The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Day: January 9, 2024
Microsoft AzureWell – Architected Framework -Security Pillar
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
BUENAS PRÁCTICAS – Medidas de ciberseguridad en vacaciones
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
DEEP LATERAL MOVEMENT IN OT NETWORKS: When Is a Perimeter Not a Perimeter?
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Information Security Management System Gap Analysis Checklist
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
10 Ways to Detect a Phishing Email
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Mastering Impact with Sharpening Techniques (RTC0026)
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
5ghoul
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Bangladesh Election App Crashes Amid Suspected Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: sleepyfellow via Alamy Stock Photo Ukraine and Germany have been accused of waging a cyberattack to crash an...
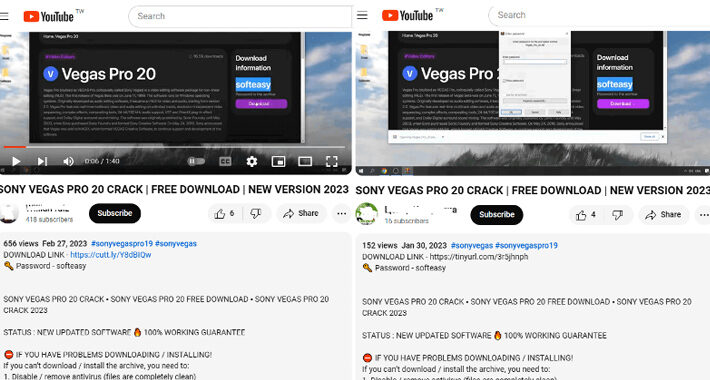
Beware Weaponized YouTube Channels Spreading Lumma Stealer – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Linaiimages via Shutterstock Attackers have been spreading a variant of the Lumma Stealer via YouTube channels that...
It’s Time to Close the Curtain on Security Theater – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jason Rebholz Source: Brownstock via Alamy Stock Photo COMMENTARY Another day, another ransomware attack or security breach at a brand-name company. And that’s just...
TitanHQ Launches PhishTitan to Combat Advanced Phishing Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE GALWAY, Ireland & SHELTON, Conn., Jan. 09, 2024 (NEWSWIRE) — TitanHQ, the leading cloud-based email security solutions provider for over...
Chertoff Group Affiliate Completes Trustwave Acquisition – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Srabin via iStock MC2 Security Fund, a growth equity fund and affiliate of The Chertoff Group, has completed...
Executing Zero Trust in the Cloud Takes Strategy – Source: www.darkreading.com
Source: www.darkreading.com – Author: Glen Pendley Source: ArtemisDiana via Alamy Stock Photo Zero trust is a high-level strategy that assumes that individuals, devices, and services attempting...
Award Winning Antivirus, On Sale for $25, Offers Elite Protection from Malware – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Academy Published January 9, 2024 Updated January 8, 2024 We may earn from vendors via affiliate links or sponsorships. This might...
The best Windows 11 features added in 2023 – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Mayank Parmar The year 2023 marks a significant milestone for Windows 11 with the introduction of several new features and improvements. This...
Toronto Zoo: Ransomware attack had no impact on animal wellbeing – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Toronto Zoo, the largest zoo in Canada, says that a ransomware attack that hit its systems on early Friday had...
Netgear, Hyundai latest X accounts hacked to push crypto drainers – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The official Netgear and Hyundai MEA Twitter/X accounts (together with over 160,000 followers) are the latest hijacked to push scams...
Turkish hackers Sea Turtle expand attacks to Dutch ISPs, telcos – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The Turkish state-backed cyber espionage group tracked as Sea Turtle has been carrying out multiple spying campaigns in the Netherlands, focusing...
Twilio will ditch its Authy desktop 2FA app in August, goes mobile only – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The Authy desktop apps for Windows, macOS, and Linux will be discontinued in August 2024, with the company recommending users...
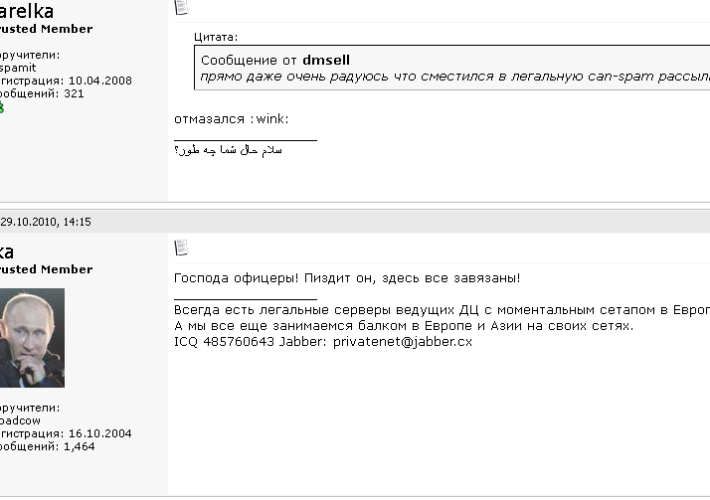
Meet Ika & Sal: The Bulletproof Hosting Duo from Hell – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs In 2020, the United States brought charges against four men accused of building a bulletproof hosting empire that once dominated the...
Alert: New Vulnerabilities Discovered in QNAP and Kyocera Device Manager – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 09, 2024NewsroomNetwork Security / Data Protection A security flaw has been disclosed in Kyocera’s Device Manager product that could be...
Beware! YouTube Videos Promoting Cracked Software Distribute Lumma Stealer – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 09, 2024NewsroomMalware / Cyber Threat Threat actors are resorting to YouTube videos featuring content related to cracked software in order...
Guide to Malware Incident Prevention and Handling for Desktops and Laptops
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
LLM AI Security & Governance Checklist
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
IT AUDIT CHECKLIST
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Kubernetes Exploitation Introduction -Cheatsheet #1
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Incident Response Playbook: Dark Web Breaches
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Life in the Swimlane with Principal Data Scientist, Dima Skorokhodov – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kelly Dougherty Welcome to the “Life in the Swimlane” blog series. Here we will feature interviews with Swimlaners to learn more about...
Ditch the Passwords: Discover the Magic of WebAuthn and Passkeys – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepak Gupta – Tech Entrepreneur, Cybersecurity Author In today’s digital age, passwords have become a necessary evil. We rely on them to...