Beware! YouTube Videos Promoting Cracked Software Distribute Lumma Stealer – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 09, 2024NewsroomMalware / Cyber Threat Threat actors are resorting to YouTube videos featuring content related to cracked software in order...
Guide to Malware Incident Prevention and Handling for Desktops and Laptops
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
LLM AI Security & Governance Checklist
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
IT AUDIT CHECKLIST
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Kubernetes Exploitation Introduction -Cheatsheet #1
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Incident Response Playbook: Dark Web Breaches
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Life in the Swimlane with Principal Data Scientist, Dima Skorokhodov – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kelly Dougherty Welcome to the “Life in the Swimlane” blog series. Here we will feature interviews with Swimlaners to learn more about...
Ditch the Passwords: Discover the Magic of WebAuthn and Passkeys – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepak Gupta – Tech Entrepreneur, Cybersecurity Author In today’s digital age, passwords have become a necessary evil. We rely on them to...
USENIX Security ’23 – ‘Know Your Cybercriminal: Evaluating Attacker Preferences by Measuring Profile Sales on an Active, Leading Criminal Market for User Impersonation at Scale’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters: Michele Campobasso, Luca Allodi Many thanks to USENIX for publishing their outstanding USENIX Security ’23 Presenter’s content, and the...
The CISO’s Guide to a Modern GRC Program with Trust Assurance – Source: securityboulevard.com
Source: securityboulevard.com – Author: Erin Crapser The position of CISO is not an enviable one. Modern CISOs face enormous challenges like managing the complexity of on-prem...
Mastering the ‘cd’ Command: Tips and Tricks for Efficient Directory Navigation – Source: securityboulevard.com
Source: securityboulevard.com – Author: CyB3rBEA$T Navigating through directories is a fundamental aspect of working in a command-line interface, and the ‘cd’ command plays a crucial role...
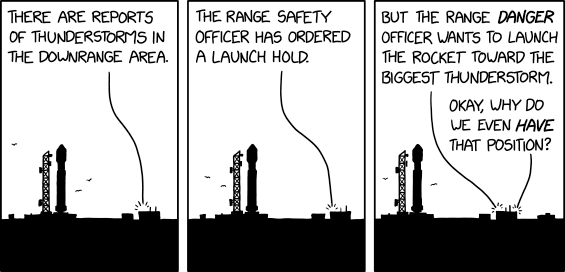
Randall Munroe’s XKCD ‘Range Safety’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman No one specifically Someone on our general security team A dedicated person/team that handles cloud security Cloud architects and developers...
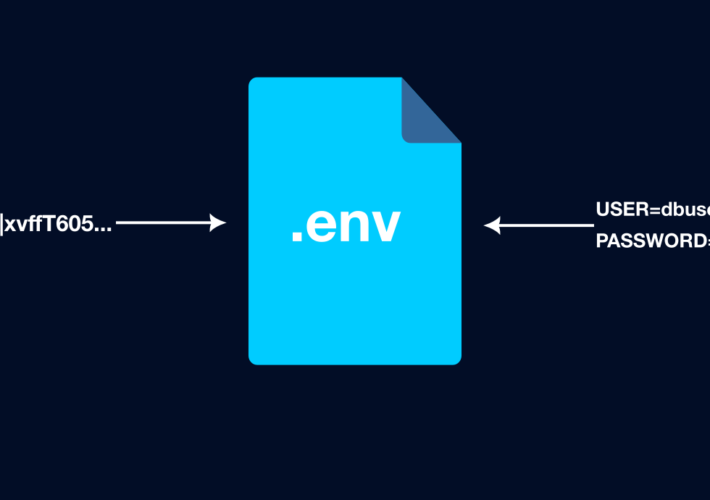
Secure Your Secrets with .env – Source: securityboulevard.com
Source: securityboulevard.com – Author: Greg Bulmash Using environment variables to store secrets instead of writing them directly into your code is one of the quickest and...
NIST: Better Defenses are Needed for AI Systems – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt The accelerating development and expanding deployment of AI systems is creating significant security and privacy risks that aren’t being mitigated...
NIS2 Compliance: Updated for 2024, Complete Guide – Source: securityboulevard.com
Source: securityboulevard.com – Author: Flare The Network Information Systems Directive (NIS) was published in 2016 and required EU critical infrastructure sectors to meet basic cybersecurity compliance...
USENIX Security ’23 – Zixin Wang, Danny Yuxing Huang, Yaxing Yao – ‘Exploring Tenants’ Preferences of Privacy Negotiation in Airbnb’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman No one specifically Someone on our general security team A dedicated person/team that handles cloud security Cloud architects and developers...
NYS: Clinic Must Pay $450K Fine, Spend $1.2M on Security – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Healthcare , Industry Specific State AG Settlement Comes After 2021 Lorenz Ransomware Attack on Health Center...