The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Month: January 2024
Cybersecurity Open Source Tools
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity in the UAE Public Sector
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
THE OPEN SOURCE CYBERSECURITY PLAYBOOK
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity Futures 2030
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity for Startups
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity Audit Guide
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Fortinet Security Fabric: Cybersecurity, Everywhere You Need It
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The ESSENTIAL GUIDE TO SIEM
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Windows Copilot autostart tests limited to 27″ displays or larger – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft says that tests of a controversial new Windows 11 feature that automatically opens the AI-powered Copilot assistant after Windows...
US court docs expose fake antivirus renewal phishing tactics – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas In a seizure warrant application, the U.S. Secret Service sheds light on how threat actors stole $34,000 using fake antivirus...
Microsoft working on a fix for Windows 10 0x80070643 errors – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft is working to fix a known issue causing 0x80070643 errors when installing the KB5034441 security update that patches the...
Windows SmartScreen flaw exploited to drop Phemedrone malware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A Phemedrone information-stealing malware campaign exploits a Microsoft Defender SmartScreen vulnerability (CVE-2023-36025) to bypass Windows security prompts when opening URL...
Over 178K SonicWall firewalls vulnerable to DoS, potential RCE attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Security researchers have found over 178,000 SonicWall next-generation firewalls (NGFW) with the management interface exposed online are vulnerable to denial-of-service...
Latest Adblock update causes massive YouTube performance hit – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Adblock and Adblock Plus users report performance issues on YouTube, initially blamed on Google but later determined to be an...
Hacker Behind $2 Million Cryptocurrency Mining Scheme Arrested in Ukraine – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Ukrainian authorities have arrested an individual allegedly involved in a $2 million cryptojacking operation. The post Hacker Behind $2 Million...
Information Stealer Exploits Windows SmartScreen Bypass – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Attackers exploit a recent Windows SmartScreen bypass vulnerability to deploy the Phemedrone information stealer. The post Information Stealer Exploits Windows...
GitLab Patches Critical Password Reset Vulnerability – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire GitLab has resolved a critical authentication vulnerability allowing attackers to hijack password reset emails. The post GitLab Patches Critical Password...
Cloud Server Abuse Leads to Huge Spike in Botnet Scanning – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Netscout sees over one million IPs conducting reconnaissance scanning on the web due to increase in use of cheap or...
Juniper Networks Patches Critical Remote Code Execution Flaw in Firewalls, Switches – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Juniper Networks patches over 100 vulnerabilities, including a critical flaw that can be exploited for remote code execution against firewalls...
Name That Toon: Cast Adrift – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner, Cartoonist 1 Min Read Are these people coming or going? Is the Wi-Fi here any good? And where’s Wilson? Come...
Voice Cloning with Very Short Samples – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier About Bruce Schneier I am a public-interest technologist, working at the intersection of security, technology, and people. I’ve been writing...
Upcoming Speaking Engagements – Source: www.schneier.com
Source: www.schneier.com – Author: B. Schneier About Bruce Schneier I am a public-interest technologist, working at the intersection of security, technology, and people. I’ve been writing...
High-Severity Flaws Uncovered in Bosch Thermostats and Smart Nutrunners – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 15, 2024NewsroomOperational Technology / Network Security Multiple security vulnerabilities have been disclosed in Bosch BCC100 thermostats and Rexroth NXA015S-36V-B smart...
Balada Injector Infects Over 7,100 WordPress Sites Using Plugin Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 15, 2024NewsroomWebsite Security / Vulnerability Thousands of WordPress sites using a vulnerable version of the Popup Builder plugin have been...
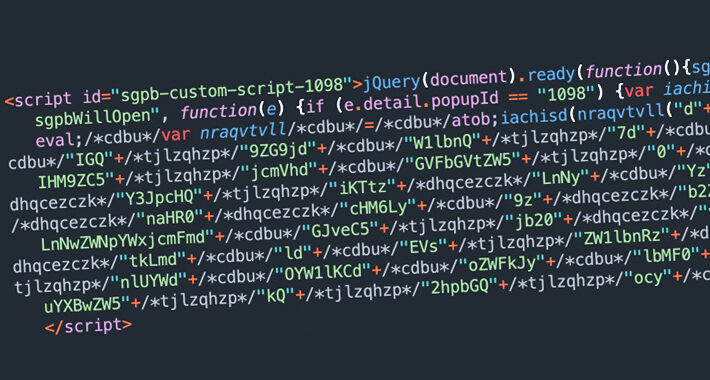
DDoS Attacks on the Environmental Services Industry Surge by 61,839% in 2023 – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 15, 2024NewsroomServer Security / Cyber Attack The environmental services industry witnessed an “unprecedented surge” in HTTP-based distributed denial-of-service (DDoS) attacks,...
Apple fixed a bug in Magic Keyboard that allows to monitor Bluetooth traffic – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Apple fixed a bug in Magic Keyboard that allows to monitor Bluetooth traffic Apple addressed a recently disclosed Bluetooth keyboard...
Attacks against Denmark ‘s energy sector were not carried out by Russia-linked APT – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Attacks against Denmark ‘s energy sector were not carried out by Russia-linked APT Forescout experts questioned the attribution of cyber...
Mastermind behind 1.8 million cryptojacking scheme arrested in Ukraine – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Mastermind behind 1.8 million cryptojacking scheme arrested in Ukraine The National Police of Ukraine, with the support of Europol, arrested...
The new Windows 11 features coming in 2024 – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Mayank Parmar Windows 11 is gearing up to introduce an array of exciting new features in 2024 aimed at enhancing user experience...