Source: securityboulevard.com – Author: Vikas Shetty Thanks to various 2023 security reports, we know phishing attacks are now the most common form of cybercrime, with an...
Month: January 2024
Comic Agilé – Mikkel Noe-Nygaard, Luxshan Ratnaravi – #275 — Comic Agilé Consulting – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Wednesday, January 17, 2024 Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News...
News alert: Incogni study reveals overwhelming majority of spam calls originate locally – Source: securityboulevard.com
Source: securityboulevard.com – Author: bacohido Los Angeles, Calif., Jan. 17, 2024 – Spam calls continue to be a major nuisance in the US, and advice on...
US Judge Again Says Meta Pixel Privacy Case Dismissal Unlikely – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Legislation & Litigation , Privacy Case Against Meta Likely Moving Forward After Court Heard Dismissal Arguments...
How a Novel Legal Maneuver Got a Hospital’s Stolen Data Back – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 The ubiquity and anonymity of cryptocurrencies are fueling economic, legal and ethical challenges that put healthcare entities in the crosshairs of...
Chinese Drones Pose Threat to US Infrastructure, CISA Warns – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Critical Infrastructure Security CISA, FBI Urge Critical Infrastructure Owners to Bolster UAS Security Measures Chris Riotta (@chrisriotta) • January 17, 2024...
Chrome Patches First Zero-Day of 2024 Exploited in the Wild – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Google Fixes Out-of-Bounds Memory Access Flaw, Microsoft Edge Browser Also Affected Mihir Bagwe (MihirBagwe) • January 17, 2024 Google...
OpenAI Combats Election Misinformation Amid Growing Concerns – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Government , Industry Specific ChatGPT Maker Wants to Deter Use of AI in Online Election...
Mimecast Announces New CEO – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE LEXINGTON, Mass., January 16, 2024 – Mimecast Limited (Mimecast), an advanced email and collaboration security company, announced today the appointment of Marc van Zadelhoff as...
ESET Launches New Managed Detection and Response (MDR) Service for Small and Midsize Businesses – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE BRATISLAVA/SAN DIEGO — January 17, 2024 — ESET, a global leader in cybersecurity, has announced the launch of ESET MDR, an...
Intel 471 Appoints Technology Veteran, Sonja Tsiridis, Chief Technology Officer – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE WILMINGTON, Del.- Intel 471, a premier provider of cyber threat intelligence (CTI) solutions across the globe, announced Sonja Tsiridis as its...
$80M in Crypto Disappears into Drainer-as-a-Service Malware Hell – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Peter Horree via Alamy Stock Photo A sophisticated phishing campaign dubbed “Inferno Drainer” has...
Google Chrome Zero-Day Bug Under Attack, Allows Code Injection – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Wachiwit via Shutterstock Google has patched a high-severity zero-day bug in its Chrome Web browser that attackers...
Experts Ponder Effectiveness of Official Warnings of Cyber Scams – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Source: Mohd Izzuan Roslan via Alamy Stock Photo The Dubai Police, from the United Arab Emirates,...
‘Punchmade Dev’ Cybercrime Rapper Launches Cash-Scamming Web Shop – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Albert Shakirov via Alamy Stock Photo Punchmade Dev — a rapper, producer, and investor known for his music...
CISA: AWS, Microsoft 365 Accounts Under Active ‘Androxgh0st’ Attack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: GagoDesign via Shutterstock The FBI and the US Cybersecurity and Infrastructure Security Agency (CISA) have issued an...
Q&A: How One Company Gauges Its Employees’ Cybersecurity ‘Fluency’ – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Source: Svyatoslav Lypynskyy via Alamy Stock Photo Professional services firm TAG.Global now requires that all of...
5 Best VPNs for Android in 2024 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Luis Millares We may earn from vendors via affiliate links or sponsorships. This might affect product placement on our site, but not...
SMB Security Pack – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Small and midsize businesses are increasingly being targeted by cybercriminals — but they often lack the resources and expertise to develop comprehensive...
Transmission of Sensitive Data Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Data in transit means data is at risk if the proper precautions aren’t followed. Data stored inside a securely monitored environment is...
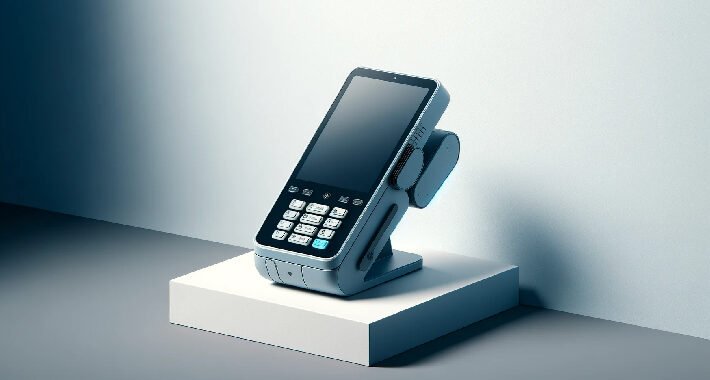
PAX PoS Terminal Flaw Could Allow Attackers to Tamper with Transactions – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 17, 2024NewsroomFinancial Data / Vulnerability The point-of-sale (PoS) terminals from PAX Technology are impacted by a collection of high-severity vulnerabilities...
Combating IP Leaks into AI Applications with Free Discovery and Risk Reduction Automation – Source:thehackernews.com
Source: thehackernews.com – Author: . Wing Security announced today that it now offers free discovery and a paid tier for automated control over thousands of AI...
Code Written with AI Assistants Is Less Secure – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier Interesting research: “Do Users Write More Insecure Code with AI Assistants?“: Abstract: We conduct the first large-scale user study examining...
Dark web threats and dark market predictions for 2024 – Source: securelist.com
Source: securelist.com – Author: Sergey Lozhkin, Anna Pavlovskaya, Kaspersky Security Services Kaspersky Security Bulletin An overview of last year’s predictions Increase in personal data leaks; corporate...
Atlassian Warns of Critical RCE Vulnerability in Outdated Confluence Instances – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Out-of-date Confluence Data Center and Server instances are haunted by a critical vulnerability leading to remote code execution. The post...
AI Data Exposed to ‘LeftoverLocals’ Attack via Vulnerable AMD, Apple, Qualcomm GPUs – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Researchers show how a new attack named LeftoverLocals, which impacts GPUs from AMD, Apple and Qualcomm, can be used to...
Achieving “Frictionless Defense” in the Age of Hybrid Networks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Matt Wilson A “frictionless defense” is about integrating security measures seamlessly into the digital landscape to safeguard against threats while ensuring a...
GitHub Rotates Credentials in Response to Vulnerability – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire GitHub rotates credentials and releases patches after being alerted of a vulnerability affecting GitHub.com and GitHub Enterprise Server. The post...
Here’s How ChatGPT Maker OpenAI Plans to Deter Election Misinformation in 2024 – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press ChatGPT maker OpenAI outlines a plan to prevent its tools from being used to spread election misinformation in 2024. The...
Oracle Patches 200 Vulnerabilities With January 2024 CPU – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Oracle releases 389 new security patches to address 200 vulnerabilities as part of the first Critical Patch Update of 2024....