Source: www.securityweek.com – Author: Eduard Kovacs Energy giants Schneider Electric and Siemens Energy have confirmed being targeted by a ransomware group in the recent campaign exploiting...
Month: June 2023
Anatsa Banking Trojan Delivered via Google Play Targets Android Users in US, Europe – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Android users in at least five countries have been targeted with the Anatsa banking trojan via malicious droppers uploaded to...
Microsoft Sysmon now detects when executables files are created – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Microsoft has released Sysmon 15, converting it into a protected process and adding the new ‘FileExecutableDetected’ option to log when...
Exploit released for new Arcserve UDP auth bypass vulnerability – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Data protection vendor Arcserve has addressed a high-severity security flaw in its Unified Data Protection (UDP) backup software that can...
Linux version of Akira ransomware targets VMware ESXi servers – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The Akira ransomware operation uses a Linux encryptor to encrypt VMware ESXi virtual machines in double-extortion attacks against companies worldwide....
Microsoft fixes Windows bug causing File Explorer freezes – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft has addressed a known issue causing File Explorer on Windows 11 and Windows Server systems after viewing a file’s...
Brave Browser boosts privacy with new local resources restrictions – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The Brave team has announced that the privacy-centric browser will soon introduce new restriction controls allowing users to specify how...
NPM ecosystem at risk from “Manifest Confusion” attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The NPM (Node Package Manager) registry suffers from a security lapse called “manifest confusion,” which undermines the trustworthiness of packages...
The Current State of Business Email Compromise Attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sponsored by Specops Software Business Email Compromise (BEC) poses a growing threat to businesses of all sizes. As BEC attacks have almost...
Microsoft Teams outage blocks access to web and desktop clients – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft is investigating an ongoing outage blocking customers from accessing and using the Microsoft Teams communication platform via web and...
8Base ransomware gang escalates double extortion attacks in June – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A 8Base ransomware gang is targeting organizations worldwide in double-extortion attacks, with a steady stream of new victims since the...
Busted ‘secure’ EncroChat messaging service leads to over 6,500 arrests by police – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Back in 2020, law enforcement agents across Europe had a major breakthrough in their fight against organised crime. They managed...
Alert: New Electromagnetic Attacks on Drones Could Let Attackers Take Control – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 28, 2023Ravie LakshmananFirmware Security / Tech Drones that don’t have any known security weaknesses could be the target of electromagnetic...
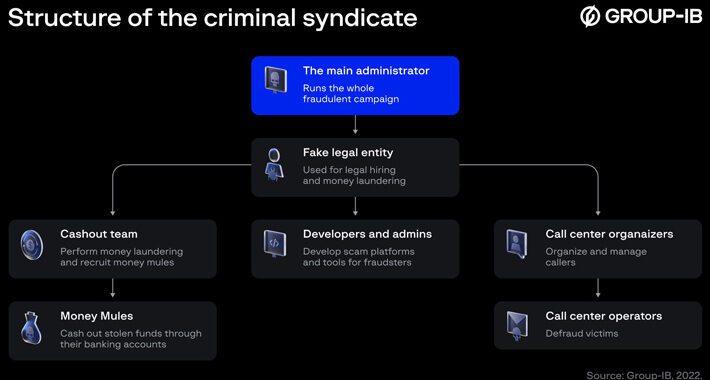
CryptosLabs Scam Ring Targets French-Speaking Investors, Rakes in €480 Million – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 28, 2023Ravie LakshmananCyber Crime / Cryptocurrency Cybersecurity researchers have exposed the workings of a scam ring called CryptosLabs that’s estimated...
The Complete Active Directory Security Handbook – Exploitation – Detection and Migitation Strategies by PICUS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Stalkerware Vendor Hacked – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier The stalkerware company LetMeSpy has been hacked: TechCrunch reviewed the leaked data, which included years of victims’ call logs and...
Typing Incriminating Evidence in the Memo Field – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier Don’t do it: Recently, the manager of the Harvard Med School morgue was accused of stealing and selling human body...
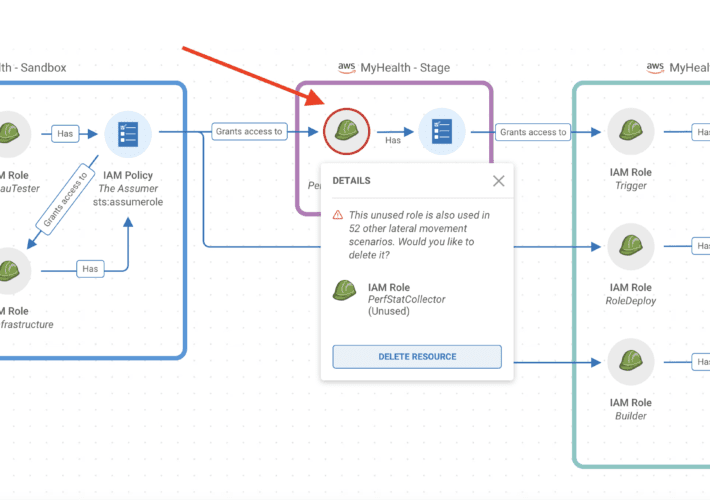
Reduce Risk Efficiently & Save Time with Prioritized Actions – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tally Shea Reading Time: 7 minutes Let’s establish the problem: practitioners are experiencing alert fatigue – desensitized, overwhelmed, and unable to manage...
Ironic: LetMeSpy Spyware Hackers Were Hacked (by Hackers) – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings Content warning: Abuse, stalking, controlling behavior. LetMeSpy is a hacking tool used for stalking and spying on spouses, although its...
BSidesSF 2023 – Reed Loden, Tom Alcock, Mike McBryde, Coleen Coolidge, Kevin Hanaford – First Security Hire: Building A Security Roadmap And Team From Scratch – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Hot Topics Reduce Risk Efficiently & Save Time with Prioritized Actions Ironic: LetMeSpy Spyware Hackers Were Hacked (by Hackers) BSidesSF...
Look Ma, G2 Awarded Us with a Giant Stack of Badges – Source: securityboulevard.com
Source: securityboulevard.com – Author: Robert Hilson We don’t like to toot our own horn here at Apptega. But when our customers do it for us –...
Sowing Chaos and Reaping Rewards in Confluence and Jira – Source: securityboulevard.com
Source: securityboulevard.com – Author: Craig Wright Introduction Let me paint a picture for you. You’re on a red team operation, operating from your favorite C2, and...
New Capabilities in Fairwinds Insights: Custom Fields and Issue Types – Source: securityboulevard.com
Source: securityboulevard.com – Author: Liz Coolman If you are managing development teams using Kubernetes, you need to be able to easily find, triage, and fix problems...
Seceon Hires Peter Christou to Drive UK and EU Expansion – Source: securityboulevard.com
Source: securityboulevard.com – Author: Pushpendra Mishra Seceon, the pioneer of the first cybersecurity platform that augments and automates security operations services for MSPs and MSSPs, with an AI...
How to Manage Security Risks in a Supply Chain – Source: securityboulevard.com
Source: securityboulevard.com – Author: Cavelo Blog As your business becomes increasingly reliant on vendors, suppliers and providers to support operations or deliver goods and services, managing...
Frontend Developers: Security Champions of the New Age – Source: securityboulevard.com
Source: securityboulevard.com – Author: Or Weis Web development has undergone dramatic changes since its inception. However, one pervasive problem still exists: Frontend developers are still required...
European Cyber Agency Remains Underfunded – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cybercrime , Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime ENISA Chief Says Lack of Appropriate Funding Continues to Be...
Application Security Testing vs. API Security Testing – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 API Security How They Differ & How Noname Security Active Testing Helps Your Business Shift Left Shay Levi • June 27,...
Cisco XDR: Making Defenders’ Lives Better – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cisco connected the world; who better to defend it? This is the mindset Carlos Diaz brings to the new Cisco XDR...
Astrix Security Raises $25M to Protect Nonhuman Identities – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Identity & Access Management , Next-Generation Technologies & Secure Development , Security Operations Cash Will Allow Astrix to Bring Threat Detection,...