Source: www.securityweek.com – Author: Ryan Naraine Private equity powerhouse Thoma Bravo on Wednesday announced plans to merge the just-acquired ForgeRock with Ping Identity, combining two of...
Month: August 2023
Smart Cities: Utopian Dream, Security Nightmare, or Political Gimmick? – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend How much smart does a smart city need to be called smart? It’s not a trivial question. It goes to...
FBI Finds 1,580 Bitcoin in Crypto Wallets Linked to North Korean Hackers – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The Federal Bureau of Investigation has published information on six cryptocurrency wallets operated by North Korean hackers and believed to...
Cybersecurity Companies Report Surge in Ransomware Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Cybersecurity companies have released a dozen ransomware reports in recent weeks and most of them show a significant increase in...
The End of “Groundhog Day” for the Security in the Boardroom Discussion? – Source: www.securityweek.com
Source: www.securityweek.com – Author: Marc Solomon It’s been eight and half years since I first wrote about the need for security leadership representation in the boardroom....
3,000 Openfire Servers Exposed to Attacks Targeting Recent Vulnerability – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire More than 3,000 Openfire servers have not been patched against a recent vulnerability and remain exposed to attacks relying on...
US Government Publishes Guidance on Migrating to Post-Quantum Cryptography – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The Cybersecurity and Infrastructure Security Agency (CISA), the National Security Agency (NSA), and the National Institute of Standards and Technology...
First Weekly Chrome Security Update Patches High-Severity Vulnerabilities – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Google this week announced a Chrome 116 security update that patches five memory safety vulnerabilities reported by external researchers, including...
Exploitation of Ivanti Sentry Zero-Day Confirmed – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Ivanti has confirmed that a recently discovered vulnerability affecting its Sentry mobile gateway has been exploited in attacks. The existence...
XLoader MacOS Malware Variant Returns With OfficeNote Facade – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The notorious XLoader malware has resurfaced, posing as a seemingly innocuous office productivity app named “OfficeNote.” Known for its malicious activities...
WinRAR Vulnerability Affects Traders Worldwide – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Cybersecurity researchers have exposed a zero-day vulnerability (CVE-2023-38831) in the popular WinRAR compression tool, which cyber-criminals have exploited to target traders...
Artificial Intelligence and USBs Drive 8% Rise in Cyber-Attacks – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Check Point Research has released its 2023 Mid-Year Security Report. The research reveals a concerning 8% surge in global weekly cyber-attacks...
Thousands of High-Risk Incidents Neutralized Using AI – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The most widely encountered high-risk cyber incidents in 2023 involved identity abuse, according to findings from Barracuda’s latest XDR Insights report,...
Doubling of Identity Theft Victims With Suicidal Thoughts – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Some 16% of American identity theft victims have had suicidal thoughts following their experiences, up from just 8% in 2020, according...
Experian Pays $650,000 to Settle Spam Claims – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Experian Consumer Services has agreed to a permanent injunction and to pay a civil penalty of $650,000 to settle allegations relating...
North Korean Affiliates Suspected in $40M Cryptocurrency Heist, FBI Warns – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 23, 2023THNCryptocurrency / Cyber Attack The U.S. Federal Bureau of Investigation (FBI) on Tuesday warned that threat actors affiliated with...
Meta Set to Enable Default End-to-End Encryption on Messenger by Year End – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 23, 2023THNEncryption / Privacy Meta has once again reaffirmed its plans to roll out support for end-to-end encryption (E2EE) by...
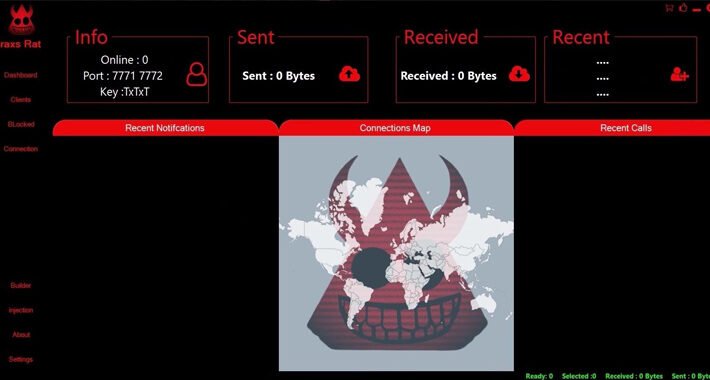
Syrian Threat Actor EVLF Unmasked as Creator of CypherRAT and CraxsRAT Android Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 23, 2023THNMobile Security / Cyber Crime A Syrian threat actor named EVLF has been outed as the creator of malware...
Agile Approach to Mass Cloud Credential Harvesting and Crypto Mining Sprints Ahead – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 23, 2023The Hacker NewsMalware / Cybersecurity Developers are not the only people who have adopted the agile methodology for their...
Windows 10 KB5029331 update introduces a new Backup app – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Microsoft has released the optional KB5029331 Preview cumulative update for Windows 10 22H2 with sixteen improvements or fixes, including the...
Over 3,000 Openfire servers vulnerable to takover attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Thousands of Openfire servers remain vulnerable to CVE-2023-32315, an actively exploited and path traversal vulnerability that allows an unauthenticated user...
Bitwarden releases free and open-source E2EE Secrets Manager – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Bitwarden, the maker of the popular open-source password manager tool, has released ‘Secrets Manager,’ an end-to-end encrypted secrets manager for...
Discord starts notifying users affected by March data breach – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Starting on Monday, Discord has been reaching out to users affected by a data breach disclosed earlier this year to...
New stealthy techniques let hackers gain Windows SYSTEM privileges – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ionut Ilascu Security researchers have released NoFilter, a tool that abuses the Windows Filtering Platform to elevate a user’s privileges to increases...
US charges founders of Tornado Cash mixer used by Lazarus hackers – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The U.S. Justice Department charged two Tornado Cash founders with helping criminals, including the notorious North Korean Lazarus hacking group,...
Kali Linux 2023.3 released with 9 new tools, internal changes – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Kali Linux 2023.3, the third version of 2023, is now available for download, with nine new tools and internal optimizations....
Google Workspace will require two admins to sign off on critical changes – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Google announced today new cybersecurity defense controls that will allow security teams to thwart social engineering attacks like phishing targeting...
FBI: Lazarus hackers readying to cash out $41 million in stolen crypto – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The FBI warned that North Koreans are likely readying to cash out tens of millions worth of stolen cryptocurrency out...
Hosting firm says it lost all customer data after ransomware attack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Danish hosting firms CloudNordic and AzeroCloud have suffered ransomware attacks, causing the loss of the majority of customer data and...
New HiatusRAT Malware Campaign Targets U.S. Defense Department`s Server – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși Threat actors launched a reconnaissance attack against a server belonging to the U.S. Department of Defense, as part of HiatusRAT...