Source: www.darkreading.com – Author: Jeffrey Schwartz, Contributing Writer, Dark Reading Back in May 2022, Microsoft promised support for passwordless authentication using passkeys in the Windows operating...
Month: September 2023
Fortinet Announces Formation of Veterans Program Advisory Council to Narrow the Cybersecurity Skills Gap With Military Veteran Talent – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 SUNNYVALE, Calif. – Sep 27, 2023 — John Maddison, EVP of Product Strategy and CMO at Fortinet “Military veterans can be vital to...
Netscout Identified Nearly 7.9M DDOS Attacks in the First Half of 2023 – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 WESTFORD, Mass., September 26, 2023 – NETSCOUT SYSTEMS, INC., (NASDAQ: NTCT) today announced findings from its 1H2023 DDoS Threat Intelligence Report. Cybercriminals launched...
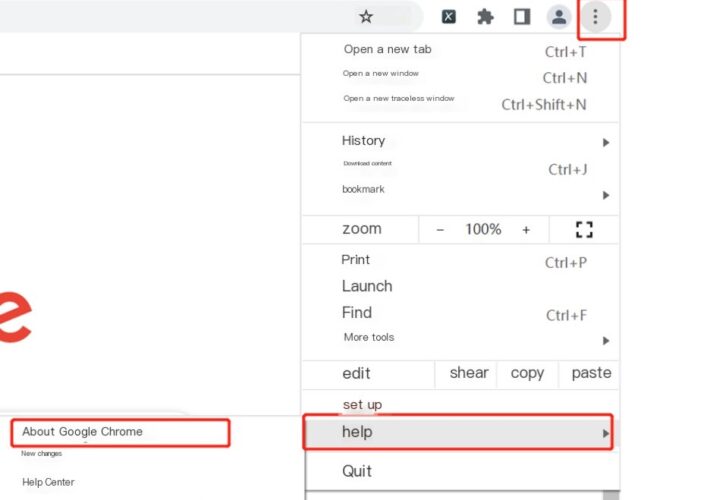
Critical Vulnerability in libwebp Library – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier Both Apple and Google have recently reported critical vulnerabilities in their systems—iOS and Chrome, respectively—that are ultimately the result of...
Researchers Release Details of New RCE Exploit Chain for SharePoint – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Researchers who discovered two critical vulnerabilities in Microsoft SharePoint Server have released details of an exploit...
China APT Cracks Cisco Firmware in Attacks Against the US and Japan – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading An old Chinese state-linked threat actor has been quietly manipulating Cisco routers to breach multinational organizations...
Microsoft Adds Passkeys to Windows 11 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading In a major update to its Windows 11 operating system this week, Microsoft has integrated Passkeys alongside...
Threat Data Feeds and Threat Intelligence Are Not the Same Thing – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kurtis Minder, Co-Founder & CEO, GroupSense In cybersecurity, “threat data feeds” and “threat intelligence” are often used interchangeably. They are, however, quite...
Hackers Trick Outlook Into Showing Fake AV Scans – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Threat actors are employing an existing technique of zero-point font obfuscation in a new way to fool...
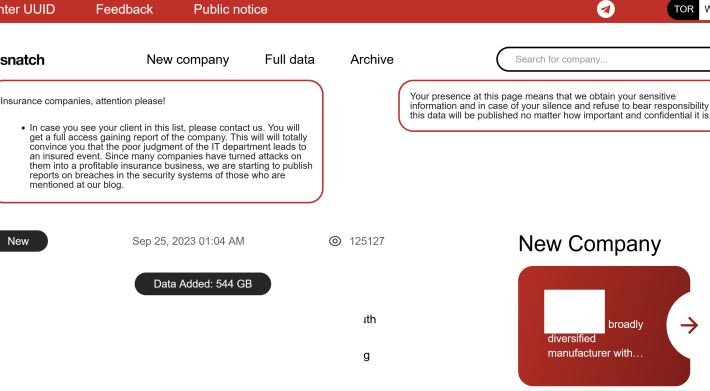
‘Snatch’ Ransom Group Exposes Visitor IP Addresses – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs The victim shaming site operated by the Snatch ransomware group is leaking data about its true online location and internal operations,...
Webinar Highlights – Mastering the new SEC Regs – Source: securityboulevard.com
Source: securityboulevard.com – Author: Gaurav Banga It was great to chat last week on the topic of the new SEC Rules with my good friend Ed...
Step on It: What to Know About TISAX Compliance in the Automotive Market – Source: securityboulevard.com
Source: securityboulevard.com – Author: Matt Kelly The automotive industry is one of the largest in the world, with sales estimated at $2.95 trillion for 2022. It’s...
Protecting Critical Infrastructure From Ransomware with LogRhythm NDR – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ianni Le A European-based organization in the transportation industry needed a way to protect its data with a solution that could mitigate...
Google LibWebP Arbitrary Code Execution Vulnerability (CVE-2023-5129) Notification – Source: securityboulevard.com
Source: securityboulevard.com – Author: NSFOCUS Overview Recently, NSFOCUS CERT found that Google officially fixed a heap buffer overflow vulnerability (CVE-2023-4863). Due to a flaw in the...
Cyber Week 2023 & The Israel National Cyber Directorate Presents – Scaling up Cyber Capacity Building: The Sectoral Approach to Critical Infrastructure Protection – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/09/cyber-week-2023-the-israel-national-cyber-directorate-presents-scaling-up-cyber-capacity-building-the-sectoral-approach-to-critical-infrastructure-protection/ Category & Tags: CISO Suite,Governance, Risk &...
ZenRAT Targets Windows Users with Fake Bitwarden Site – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Hackers are using a bogus download page for Bitwarden’s password manager solution to target Windows users with a new remote...
Meet the Ona: Stefan Popa – Source: securityboulevard.com
Source: securityboulevard.com – Author: ltabo Meet the Ona: Stefan Popa ltabo Wed, 09/27/2023 – 18:12 Today, we announced a series of strategic expansion efforts, including a...
RATs, rootkits, and ransomware (oh my!) – Source: securityboulevard.com
Source: securityboulevard.com – Author: Avast Blog In a vast world of online threats, certain terms can stand out for their mysterious nature and vague implications. They...
Randall Munroe’s XKCD ‘Lying’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the comic artistry and dry wit of Randall Munroe, maker of XKCD! Permalink *** This is a Security Bloggers...
Unlock 2023’s Top Benefits of Security as a Service! – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Toback Introduction In today’s digital age, the significance of robust cybersecurity for small and medium-sized businesses (SMBs) is more crucial than...
School, Hospital Leaders on Front Lines of Ransomware Attack – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Ransomware From Paying Ransoms to Rebuilding IT Systems, Here’s What the Response Looked Like Michael Novinson...
Why Palo Alto Is Eyeing Data Defense Firm Dig at $300M-$400M – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Big Data Security Analytics , Data Loss Prevention (DLP) , Endpoint Security Dig Security Is Set for a 9-Figure Deal Just...
Why OT Security Keeps Some Healthcare Leaders Up at Night – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 It’s not just medical device cybersecurity that’s keeping some healthcare security leaders up at night – it’s also the risks posed...
ShadowSyndicate: A New Player in the RaaS Landscape – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Ransomware New Group Has Connections to Name-Brand Ransomware-as-a-Service Groups Mihir Bagwe (MihirBagwe) • September 27, 2023...
Live Webinar I Breaking Barriers: Transforming Threat Detection and Response – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Simon Perry Security Evangelist, VMware Carbon Black Simon Perry has 40 years of work experience and has provided strategic cyber security...
Live Webinar | With the Rise of Generative AI, Where is Cloud Security Headed? – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 JT Rakitan Security Product Marketer, Sumo Logic Currently a Security Product Marketer at Sumo Logic, JT Rakitan began his marketing journey...
Chinese Hackers Target Routers in IP Theft Campaign – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Network Firewalls, Network Access Control BlackTech Exploits Trusted Relationship Between Outpost...
FDA Finalizes Guidance Just as New Device Cyber Regs Kick In – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Endpoint Security , Healthcare , Industry Specific Starting Oct. 1, Agency to Require Secure Dev Framework, Threat Modeling, SBOMs Marianne Kolbasuk...
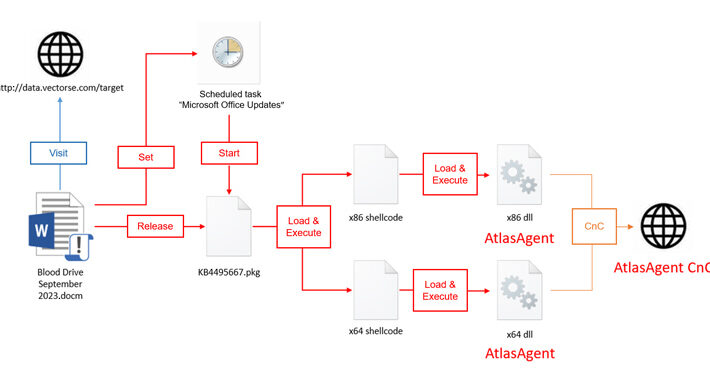
Red Cross-Themed Phishing Attacks Distributing DangerAds and AtlasAgent Backdoors – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 27, 2023THNMalware / Cyber Attack A new threat actor known as AtlasCross has been observed leveraging Red Cross-themed phishing lures...
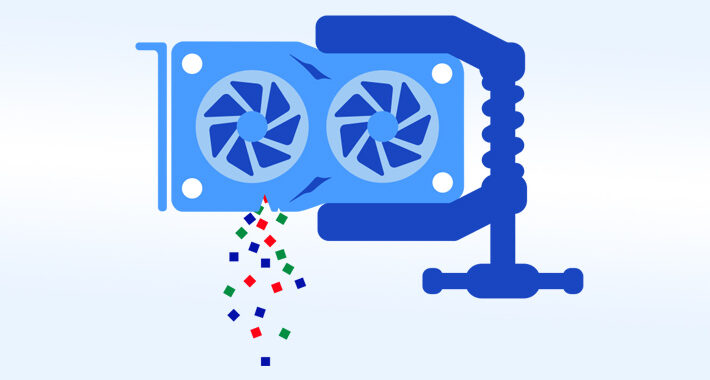
Researchers Uncover New GPU Side-Channel Vulnerability Leaking Sensitive Data – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 27, 2023THNVulnerability / Endpoint Security A novel side-channel attack called GPU.zip renders virtually all modern graphics processing units (GPU) vulnerable...