Source: securityboulevard.com – Author: Richi Jennings Under active exploitation since last year—but still no patch available. A critical zero-day and another high-severity CVE are being chained together to...
Month: January 2024
CISA ROADMAP FOR ARTIFICIAL INTELLIGENCE
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Catalogue of security measures GDPR
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Web ApplicationPenetration TestingTraining
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Boardroom Guide on Cybersecurity Governance and SEC info
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Amazon Appeals Privacy Fine of 746 Million Euros – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 General Data Protection Regulation (GDPR) , Standards, Regulations & Compliance E-Commerce Giant Accuses Luxembourg Regulators of Attacking the Company Akshaya Asokan...
Chinese Nation-State Hacker Is Exploiting Cisco Routers – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Governance & Risk Management ‘Volt Typhoon’ Could Be Preparing for Renewed...
Live Webinar | Cybersecurity Strategies for Resource-Constrained State and Local Governments – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Jamie Tomasello Managing Director, Superbloom Jamie Tomasello (she/her and he/him) is a technology and policy leader with a strategic focus on...
US CISA Must Improve Water Sector Assistance, Says Watchdog – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Critical Infrastructure Security DHS Office of Inspector General Finds Lack of Coordination With EPA David Perera (@daveperera) • January 12, 2024...
Fertility Test Lab Will Pay $1.25M to Settle Breach Lawsuit – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Healthcare , Industry Specific , Legislation & Litigation ReproSource Also Agrees to Beef Up Security in Wake of 2021 Ransomware Attack...
Nation-State Actors Weaponize Ivanti VPN Zero-Days, Deploying 5 Malware Families – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 12, 2024NewsroomVulnerability / Threat Intelligence As many as five different malware families were deployed by suspected nation-state actors as part...
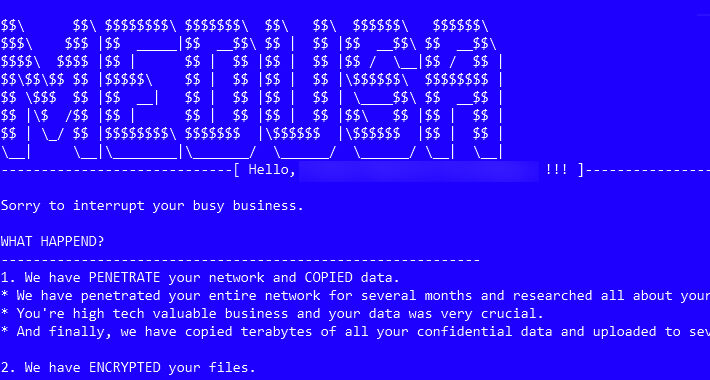
Medusa Ransomware on the Rise: From Data Leaks to Multi-Extortion – Source:thehackernews.com
Source: thehackernews.com – Author: . The threat actors associated with the Medusa ransomware have ramped up their activities following the debut of a dedicated data leak...
Applying the Tyson Principle to Cybersecurity: Why Attack Simulation is Key to Avoiding a KO – Source:thehackernews.com
Source: thehackernews.com – Author: . Picture a cybersecurity landscape where defenses are impenetrable, and threats are nothing more than mere disturbances deflected by a strong shield....
Urgent: GitLab Releases Patch for Critical Vulnerabilities – Update ASAP – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 12, 2024NewsroomDevSecOps / Software security GitLab has released security updates to address two critical vulnerabilities, including one that could be...
Brad Arkin is New Chief Trust Officer at Salesforce – Source: www.securityweek.com
Source: www.securityweek.com – Author: SecurityWeek News Veteran cybersecurity leader Brad Arkin has left Cisco and is joining Salesforce as SVP and Chief Trust Officer. The post...
Laptop Maker Framework Says Customer Data Stolen in Third-Party Breach – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Device maker Framework is notifying users that their personal information was stolen in a data breach at its external accounting...
In Other News: WEF’s Unsurprising Cybersecurity Findings, KyberSlash Cryptography Flaw – Source: www.securityweek.com
Source: www.securityweek.com – Author: SecurityWeek News Noteworthy stories that might have slipped under the radar: WEF releases a cybersecurity report with unsurprising findings, and KyberSlash cryptography...
New Class of CI/CD Attacks Could Have Led to PyTorch Supply Chain Compromise – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Researchers detail a CI/CD attack leading to PyTorch releases compromise via GitHub Actions self-hosted runners. The post New Class of...
Russian Hackers Likely Not Involved in Attacks on Denmark’s Critical Infrastructure – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Researchers find no direct link between Russian APT Sandworm and last year’s attacks on Denmark’s critical infrastructure. The post Russian...
Apple Patches Keystroke Injection Vulnerability in Magic Keyboard – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Apple’s latest Magic Keyboard firmware addresses a recently disclosed Bluetooth keyboard injection vulnerability. The post Apple Patches Keystroke Injection Vulnerability...
Malware Used in Ivanti Zero-Day Attacks Shows Hackers Preparing for Patch Rollout – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Ivanti zero-day vulnerabilities dubbed ConnectAround could impact thousands of systems and Chinese cyberspies are preparing for patch release. The post...
Your Cybersecurity Budget Is a Horse’s Rear End – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ira Winkler Source: neal and molly jansen via Alamy Stock Photo COMMENTARY There is a popular Internet tale that traces the design...
FBI Warns of More Election ‘Chaos’ in 2024 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jeffrey Schwartz, Contributing Writer Source: Jon Helgason via Alamy Stock Photo INTERNATIONAL CONFERENCE ON CYBER SECURITY — New York — The infrastructure...
Taking a Page From Data Scientists for Better Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Erin Hamm Source: Science History Images via Alamy Stock Photo As organizations add more cybersecurity solutions to their toolboxes, they also increase...
Claroty Welcomes Former US National Cyber Director Chris Inglis to Advisory Board – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE NEW YORK, Jan. 10, 2024 /PRNewswire/ — Claroty, the cyber-physical systems protection company, today announced the appointment of Chris Inglis, former U.S. National Cyber...
Anonymous Sudan Launches Cyberattack on Chad Telco – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Christophe Coat via Alamy Stock Photo Anonymous Sudan has hit Chad telecommunications provider Sudachad with what the threat...
Kenya Issues New Guidance for Protecting Personal Data – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: David Makings via Alamy Stock Photo Kenya’s Office of the Data Protection Commissioner (ODPC) this week issued...
Hospitals Must Treat Patient Data and Health With Equal Care – Source: www.darkreading.com
Source: www.darkreading.com – Author: Scott Allendevaux Source: Piotr Adamowicz via Alamy Stock Photo COMMENTARY Hospitals are in the crosshairs: As collectors of some of the most...
War or Cost of Doing Business? Cyber Insurers Hashing Out Exclusions – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Drugmaker Merck’s long legal battle with its insurance companies over the damages caused to its business by the...
7 Lessons Learned From Designing a DEF CON CTF – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ericka Chickowski, Contributing Writer Capture-the-flag (CTF) events are both fun and educational, providing cybersecurity professionals with a way to flex their hacking...