Source: thehackernews.com – Author: . Jan 23, 2024NewsroomCyber Crime / Dark Web Conor Brian Fitzpatrick has been sentenced to time served and 20 years of supervised...
Month: January 2024
~40,000 Attacks in 3 Days: Critical Confluence RCE Under Active Exploitation – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 23, 2024NewsroomVulnerability / Cyber Attack Malicious actors have begun to actively exploit a recently disclosed critical security flaw impacting Atlassian...
Apple Issues Patch for Critical Zero-Day in iPhones, Macs – Update Now – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 23, 2024NewsroomVulnerability / Device Security Apple on Monday released security updates for iOS, iPadOS, macOS, tvOS, and Safari web browser...
Apple Ships iOS 17.3, Warns of WebKit Zero-Day Exploitation – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Apple pushes out fresh versions of its iOS and macOS platforms to fix WebKit vulnerabilities being exploited as zero-day in...
Security Experts Describe AI Technologies They Want to See – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine SecurityWeek interviews a wide spectrum of security experts on AI-driven cybersecurity use-cases that are worth immediate attention. The post Security...
Hackers Targeting Critical Atlassian Confluence Vulnerability Days After Disclosure – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The Atlassian Confluence vulnerability CVE-2023-22527 is being exploited in the wild just days after it was disclosed. The post Hackers...
LoanDepot Breach: 16.6 Million People Impacted – Source: www.securityweek.com
Source: www.securityweek.com – Author: SecurityWeek News Lending giant LoanDepot (NYSE: LDI) said that roughly 16.6 million individuals were impacted as a result of a ransomware attack....
New NTLM Hash Leak Attacks Target Outlook, Windows Programs – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Varonis finds one vulnerability and three attack methods that can be used to obtain NTLM hashes via Outlook and two...
Owner of Cybercrime Website BreachForums Sentenced to Supervised Release – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Conor Brian Fitzpatrick, the owner of the cybercrime website BreachForums, was sentenced to time served and supervised release. The post...
Chinese Spies Exploited VMware vCenter Server Vulnerability Since 2021 – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire CVE-2023-34048, a vCenter Server vulnerability patched in October 2023, had been exploited as zero-day for a year and a half....
France Fines Yahoo 10 Mn Euros Over Cookie Abuses – Source: www.securityweek.com
Source: www.securityweek.com – Author: AFP France’s data protection watchdog fines Yahoo 10 million euros for not respecting users’ refusals of internet-tracking “cookies” The post France Fines...
AI Bots on X (Twitter) – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments Tom • January 22, 2024 8:12 AM Something I’ve been expecting to see for a while now is...
Amy Farrow Joins Infoblox As Chief Information Officer – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE SANTA CLARA, Calif., Jan. 22, 2024 /PRNewswire/ — Infoblox Inc., a leader in cloud networking and security services, today announces the appointment of Amy...
F5 Welcomes Samir Sherif As New Chief Information Security Officer – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE SEATTLE – F5 (NASDAQ: FFIV), today announced the appointment of Samir Sherif as Senior Vice President and Chief Information Security...
National Cybersecurity Alliance Announces 2024 Data Privacy Week – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE WASHINGTON (January 22, 2024) – Today, the National Cybersecurity Alliance (NCA), announced the program for its third annual Data Privacy Week campaign,...
Godzilla Web Shell Attacks Stomp on Critical Apache ActiveMQ Flaw – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Chris Willson via Alamy Stock Photo Threat actors have unleashed a fresh wave of cyberattacks targeting a...
Chinese Spies Exploited Critical VMware Bug for Nearly 2 Years – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: rafapress via Shutterstock One of the most serious VMware vulnerabilities in recent memory was secretly being exploited...
Microsoft Falls Victim to Russia-Backed ‘Midnight Blizzard’ Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading 2 Min Read Source: Robert K. Chin – Storefronts via Alamy Stock Photo Microsoft’s corporate systems were...
North Korea’s ScarCruft Attackers Gear Up to Target Cybersecurity Pros – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Cavan Images via Alamy Stock Photo ScarCruft, the North Korea-sponsored advanced persistent threat (APT)...
German IT Consultant Fined Thousands for Reporting Security Failing – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading 1 Min Read Source: Andriy Popov via Alamy Stock Photo After discovering and reporting a vulnerability...
Israel, Czech Republic Reinforce Cyber Partnership Amid Hamas War – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: lunewind via Alamy Stock Photo The director general of the Israel National Cyber Directorate (INCD) has signed a...
Battling Misinformation During Election Season – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ben Sebree Source: Saphiens via Alamy Stock Photo COMMENTARY The 2024 US election season is upon us, bringing a surge of political...
How to Use Context-Based Authentication to Improve Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Shelley Leveson, Director of Content Marketing, HYPR One of the biggest security weak points for organizations involves their authentication processes. According to...
News alert: Deloitte, Memcyco partner to deliver real-time ‘digital impersonation’ solutions – Source: securityboulevard.com
Source: securityboulevard.com – Author: bacohido New York, NY, Jan. 22, 2024 —Memcyco Inc, the real-time digital impersonation detection and prevention solution provider, and Deloitte, the leading...
USENIX Security ’23 – Ding Wang, Xuan Shan, Qiying Dong, Yaosheng Shen, Chunfu Jia – No Single Silver Bullet: Measuring the Accuracy of Password Strength Meters – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Identity & Access Network Security Security Bloggers Network Home » Cybersecurity » Network Security » USENIX Security ’23 – Ding Wang, Xuan...
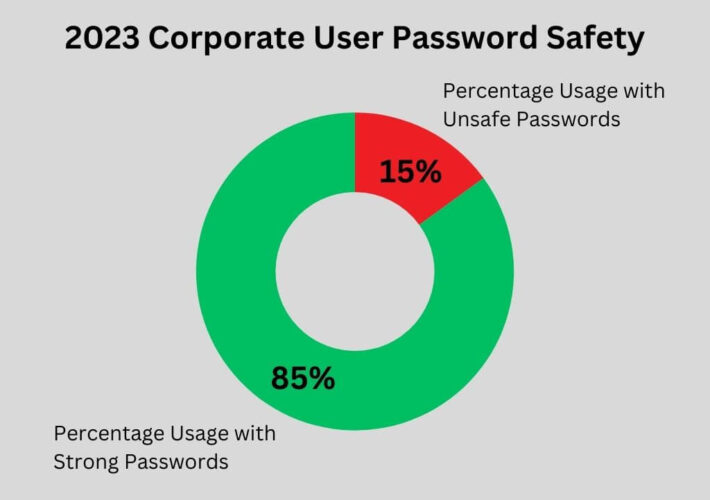
Enzoic for AD Lite Data Shows Increase in Crucial Risk Factors – Source: securityboulevard.com
Source: securityboulevard.com – Author: Enzoic The 2023 data from Enzoic for Active Directory Lite (also known as Enzoic for AD Lite) data from 2023 offers a...
Essential Email and Internet Safety Tips for College Students – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ahona Rudra Reading Time: 5 min Your email is one of the most important digital assets and identities because it helps you...
Randall Munroe’s XKCD ‘Astronaut Guests’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
Deloitte Partners with Memcyco to Combat ATO and Other Online Attacks with Real-Time Digital Impersonation Protection Solutions – Source: securityboulevard.com
Source: securityboulevard.com – Author: cyberwire New York, U.S.A., January 22nd, 2024, Cyberwire Memcyco will showcase its solutions at Deloitte’s annual Cyber iCON event, demonstrating how organizations...
Chinese Espionage Group Has Exploited VMware Flaw Since 2021 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt A Chinese espionage group spotted last year by Mandiant researchers abusing a flaw that affected VMware virtualization tools has been...