Source: www.techrepublic.com – Author: Cedric Pernet A new variant of malware called XLoader is targeting macOS users. XLoader’s execution, functionalities and distribution are detailed. Image: Sashkin/Adobe...
Month: August 2023
Kroll Suffers Data Breach: Employee Falls Victim to SIM Swapping Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 26, 2023THNData Breach / SIM Swapping Risk and financial advisory solutions provider Kroll on Friday disclosed that one of its...
How to Choose the Best XDR Solution for Your Organization? – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Andreea Chebac The fact that malicious software gets smarter and more sophisticated every day that goes by is no news to any...
Genworth Financial Under Investigation for Data Breach – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 SAN FRANCISCO, Aug. 24, 2023 /PRNewswire/ — Schubert Jonckheer & Kolbe LLP is investigating a data breach impacting the personal information of over...
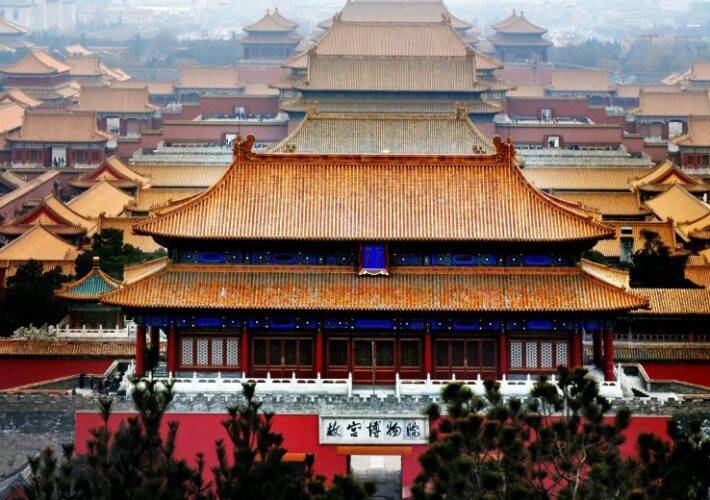
China Unleashes Flax Typhoon APT to Live Off the Land, Microsoft Warns – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading A China-backed advanced persistent threat (APT) group dubbed Flax Typhoon has installed a web of persistent,...
Luna Grabber Malware Targets Roblox Gaming Devs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Since the start of this month, researchers at ReversingLabs have found a host of malicious, multistage packages...
‘Whiffy Recon’ Malware Transmits Device Location Every 60 Seconds – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer, Dark Reading Researchers have uncovered the “Whiffy Recon” malware being deployed by the SmokeLoader botnet, which is a...
Is Bias in AI Algorithms a Threat to Cloud Security? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Amir Shachar, Director of AI and Research, Skyhawk Security Artificial intelligence (AI) has been helping humans in IT security operations since the...
NIST Publishes First Draft Standards for Post-Quantum Cryptography – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jeffrey Schwartz, Contributing Writer, Dark Reading The first draft standards for quantum-resistant public key cryptography based on algorithms chosen by the National...
Data breach at French govt agency exposes info of 10 million people – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Pôle emploi, France’s governmental unemployment registration and financial aid agency, is informing of a data breach that exposed data belonging...
MSI: Recent wave of Windows blue screens linked to MSI motherboards – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan MSI has officially confirmed the recent surge of blue screens of death (BSODs) encountered by Windows users after installing this...
ICO calls social media firms to protect people’s data from scraping – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas UK’s Information Commissioner’s Office (ICO), together with eleven data protection and privacy authorities from around the world, have published a...
Microsoft: Stealthy Flax Typhoon hackers use LOLBins to evade detection – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Microsoft has identified a new hacking group it now tracks as Flax Typhoon that argets government agencies and education, critical manufacturing,...
Leaseweb is restoring ‘critical’ systems after security breach – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Leaseweb, one of the world’s largest cloud and hosting providers, notified people that it’s working on restoring “critical” systems disabled...
Kroll data breach exposes info of FTX, BlockFi, Genesis creditors – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Multiple reports on social media warn of a data breach at financial and risk advisory company Kroll that resulted in...
BSides Cheltenham 2023 – Cristian Cornea – Bypassing Anti-Virus Using BadUSB – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Yes, we have specific objectives for uptime and recovery Yes, we talk about resilience, but don’t have specific objectives It’s...
Kroll Employee SIM-Swapped for Crypto Investor Data – Source: securityboulevard.com
Source: securityboulevard.com – Author: BrianKrebs Security consulting giant Kroll disclosed today that a SIM-swapping attack against one of its employees led to the theft of user...
Daniel Stori’s ‘Python Robots’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Yes, we have specific objectives for uptime and recovery Yes, we talk about resilience, but don’t have specific objectives It’s...
Perceptions, SaaS Identities and AI – Source: securityboulevard.com
Source: securityboulevard.com – Author: Beverly Nevalga, Sr. Content Marketing Manager @ AppOmni In his presentation, Brendan O’Connor examined Identity risk within the SaaS ecosystem. He broke...
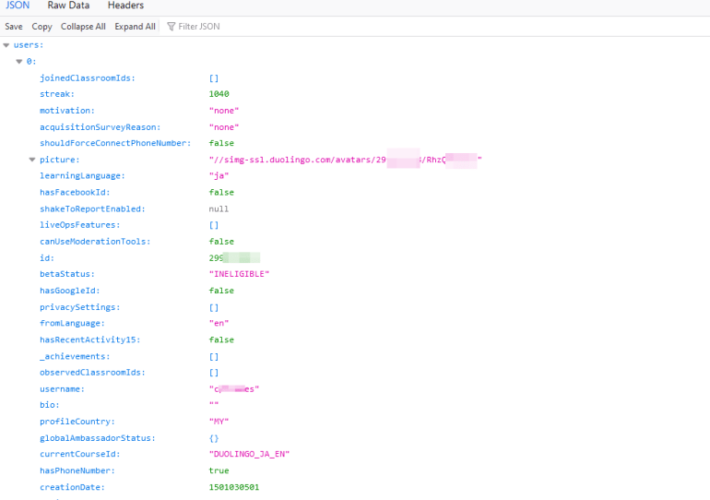
API Abuse – Lessons from the Duolingo Data Scraping Attack – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tim Erlin It’s been reported that 2.6 million user records sourced from the Duolingo app are for sale. The attacker apparently obtained...
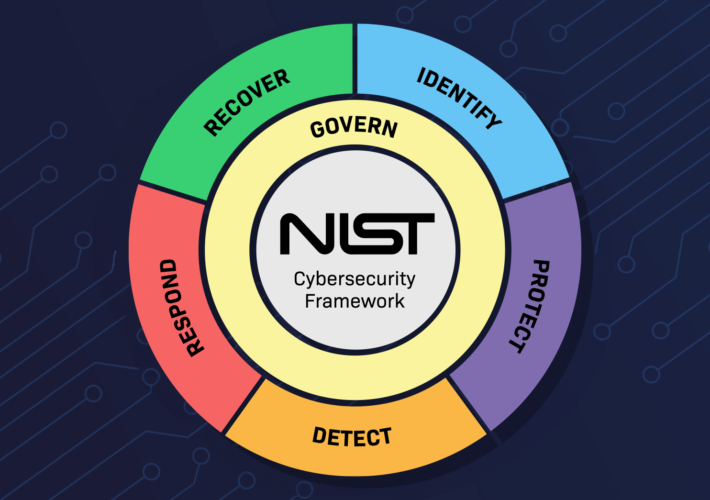
NIST CSF 2.0: The Journey so Far and What’s Ahead – Source: securityboulevard.com
Source: securityboulevard.com – Author: Chris Griffith NIST CSF 1.1 to 2.0 is a significant update reflecting an inclusive and responsive approach to risk management. The most...
Versa Networks Adds Generative AI to SASE Platform – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard Versa Networks this week revealed it has extended its secure access service edge (SASE) platform to include generative artificial intelligence...
Scammers Target Online Markets with Telekopye Phishing Toolkit – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Bad actors are using a full-featured phishing toolkit to target large numbers of users of popular online shopping sites like...
Cybersecurity Insights with Contrast CISO David Lindner | 8/25 – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Lindner, Director, Application Security Yes, we have specific objectives for uptime and recovery Yes, we talk about resilience, but don’t have...
BSides Cheltenham 2023 – Welcome And Announcements By BSides Cheltenham Orga – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Yes, we have specific objectives for uptime and recovery Yes, we talk about resilience, but don’t have specific objectives It’s...
Lazarus Group Debuts Tiny Trojan for Espionage Attacks – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Critical Infrastructure Security , Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime The Malware Is Based on an Unusual Development...
Live Fireside Chat | Getting Governance that Works – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Digital Identity , Governance & Risk Management , Identity & Access Management Presented by Radiant Logic 60 minutes ...
ISMG Editors: The Shifting Cyber Insurance Landscape – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyber Insurance , Governance & Risk Management , Video Also: Global Privacy Trends; Tornado Cash Founders Charged Anna Delaney (annamadeline) •...
UnitedHealthcare Fined $80K for 6-Month Records Access Delay – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Healthcare , HIPAA/HITECH , Industry Specific HHS Settlement Is Agency’s 45th HIPAA ‘Right of Access’ Enforcement Action Marianne Kolbasuk McGee (HealthInfoSec)...
Chinese State Hackers ‘Flax Typhoon’ Targeting Taiwan – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Likely Espionage Campaign Focuses on Persistence and Credential Dumping Prajeet Nair (@prajeetspeaks)...