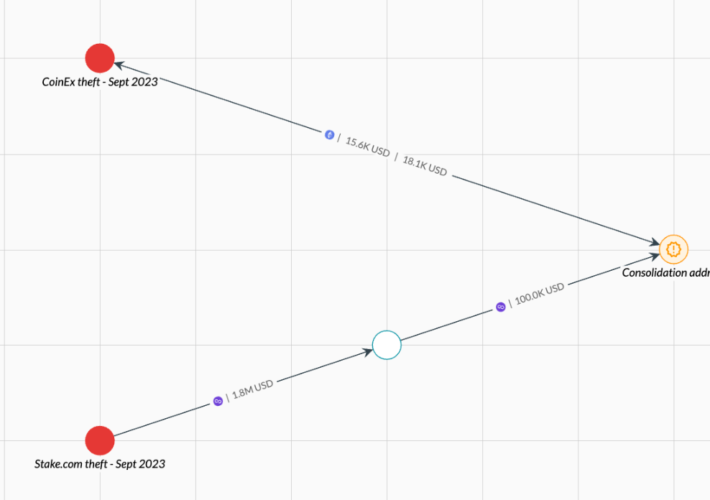
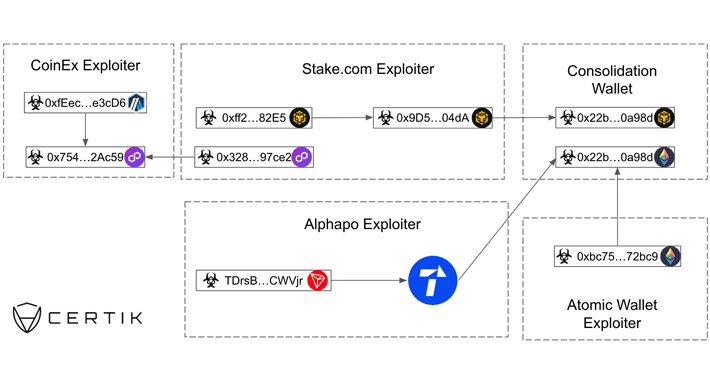
Source: securityaffairs.com – Author: Pierluigi Paganini North Korea’s Lazarus APT stole almost $240 million in crypto assets since June Pierluigi Paganini September 18, 2023 The North...
Month: September 2023
Clop gang stolen data from major North Carolina hospitals – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Clop gang stolen data from major North Carolina hospitals Pierluigi Paganini September 17, 2023 Researchers at healthcare technology firm Nuance blame...
CardX released a data leak notification impacting their customers in Thailand – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini CardX released a data leak notification impacting their customers in Thailand Pierluigi Paganini September 17, 2023 One of Thailand’s major...
TikTok flooded by ‘Elon Musk’ cryptocurrency giveaway scams – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams TikTok is flooded by a surge of fake cryptocurrency giveaways posted to the video-sharing platform, with almost all of the...
Understanding the Cyber Kill Chain: A Comprehensive Guide to Cybersecurity – Source: securityboulevard.com
Source: securityboulevard.com – Author: CyB3rBEA$T In today’s interconnected digital world, cyberattacks have become an ever-present threat to individuals, businesses, and governments. To defend against these threats...
Cyber Week 2023 & The Israel National Cyber Directorate Presents – FraudCON In-Person – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Very Important – Follow available standards and guidelines (NIST, CIS, SLSA etc.) Important – Taken significant steps to secure our...
When Ransomware Attacks Seem Inevitable, What Can IT Teams Do? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Anthony Cusimano The possibility of their business falling victim to a cyberattack has always kept IT teams up at night, but today’s...
UNC3944 Is Now Deploying Ransomware Variants – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Financially Motivated Hackers Are Diversifying Operations Akshaya Asokan (asokan_akshaya) • September 15, 2023 Image: Shutterstock A financially motivated criminal...
Live Webinar Tomorrow | Shielding the Core: Strategies for Protecting Servers and Endpoints – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Andrey Pozhogin Sr. Product Marketing Manager, Endpoint Privilege Security, IT Security Expert, CyberArk Andrey has over 15 years of experience in...
UNC3944 Is Now Deploying Ransomware Variants – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Financially Motivated Hackers Are Diversifying Operations Akshaya Asokan (asokan_akshaya) • September 15, 2023 Image: Shutterstock A financially motivated criminal...
Google Chrome tests Microsoft Edge-like Read Aloud feature – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Mayank Parmar Google Chrome is set to enhance its user experience on the desktop by adding a “read aloud” function, currently available...
Microsoft Edge is losing tablet-friendly “Web Select” feature – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Mayank Parmar Microsoft’s Edge browser, known for its innovative features, is now shedding one of its most applauded functions, Web Select. This...
WhatsApp rival Telegram gets Crypto wallet integration – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Mayank Parmar Telegram, the widely used messaging app, has unveiled an integrated crypto wallet feature, allowing users to effortlessly access their cryptocurrency...
BlackCat ransomware hits Azure Storage with Sphynx encryptor – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Image: Midjourney The BlackCat (ALPHV) ransomware gang now uses stolen Microsoft accounts and the recently spotted Sphynx encryptor to encrypt...
North Korea’s Lazarus Group Suspected in $31 Million CoinEx Heist – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 17, 2023THNCryptocurrency / Cyber Attack The North Korea-affiliated Lazarus Group has stolen nearly $240 million in cryptocurrency since June 2023,...
Security Affairs newsletter Round 437 by Pierluigi Paganini – International edition – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Privacy Overview This website uses cookies to improve your experience while you navigate through the website. Out of these cookies,...
TikTok fined €345M by Irish DPC for violating children’s privacy – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini TikTok fined €345M by Irish DPC for violating children’s privacy Pierluigi Paganini September 16, 2023 The Irish Data Protection Commission...
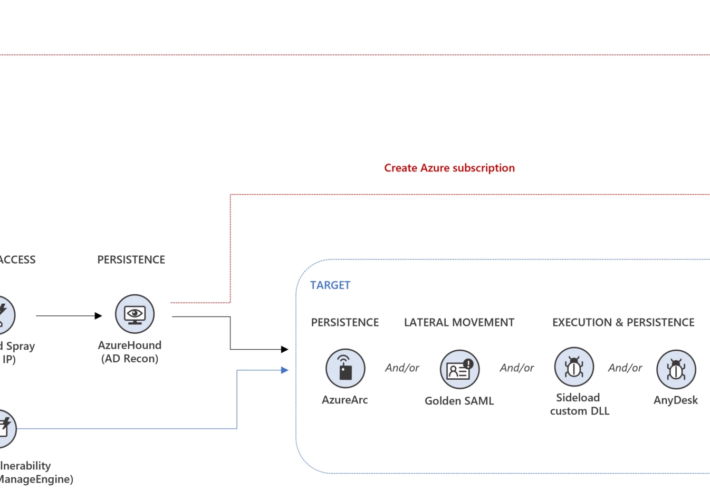
Iranian Peach Sandstorm group behind recent password spray attacks – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Iranian Peach Sandstorm group behind recent password spray attacks Pierluigi Paganini September 16, 2023 Iran-linked Peach Sandstorm APT is behind...
Cyber Week 2023 & The Israel National Cyber Directorate Presents – CSA Israel Event: Deep Dive Into Cloud Security Operations – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Very Important – Follow available standards and guidelines (NIST, CIS, SLSA etc.) Important – Taken significant steps to secure our...
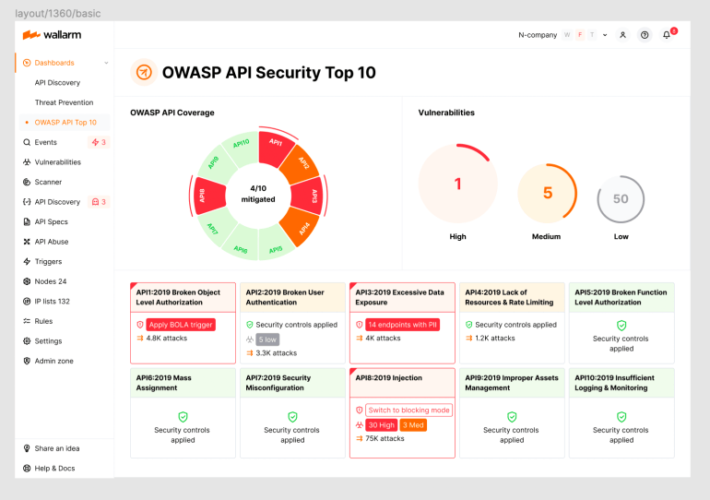
2023 OWASP Top-10 Series: API8:2023 Security Misconfiguration – Source: securityboulevard.com
Source: securityboulevard.com – Author: wlrmblog Welcome to the 9th post in our weekly series on the new 2023 OWASP API Security Top-10 list, with a particular...
How to Mitigate Cybersecurity Risks From Misguided Trust – Source: www.darkreading.com
Source: www.darkreading.com – Author: Stu Sjouwerman, Founder & CEO, KnowBe4, Inc. Kroll’s “2023 State of Cyber Defense” report includes some noteworthy findings about today’s cybersecurity landscape....
Best Practices for Endpoint Security in Healthcare Institutions – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Madalina Popovici While achieving compliance with industry standards is the minimum, it’s not enough to prevent insider threats, supply chain attacks, DDoS,...
Top 10 Healthcare Data Breaches [2022-2023] – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Madalina Popovici In recent years, healthcare institutions have become prime targets for cyberattacks. The year 2022 witnessed an alarming increase in the...
Friday Squid Blogging: Cleaning Squid – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Friday Squid Blogging: Cleaning Squid Two links on how to properly clean squid. I learned a few years ago,...
TikTok Faces Massive €345 Million Fine Over Child Data Violations in E.U. – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 16, 2023THNPrivacy / Technology The Irish Data Protection Commission (DPC) slapped TikTok with a €345 million (about $368 million) fine...
The Week in Ransomware – September 15th 2023 – Russian Roulette – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams This week’s big news is the extortion attacks on the Caesars and MGM Las Vegas casino chains, with one having...
6 most common cyber security vulnerabilities you should know in 2023 – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau Contributed by George Mack, Content Marketing Manager, Check Point Software. Nearly all security incidents stem from cyber security vulnerabilities. What is...
Dariy Pankov, the NLBrute malware author, pleads guilty – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Dariy Pankov, the NLBrute malware author, pleads guilty Pierluigi Paganini September 15, 2023 The Russian national Dariy Pankov, aka dpxaker,...
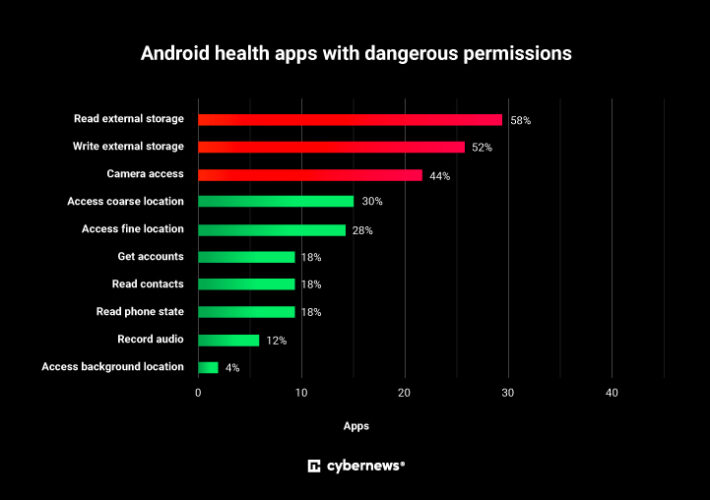
Dangerous permissions detected in top Android health apps – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Dangerous permissions detected in top Android health apps Pierluigi Paganini September 15, 2023 Leading Android health apps expose users to...
Caesars Entertainment paid a ransom to avoid stolen data leaks – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Caesars Entertainment paid a ransom to avoid stolen data leaks Pierluigi Paganini September 15, 2023 Caesars Entertainment announced it has...















![top-10-healthcare-data-breaches-[2022-2023]-–-source:-heimdalsecurity.com](https://ciso2ciso.com/wp-content/uploads/2023/09/79529/top-10-healthcare-data-breaches-2022-2023-source-heimdalsecurity-com.png)