Source: www.bleepingcomputer.com – Author: Bill Toulas Atlassian Confluence Data Center and Confluence Server are vulnerable to a critical remote code execution (RCE) vulnerability that impacts versions...
Month: January 2024
Ivanti Connect Secure zero-days now under mass exploitation – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Two zero-day vulnerabilities affecting Ivanti’s Connect Secure VPN and Policy Secure network access control (NAC) appliances are now under mass...
Comprehensive Guide to Patch Management Templates – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Gabriella Antal We all know that maintaining up-to-date systems is crucial. Patch management plays a vital role in this process. This article...
How to Create an End-to-End Privileged Access Management Lifecycle – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Cristian Neagu Key takeaways: Why privileged access management requires a continuous approach; The common pitfalls of poor privileged access management; How to...
Framework Discloses Data Breach After Third-Party Got Phished – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Cristian Neagu Framework Computer announced the discovery of a data breach that exposed the private data of an unspecified number of its...
Google Workspace: Cybersecurity Friend or Foe? – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Vladimir Unterfingher Kevin Mitnick, once dubbed the World’s Most Famous Hacker said that “hackers are breaking the systems for profit. Before, it...
Sea Turtle Hackers Spy on Dutch ISPs and Telecommunication Companies – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși Sea Turtle Turkish state-backed group changed to focus on internet service providers (ISPs), telcos, media, and Kurdish websites. Sea Turtle...
Turkish Hackers Target Microsoft SQL Servers with Mimic Ransomware – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși Threat actors use AnyDesk to install Mimic ransomware and exploit poorly configured MSSQL database servers. Security researchers dubbed this ransomware campaign...
Managed Service Provider (MSP) Best Practices: A Insider’s Guide – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Madalina Popovici MSPs have carved their way into the business environment by offering a unique value proposition: by managing a wide range...
2024 Cybertrends with Morten (A Cybersecurity CEO) – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Cristian Neagu In a recent insightful discussion with Morten, CEO of Heimdal®, we explored the key cybersecurity trends for 2024. From the...
Protecting MSPs and Mid-Market Companies from ‘FalseFont’ Backdoor Attacks – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Adelina Deaconu A new backdoor, known as “FalseFont”, has been discovered and attributed to the Iranian hacking group Peach Sandstorm. As a...
The Story of the Mirai Botnet – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments Chris Becke • January 16, 2024 8:18 AM I do like how it gave me ~2m to read...
As Enterprise Cloud Grows, So Do Challenges – Source: www.darkreading.com
Source: www.darkreading.com – Author: Joshua Goldfarb Source: winter via Alamy Stock Photo As the saying goes, “little kids, little problems; big kids, big problems.” Indeed, as...
Weekly Update 382 – Source: www.troyhunt.com
Source: www.troyhunt.com – Author: Troy Hunt Geez it’s nice to be back in Oslo! This city has such a special place in my heart for so...
Case Study: The Cookie Privacy Monster in Big Global Retail – Source:thehackernews.com
Source: thehackernews.com – Author: . Explore how an advanced exposure management solution saved a major retail industry client from ending up on the naughty step due...
Inferno Malware Masqueraded as Coinbase, Drained $87 Million from 137,000 Victims – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 16, 2024NewsroomCryptocurrency / Cyber Threat The operators behind the now-defunct Inferno Drainer created more than 16,000 unique malicious domains over...
Hackers Weaponize Windows Flaw to Deploy Crypto-Siphoning Phemedrone Stealer – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 16, 2024NewsroomCryptocurrency / Windows Security Threat actors have been observed leveraging a now-patched security flaw in Microsoft Windows to deploy...
Heartless scammers prey on hundreds of lost pet owners, demanding ransoms or else… – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley Hundreds of pet owners across the UK have reported that they have received blackmail threats from scammers who claim to...
Critical flaw found in WordPress plugin used on over 300,000 websites – Source: www.tripwire.com
Source: www.tripwire.com – Author: Graham Cluley A WordPress plugin used on over 300,000 websites has been found to contain vulnerabilities that could allow hackers to seize...
Over 178,000 SonicWall next-generation firewalls (NGFW) online exposed to hack – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Over 178,000 SonicWall next-generation firewalls (NGFW) online exposed to hack Researchers from Bishop Fox found over 178,000 SonicWall next-generation firewalls...
Phemedrone info stealer campaign exploits Windows smartScreen bypass – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Phemedrone info stealer campaign exploits Windows smartScreen bypass Threat actors exploit a recent Windows SmartScreen bypass flaw CVE-2023-36025 to deliver...
Balada Injector continues to infect thousands of WordPress sites – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Balada Injector continues to infect thousands of WordPress sites Balada Injector malware infected more than 7100 WordPress sites using a...
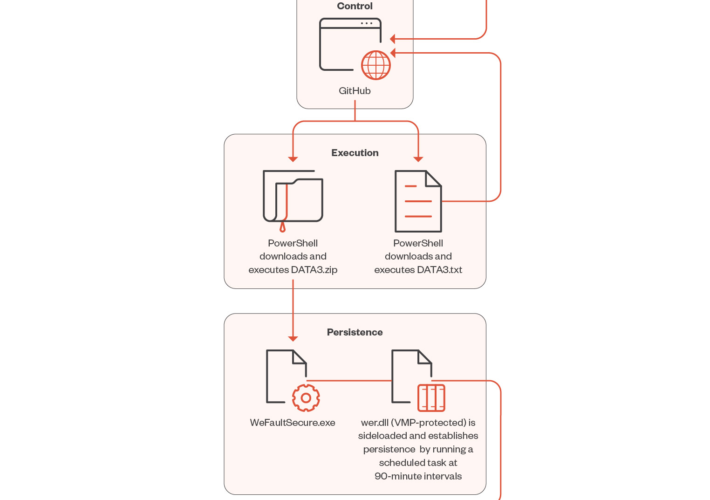
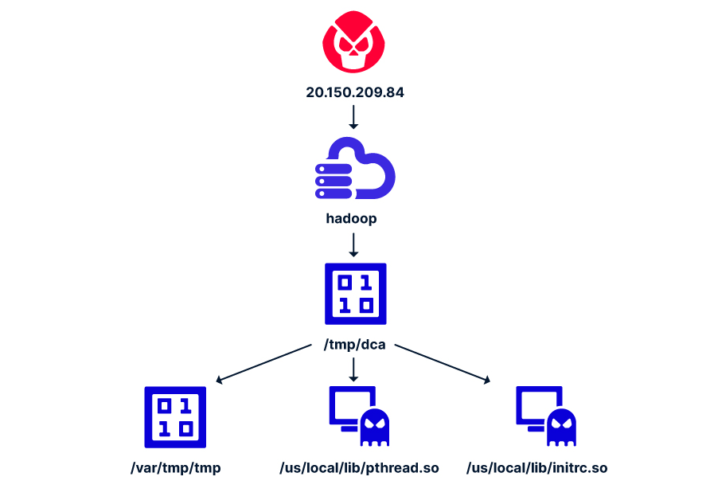
Attackers target Apache Hadoop and Flink to deliver cryptominers – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Attackers target Apache Hadoop and Flink to deliver cryptominers Researchers devised a new attack that exploits misconfigurations in Apache Hadoop...
SOC ANALYST SERIES
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Detecting the Unknown: A Guide to Threat Hunting
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
THREAT HUNTING MALWARE INFRASTRUCTURE
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
TOP ASIA/APAC CYBERSECURITY THREATS OF 2023
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Infra Pentest Course
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Information security aspects of Industrial Control Systems
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Compression Methods
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...