Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Researchers have written exploit code for a critical remote code execution (RCE) vulnerability in Fortinet’s FortiGate...
Day: July 3, 2023
Russian Satellite Internet Downed via Attackers Claiming Ties to Wagner Group – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Russian satellite Internet provider Dozor-Teleport was knocked offline in the early hours of June 29, dealing a...
Israel Aided UAE in Defending Against DDoS Attack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Israel earlier this year aided the United Arab Emirates (UAE) in helping repel a major distributed...
SSH Servers Hit in ‘Proxyjacking’ Cyberattacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Threat actors are exploiting vulnerable secure shell protocol (SSH) servers to launch Docker services that take advantage...
Name That Edge Toon: Three-Ring Circus – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner, Cartoonist Let’s see you tame this contest beast! Come up with a witty cybersecurity-related caption to explain the scary scene...
A CISO’s Guide to Paying Down Software Supply Chain Security Debt – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Lorenc, Founder & CEO, Chainguard There has always been a tradeoff in IT between shipping new features and functionality versus paying...
Microsoft denies data breach, theft of 30 million customer accounts – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Microsoft has denied the claims of the so-called hacktivists “Anonymous Sudan” that they breached the company’s servers and stole credentials...
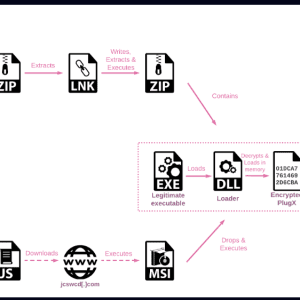
Hackers target European government entities in SmugX campaign – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A phishing campaign that security researchers named SmugX and attributed to a Chinese threat actor has been targeting embassies and...
Microsoft Edge upgrades built-in Cloudflare VPN with 5GB of data – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Mayank Parmar Microsoft’s Edge browser has recently enhanced its ‘Edge Secure Network’ feature, which now offers 5GB of data, significantly increasing from...
300,000+ Fortinet firewalls vulnerable to critical FortiOS RCE bug – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Hundreds of thousands of FortiGate firewalls are vulnerable to a critical security issue identified as CVE-2023-27997, almost a month after...
Twitter’s bot spam keeps getting worse — it’s about porn this time – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ax Sharma Forget crypto spam accounts, Twitter’s got another problem which involves bots and accounts promoting adult content and infiltrating Direct Messages and...
Snappy: A tool to detect rogue WiFi access points on open networks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Cybersecurity researchers have released a new tool called ‘Snappy’ that can help detect fake or rogue WiFi access points that...
BlackCat ransomware pushes Cobalt Strike via WinSCP search ads – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Image: Bing Create The BlackCat ransomware group (aka ALPHV) is running malvertizing campaigns to lure people into fake pages that...
SmugX: Chinese APT uses HTML smuggling to target European Ministries and embassies – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini China-linked APT group was spotted using HTML smuggling in attacks aimed at Foreign Affairs ministries and embassies in Europe. A...
The Impacts of Data Loss on Your Organization – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini What are the causes of Data Loss and which are their impact on your organization? In today’s digital age, data...
CISA adds Samsung and D-link bugs to its Known Exploited Vulnerabilities catalog – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini US CISA added actively exploited Samsung and D-Link vulnerabilities to its Known Exploited Vulnerabilities catalog. US Cybersecurity and Infrastructure Security...
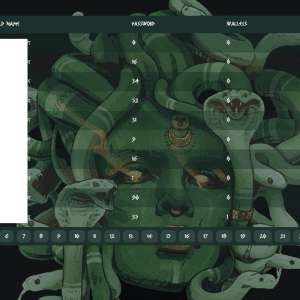
New Windows Meduza Stealer targets tens of crypto wallets and password managers – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers spotted a new Windows information stealer called Meduza Stealer, the authors employ sophisticated marketing strategies to promote it. The Meduza...
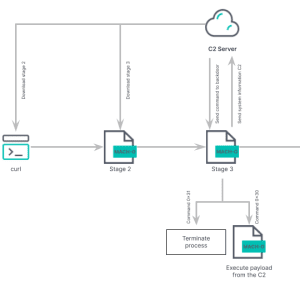
Experts detected a new variant of North Korea-linked RUSTBUCKET macOS malware – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers spotted a new version of the RustBucket Apple macOS malware that supports enhanced capabilities. Researchers from the Elastic Security...
How to add the Docker Scout feature to the Docker CLI – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Jack Wallen on July 3, 2023, 9:38 AM EDT How to add the Docker Scout feature to the Docker CLI In this...
IT Physical Security Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: This policy will help your organization safeguard its hardware, software and data from exposure to persons (internal or external) who could intentionally...
Celebrating Arkose Labs’ Net Promoter Score of 100 for Q2 2023 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Patrice Boffa A Testament to Our Customer Success Team’s Dedication We are thrilled to announce that Arkose Labs has achieved an exceptional...
BSidesSF 2023 – Nika Korchok Wakulich – MTV Reboot — My Super Sweet 16-Bit Malware ~ *MS-DOS Edition* ~ [TSR Remix] – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
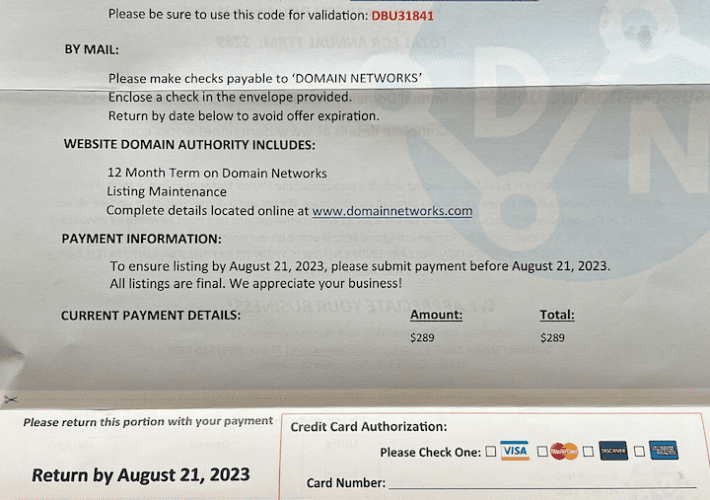
Who’s Behind the DomainNetworks Snail Mail Scam? – Source: securityboulevard.com
Source: securityboulevard.com – Author: BrianKrebs If you’ve ever owned a domain name, the chances are good that at some point you’ve received a snail mail letter...
Google To Replace the “Padlock Icon” with the “Tune Icon” in Chrome 117 Version – Source: securityboulevard.com
Source: securityboulevard.com – Author: SSLWiki Chrome’s “Padlock Icon” is to be replaced by “Tune Icon” in the Latest Version 117, According to Google Google recently announced...
How to Show the Efficiency of a Vulnerability Management Program – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michelle Ofir Geveye What is Vulnerability Management? Vulnerability management is a critical element of information security. With cyber-attacks and data breaches increasing...
Self-Driving Cars Are Surveillance Cameras on Wheels – Source: securityboulevard.com
Source: securityboulevard.com – Author: Bruce Schneier Police are already using self-driving car footage as video evidence: While security cameras are commonplace in American cities, self-driving cars...
MOVEit Cyberattack, The Problem with Password Rotations, Military Alert on Free Smartwatches – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tom Eston Several major organizations, including British Airways and the BBC, fell victim to the recent MOVEit cyberattack. We discuss the alarming...
Choosing Between Self-Managed and Service-Based SSO Solutions: A Comprehensive Comparison – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepak Gupta In today’s interconnected digital landscape, secure and seamless access to multiple applications and systems is crucial for organizations of all...
Massive Data Breach Affects UK Hospital Group – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Andreea Chebac The BlackCat ransomware group claims they have breached Barts Health NHS Trust and stolen seven terabytes of internal documents. On...
BlackCat Ransomware Gang to Launch Malicious WinSCP Ads – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Andreea Chebac The BlackCat ransomware group launched a malvertising campaign to push Cobalt Strike. They put up advertisements to attract people to...

















![bsidessf-2023-–-nika-korchok-wakulich-–-mtv-reboot-—-my-super-sweet-16-bit-malware-~-*ms-dos-edition*-~-[tsr-remix]-–-source:-securityboulevard.com](https://ciso2ciso.com/wp-content/uploads/2023/07/67876/bsidessf-2023-nika-korchok-wakulich-mtv-reboot-my-super-sweet-16-bit-malware-ms-dos-edition-tsr-remix-source-securityboulevard-com-710x500.jpg)