Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development , Standards, Regulations & Compliance Cisco’s Pam Lindemoen and Daniel...
Month: September 2023
Why Entities Should Review Their Online Tracker Use ASAP – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Healthcare , HIPAA/HITECH Nick Heesters of HHS OCR on the Agency’s Top Areas of HIPAA Scrutiny...
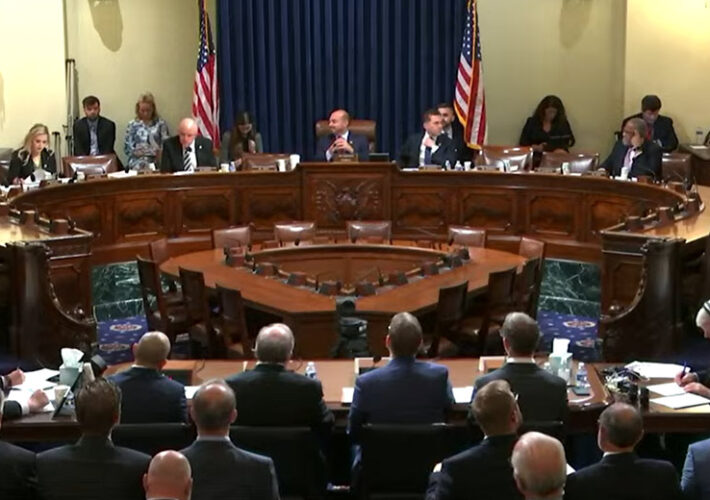
Cyber Experts Urge House Committee to Avoid Federal Shutdown – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Critical Infrastructure Security , Cybersecurity Spending , Government Annual Federal Funding Will Expire in 12 Days Marianne Kolbasuk McGee (HealthInfoSec) •...
CrowdStrike to Buy AppSec Startup Bionic for Reported $350M – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cloud Security , Security Operations Deal Will Offer Visibility Into Application Behavior, Vulnerability Prioritization Michael Novinson (MichaelNovinson) • September 19, 2023...
China-Linked Actor Taps Linux Backdoor in Forceful Espionage Campaign – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading “Earth Lusca,” a China-linked cyber espionage actor that’s been actively targeting government organizations in Asia, Latin...
Trend Micro Patches Zero-Day Endpoint Vulnerability – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Trend Micro has released an advisory covering a critical zero-day flaw — tracked as CVE-2023-41179 — that...
MGM, Caesars Face Regulatory, Legal Maze After Cyber Incidents – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading In the wake of the new Securities and Exchange Commission (SEC) regulatory requirements to disclose “material” cyber...
Qatar Cyber Chiefs Warn on Mozilla RCE Bugs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The National Cyber Security Agency in Qatar is warning Adobe users to urgently apply patches following the...
Name That Toon: Somewhere in Sleepy Hollow – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner, Cartoonist Harken, readers! ‘Tis you we love! Come up with a clever cybersecurity-related caption for the cartoon, above! (Our favorite...
Clorox Sees Product Shortages Amid Cyberattack Cleanup – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading The Clorox Company is starting to feel the pinch of product shortages after a recent...
CapraRAT Impersonates YouTube to Hijack Android Devices – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading A known Pakistan-linked threat actor is dangling romance-based content lures to spread Android-based spyware that mimics YouTube...
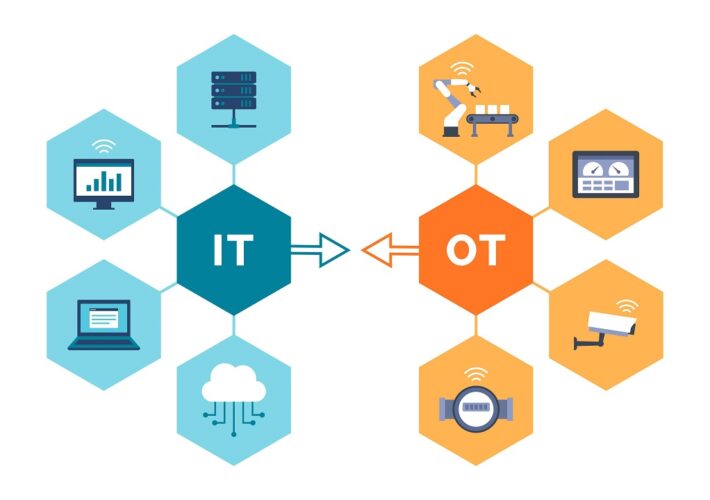
Engineering-Grade OT Protection – Source: www.darkreading.com
Source: www.darkreading.com – Author: Andrew Ginter, Vice President of Industrial Security, Waterfall Security Solutions The following are excerpts from a book set to be launched Nov....
Welcome to the Resilience Revolution, Where Defenders Act More Like Attackers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Dark Reading News Desk interviewed Kelly Shortridge, senior principal at Fastly at Black Hat USA 2023 about...
‘ShroudedSnooper’ Backdoors Use Ultra-Stealth in Mideast Telecom Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading A potentially novel threat actor recently compromised two Middle East-based telecommunications organizations, using two backdoors with...
Cyber Experts Urge House Committee to Avoid Federal Shutdown – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Critical Infrastructure Security , Cybersecurity Spending , Government Annual Federal Funding Will Expire in 12 Days Marianne Kolbasuk McGee (HealthInfoSec) •...
Journey to the Cloud: Navigating the Transformation – Part 2 – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cloud Security , Security Operations Nikko Asset Management’s Marcus Rameke on the Advantages of HCI On-Premises CyberEdBoard • September 19, 2023...
Generative AI: Embrace It, But Put Up Guardrails – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development , Standards, Regulations & Compliance Cisco’s Pam Lindemoen and Daniel...
Why Entities Should Review Their Online Tracker Use ASAP – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Governance & Risk Management , Healthcare , HIPAA/HITECH Nick Heesters of HHS OCR on the Agency’s Top Areas of HIPAA Scrutiny...
CrowdStrike to Buy AppSec Startup Bionic for Reported $350M – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cloud Security , Security Operations Deal Will Offer Visibility Into Application Behavior, Vulnerability Prioritization Michael Novinson (MichaelNovinson) • September 19, 2023...
CrowdStrike to Acquire Application Intelligence Startup Bionic – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Cybersecurity vendor CrowdStrike on Tuesday announced plans to acquire Bionic, a Silicon Valley startup selling tools in the Application Security...
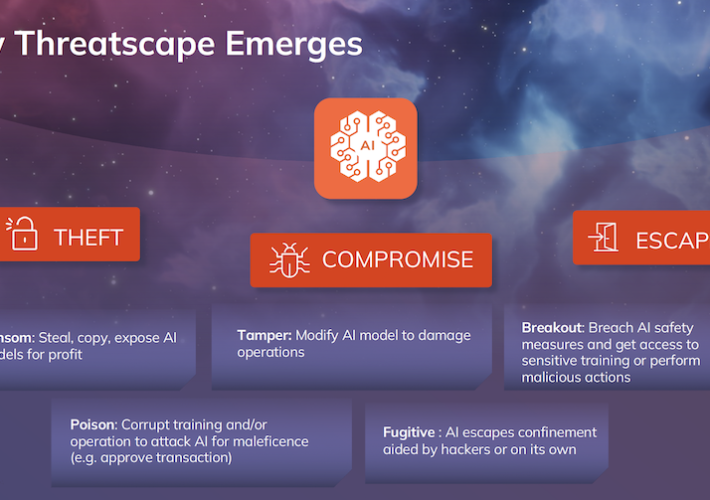
HiddenLayer Raises Hefty $50M Round for AI Security Tech – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Texas startup HiddenLayer has bagged a hefty $50 million in new venture capital funding as investors continue to pour money...
Venafi Leverages Generative AI to Manage Machine Identities – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Machine identity firm Venafi has launched a proprietary generative AI (gen-AI) model to help with the mammoth, complex, and expanding...
‘Cybersecurity Incident’ Hits ICC – Source: www.securityweek.com
Source: www.securityweek.com – Author: AFP The International Criminal Court said Tuesday it had been affected by what it called “anomalous activity” regarding its IT systems and...
Clorox Blames Damaging Cyberattack for Product Shortage – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Cleaning products manufacturer Clorox says the recent cyberattack has been contained, but production is still not fully restored and some...
Alcion Raises $21 Million for Backup-as-a-Service Platform – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Data management startup Alcion today announced that it has raised $21 million in a Series A funding round that brings...
Pakistani APT Uses YouTube-Mimicking RAT to Spy on Android Devices – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Pakistan-linked state-sponsored threat actor Transparent Tribe has been observed using new versions of the CapraRAT Android trojan that mimic the...
Thousands of Juniper Appliances Vulnerable to New Exploit – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Threat intelligence firm VulnCheck has published details on a new exploit targeting a recent Junos OS vulnerability and says that...
Trend Micro Patches Exploited Zero-Day Vulnerability in Endpoint Security Products – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Trend Micro on Tuesday released an advisory to warn customers that a critical vulnerability affecting Apex One and other endpoint...
Hacker Conversations: Casey Ellis, Hacker and Ringmaster at Bugcrowd – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend In this edition of Hacker Conversations, SecurityWeek talks to Casey Ellis, founder, chairman and CTO at Bugcrowd – and hacker....
ShroudedSnooper’s HTTPSnoop Backdoor Targets Middle East Telecom Companies – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 19, 2023THNMalware / Cyber Threat Telecommunication service providers in the Middle East are the target of a new intrusion set...