Source: www.lastwatchdog.com – Author: bacohido Eden Prairie, Minn., June 22, 2023 — Malicious emails have reached a crescendo in 2023 according to the latest report from...
Month: June 2023
US Military Personnel Warned of Malicious Smartwatches – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Service members across the US military have reported receiving smartwatches unsolicited in the mail. These smartwatches have Wi-Fi auto-connect capabilities and can...
OpenSSH Trojan Campaign Targets IoT and Linux Systems – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security researchers have discovered a sophisticated attack campaign that exploits custom and open-source tools to target Linux-based systems and Internet of...
USB Drives Used as Trojan Horses By Camaro Dragon – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 New versions of Chinese espionage malware have been observed spreading rapidly through infected USB drives. The malicious software tools were discovered...
ITDR Combines and Refines Familiar Cybersecurity Approaches – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jonathan Care, Contributing Writer, Dark Reading The advantages of using proactive approaches to identify threats before the attackers can cause too much...
NSA: BlackLotus BootKit Patching Won’t Prevent Compromise – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading The US National Security Agency (NSA) is urging systems administrators to go beyond patching in...
Suspicious Smartwatches Mailed to US Army Personnel – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The US Army’s Criminal Investigation Division (CID) is warning service members to look out for unsolicited smartwatches arriving in...
Microsoft Teams Attack Skips the Phish to Deliver Malware Directly – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading A bug in the latest version of Microsoft Teams allows for external sources to send files to...
Why Legacy System Users Prioritize Uptime Over Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Evan Schuman, Contributing Writer, Dark Reading Dirk Hodgson, the director of cybersecurity for NTT Australia, tells a story. He once worked with...
Black Hat Asia 2023: Cybersecurity Maturity and Concern in Asia – Source: www.darkreading.com
Source: www.darkreading.com – Author: Zhiyee Teh, Research Associate, Cybersecurity, Omdia Cybersecurity maturity is observed to be nascent among organizations in Asia, with opportunities to make headway...
How Government Contractors & Agencies Should Navigate New Cyber Rules – Source: www.darkreading.com
Source: www.darkreading.com – Author: Matt Malarkey, VP, Strategic Alliances, Titania There are kinks in the chain — the supply chain. And after several high-profile cybersecurity breaches...
Millions of Repos on GitHub Are Potentially Vulnerable to Hijacking – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Millions of enterprise software repositories on GitHub are vulnerable to repojacking, a relatively simple kind of...
Deception Technologies Have a Maturity Problem – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading INFOSEC23 — London — Deception technologies can offer a better method to detect attackers in your...
Public exploit is now available for Cisco AnyConnect VPN client – Source: www.csoonline.com
Source: www.csoonline.com – Author: Attackers could elevate privileges on systems with the vulnerable, unpatched Cisco clients, possibly taking full control. An easy-to-use exploit was publicly released...
BrandPost: Study finds Zscaler can save $2.1 million annually – Source: www.csoonline.com
Source: www.csoonline.com – Author: About | See why Zscaler’s proxy-based architecture is built on an industry-leading SSE framework to deliver superior security to secure today’s modern...
Millions of GitHub repositories vulnerable to RepoJacking: Report – Source: www.csoonline.com
Source: www.csoonline.com – Author: AquaSec analyzed a sample of 1% of GitHub repositories and found that about 37,000 of them are vulnerable to RepoJacking, including the...
New CISO appointments 2023 – Source: www.csoonline.com
Source: www.csoonline.com – Author: Keep up with news of CSO, CISO, and other senior security executive appointments. Rawpixel / Getty Images The upper ranks of corporate...
Cybercrime Group ‘Muddled Libra’ Targets BPO Sector with Advanced Social Engineering – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 23, 2023Ravie LakshmananSocial Engineering / Phishing A threat actor known as Muddled Libra is targeting the business process outsourcing (BPO)...
MDM: Balancing the Need for User Privacy, Corporate Control – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 In today’s hybrid work environment, mobile device management and security are more important than ever before. Apple has a reputation for...
SEO Poisoning Attacks on Healthcare Sector Rising, HHS Warns – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Account Takeover Fraud , Fraud Management & Cybercrime , Social Engineering Search Scams Luring Users to Malware-Infected Sites Are Often Tricky...
LIVE Webinar | Resilience, Recovery and Contingency: Database Challenge Secrets – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Michael Fal Director, Database Solution Architecture, Rubrik Mike Fal (@mike_fal) is a specialist in data management technologies. As a community advocate,...
EU to Push Ahead With Data Act Despite Criticism – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 General Data Protection Regulation (GDPR) , Governance & Risk Management , Privacy EU’s Industry Chief Says Europe’s ‘Assertion Is Not Protectionism’...
Hackers Targeting Linux and IoT Devices for Crytomining – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cryptocurrency Fraud , Cybercrime , Fraud Management & Cybercrime Attackers Deploy Trojanized OpenSSH Version for Device Takeover, Microsoft Says Mihir Bagwe...
What to know about the MoveIT hack – Week in security with Tony Anscombe – Source: www.welivesecurity.com
Source: www.welivesecurity.com – Author: Editor The US government has now announced a bounty of $10 million for intel linking the Cl0p ransomware gang to a foreign...
SMS Phishers Harvested Phone Numbers, Shipment Data from UPS Tracking Tool – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs The United Parcel Service (UPS) says fraudsters have been harvesting phone numbers and other information from its online shipment tracking tool...
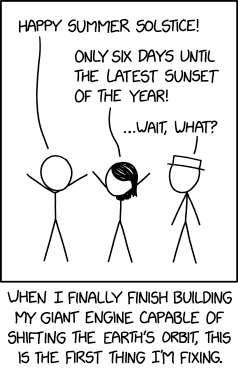
Randall Munroe’s XKCD ‘Summer Solstice’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
IRONSCALES Brings Generative AI to Email Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard IRONSCALES this week made available in beta a tool that leverages OpenAI’s generative pre-trained transformer (GPT) technology to make it...
Protecting Your Enterprise Data from a Coming Cyber Storm – Source: securityboulevard.com
Source: securityboulevard.com – Author: Thomas Stoesser There’s no better way to understand the biggest threats to enterprise cybersecurity than spending a few days at Infosecurity Europe....
BSidesSF 2023 – Zur Ulianitzky, Bill Ben Haim – Advanced Attack Vectors In Azure Environments – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...