Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Apple has released security updates to address zero-day vulnerabilities exploited in attacks targeting iPhones, Macs, and iPads. “Apple is aware...
Month: July 2023
Flipper Zero now has an app store to install third-party apps – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The Flipper Zero team has launched its very own ‘Flipper Apps’ mobile app store, allowing mobile users to install 3rd-party...
JumpCloud hack linked to North Korea after OPSEC mistake – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan A hacking unit of North Korea’s Reconnaissance General Bureau (RGB) was linked to the JumpCloud breach after the attackers made...
Microsoft shares fix for some Outlook hyperlinks not opening – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft shared a workaround for Outlook Desktop blocking attempts to open IP address or fully qualified domain name (FQDN) hyperlinks...
Apple addressed a new actively exploited zero-day tracked as CVE-2023-38606 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Apple released security updates to address an actively exploited zero-day flaw in iOS, iPadOS, macOS, tvOS, watchOS, and Safari. Apple released...
Twelve Norwegian ministries were hacked using a zero-day vulnerability – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Threat actors exploited a zero-day flaw in third-party software in attacks against the ICT platform used by 12 Norwegian ministries....
A flaw in OpenSSH forwarded ssh-agent allows remote code execution – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A new flaw in OpenSSH could be potentially exploited to run arbitrary commands remotely on compromised hosts under specific conditions....
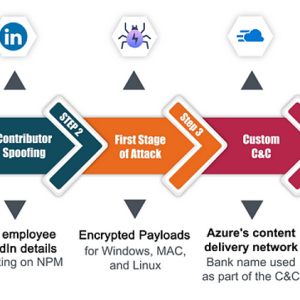
Experts warn of OSS supply chain attacks against the banking sector – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Checkmark researchers have uncovered the first known targeted OSS supply chain attacks against the banking sector. In the first half of...
Apple could opt to stop iMessage and FaceTime services due to the government’s surveillance demands – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Apple could opt to pull iMessage and FaceTime services in the U.K. in response to the government’s surveillance demands. In...
Managing Human Risk: Discoveries From SANS 2023 Security Awareness Report – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 BETHESDA, MD. (PRWEB) JULY 24, 2023 — As artificial intelligence (AI) amplifies the sophistication and reach of phishing, vishing, and smishing attacks,...
Global Security Assurance Market to Reach $13B by 2030 – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 DUBLIN, July 24, 2023 /PRNewswire/ — The “Security Assurance – Global Strategic Business Report” report has been added to ResearchAndMarkets.com’s offering. The global market for Security Assurance,...
CISOs Connect Launches the 2023 CISO Choice Awards – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 NEW YORK, July 24, 2023 /PRNewswire/ — CISOs Connect™ today opened nominations for its annual CISO-selected vendor recognition, the 2023 CISO Choice Awards, and named...
OneTrust Secures $150M Investment Led by Generation Investment Management – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 ATLANTA, July 24, 2023 /PRNewswire/ — OneTrust, the market-defining leader for trust intelligence, today announced a $150 million funding round. This capital will bolster OneTrust’s continued...
TARA Partners With Plante Moran to Deliver Risk-Based Vulnerability Management – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 CLARKSTON, Mich., July 24, 2023 /PRNewswire/ — TARA, an industry leading risk-based vulnerability management platform, has announced a strategic partnership with Plante Moran,...
China Propaganda Spreads via US News Sites, Freelancers, Times Square – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading The organizers of a pro-People’s Republic of China (PRC) influence campaign called “HaiEnergy” are taking the...
Orgs Face Record $4.5M Per Data Breach Incident – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading The average cost per data breach for business in 2023 jumped to $4.45 million, a 15% increase...
Are AI-Engineered Threats FUD or Reality? – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Dwyer, Head of Research, IBM Security X-Force The moment that generative AI applications hit the market, it changed the pace of...
Atlassian RCE Bugs Plague Confluence, Bamboo – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Three just-disclosed remote code execution (RCE) security vulnerabilities open up Atlassian Confluence Data Center & Server, and...
KillNet’s Kremlin Connection Unclear as the Cybercrime Collective Grows – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Although the precise connection between Russian threat group KillNet and the Kremlin remains nebulous, its high-profile, and increasingly...
IBM: Cost of a Data Breach Hits Another High – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt The average cost to an organization hit with a data breach reached a record high this year, though those companies...
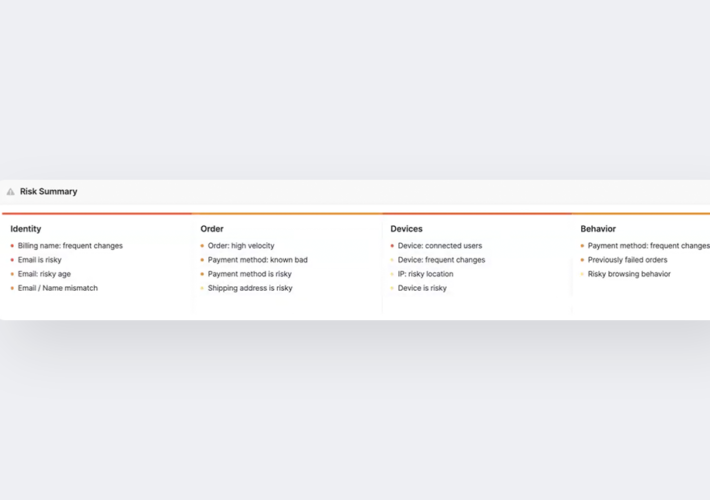
Lost transparency, blackbox ML, and other hidden risks of outsourced fraud solutions – Source: securityboulevard.com
Source: securityboulevard.com – Author: Coby Montoya Machine learning-based fraud decision engines are sometimes viewed as mysterious black boxes that only provide minimal insight into why a...
Google Launches Red Team to Secure AI Systems Against Attacks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Google is rolling out a red team charged with testing the security of AI systems by running simulated but realistic...
BSides Leeds 2023 – BSides Leeds Orga – Opening Remarks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
CodeSecDays brings security leaders together to build a world without software security issues – Source: securityboulevard.com
Source: securityboulevard.com – Author: Mackenzie Jackson In GitGuardian’s first digital conference, CodeSecDays, security leaders from multiple leading companies like Synk, Chainguard, Doppler, RedMonk, and more came...
AI and the software supply chain: Application security just got a whole lot more complicated – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ericka Chickowski As artificial intelligence (AI) captivates the hearts and minds of business and technology executives eager to generate rapid gains from...
Netography Fusion Enhancements Give SOC, NOC, and AIOps Teams Faster Detection and Response to Anomalies and Threats, Automated Context Label Creation – Source: securityboulevard.com
Source: securityboulevard.com – Author: Patrick Bedwell Netography Fusion Enhancements Give SOC, NOC, and AIOps Teams Faster Detection and Response to Anomalies and Threats, Automated Context Label...
‘China’ Azure Breach: MUCH Worse Than Microsoft Said – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings Satya and Pooh, Sitting in a Tree, K.I.S.S.I.N.G. The nasty hack ‘by China’ I covered 11 days ago is even...
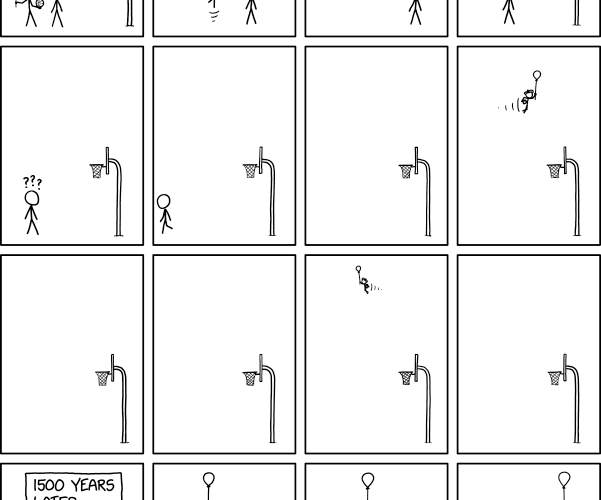
Randall Munroe’s XKCD ‘Global Atmospheric Circulation’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
How to Safeguard PHI From Healthcare SaaS Risks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Josh Smith, Strategic Alliance Manager @ AppOmni Five Critical Steps to Securing Healthcare SaaS 2. Identify which SaaS apps house your crown...
Gamification Can Make Security Training Fun – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Security Awareness Programs & Computer-Based Training , Training & Security Leadership Webhelp CISO on Interactive Tools for Cybersecurity Awareness Training Anna...