Source: www.darkreading.com – Author: 1 Safe Security, the AI-Driven Cyber Risk Management company, has acquired RiskLens, the pioneer of the Cyber Risk Quantification standard – FAIR....
Month: July 2023
Linux Hacker Exploits Researchers With Fake PoCs Posted to GitHub – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading A GitHub user managed to dupe security researchers by publishing fake proofs-of-concept (PoCs) containing Linux backdoors....
Cybersecurity Leaders Report Reduction in Disruptive Cyber Incidents With MSS/MDR Solutions – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 DENVER — July 12, 2023 — Optiv, the cyber advisory and solutions leader, has published a report based on a recent survey...
GUEST ESSAY: Why it’s high time for us to rely primarily on passwordless authentication – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Thierry Gagnon Accessing vital information to complete day-to-day tasks at our jobs still requires using a password-based system at most...
Security Affairs newsletter Round 429 by Pierluigi Paganini – International edition – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Privacy Overview This website uses cookies to improve your experience while you navigate through the website. Out of these cookies,...
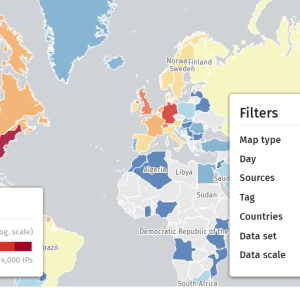
Shadowserver reported that +15K Citrix servers are likely vulnerable to attacks exploiting the flaw CVE-2023-3519 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers reported that more than 15000 Citrix servers exposed online are likely vulnerable to attacks exploiting the vulnerability CVE-2023-3519. The...
BSides Sofia 2023 – Alexandar Andonov – The Secure Software Supply Chain Function S3C – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
Maine CISO on the State’s Six-Month Generative AI ‘Pause’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lohrmann on Cybersecurity Maine paused the use of ChatGPT and other generative AI apps for six months beginning in June. After hearing...
Crossing the road – Source: securityboulevard.com
Source: securityboulevard.com – Author: Matt Palmer Last week I spoke for Jersey Cyber Security Centre ( CERT.JE) about the changing threats facing us — from the very active...
Clop now leaks data stolen in MOVEit attacks on clearweb sites – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams The Clop ransomware gang is copying an ALPHV ransomware gang extortion tactic by creating Internet-accessible websites dedicated to specific victims,...
Microsoft enhances Windows 11 Phishing Protection with new features – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Microsoft is further enhancing the Windows 11 Enhanced Phishing Protection by testing a new feature that warns users when they copy...
CISA warns govt agencies to patch Adobe ColdFusion servers – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has given federal agencies three weeks to secure Adobe ColdFusion servers on...
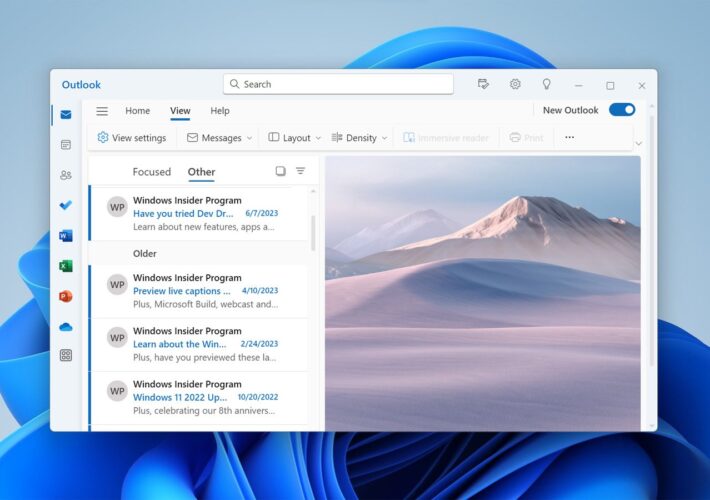
Microsoft force-migrating Windows Mail & Calendar apps to Outlook app in August – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Microsoft will retire the Windows Mail and Calendar applications on Windows 10 and Windows 11 at the end of the...
Windows 11 23H2 getting an energy report with app’s power usage – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Mayank Parmar Microsoft is making it easier to see how much energy your apps use in Windows 11 over a given period...
Over 15K Citrix servers vulnerable to CVE-2023-3519 RCE attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Thousands of Citrix Netscaler ADC and Gateway servers exposed online are vulnerable to attacks exploiting a critical remote code execution...
How Hackers Can Hijack a Satellite – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading A computer flying hundreds or even thousands of kilometers in the sky, at a speed of...
Cisco Flags Critical SD-WAN Vulnerability – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading A critical security vulnerability in Cisco’s SD-WAN vManage software could allow a remote, unauthenticated attacker to gain read and...
Rogue Azure AD Guests Can Steal Data via Power Apps – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ericka Chickowski, Contributing Writer, Dark Reading Guest accounts in Azure AD (AAD) are meant to provide limited access to corporate resources for...
Zimbra Zero-Day Demands Urgent Manual Update – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Teams running the Zimbra Collaboration Suite version 8.8.15 are urged to apply a manual fix against a...
Training’s New Understanding – Source: www.darkreading.com
Source: www.darkreading.com – Author: Curtis Franklin, Senior Analyst, Omdia Cybersecurity awareness training is a risky business. And the importance of measuring risk before and after training...
Electrical Grid Stability Relies on Balancing Digital Substation Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Steve Kunsman, Director of Product Management and Applications, Hitachi Energy With a central role in modern electrical systems, digital substations are of...
Brand Impersonation Scams in Middle East & Africa See Massive Growth – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading The number of detected fake and scam websites pertaining to be reputable brands from the Middle...
White House Fills in Details of National Cybersecurity Strategy – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Fresh from the federal policy mill, the Biden Administration’s 57-page National Cybersecurity Strategy Implementation Plan (NCSIP)...
What happens if AI is wrong? – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Responses generated by ChatGPT about individual people could be misleading or harmful or spill their personal information. What are the takeaways for...
Avoiding data backup failures – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Today is World Backup Day, but maybe we also need a “did you test your backups” day? Original Post URL: Category &...
Banking turmoil opens opportunities for fraud – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Scammers are looking to cash in on the chaos that has set in following the startling meltdowns of Silicon Valley Bank and...
Twitter ends free SMS 2FA: Here’s how you can protect your account now – Source:
Source: – Author: 1 Twitter’s ditching of free text-message authentication doesn’t mean that you should forgo using 2FA. Instead, switch to another – and, indeed, better...
Understanding Managed Detection and Response – and what to look for in an MDR solution – Source:
Source: – Author: 1 Why your organization should consider an MDR solution and five key things to look for in a service offering Original Post URL:...
What TikTok knows about you – and what you should know about TikTok – Source:
Source: – Author: 1 As TikTok CEO attempts to placate U.S. lawmakers, it’s time for us all to think about the wealth of personal information that...
Highlights from TikTok CEO’s Congress grilling – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Here are some of the key moments from the five hours of Shou Zi Chew’s testimony and other interesting news on the...