Source: www.govinfosecurity.com – Author: 1 Governance & Risk Management , Incident & Breach Response , Privacy Lokker CEO Ian Cohen on Growing Health Information Concerns With...
Day: May 30, 2023
Sports Warehouse Fined $300,000 Over Payment Card Data Theft – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Audit , Card Not Present Fraud , Cybercrime Data Breach Exposed Nearly 20 Years of ‘Indefinitely’ Stored Payment Card Data Mathew...
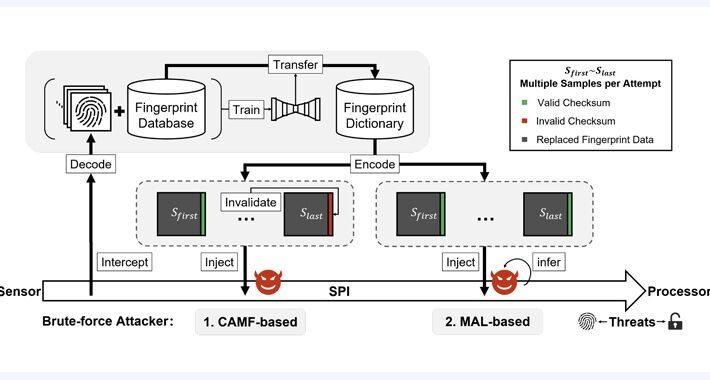
New BrutePrint Attack Lets Attackers Unlock Smartphones with Fingerprint Brute-Force – Source:thehackernews.com
Source: thehackernews.com – Author: . May 29, 2023Ravie LakshmananAuthentication / Mobile Security Researchers have discovered an inexpensive attack technique that could be leveraged to brute-force fingerprints...
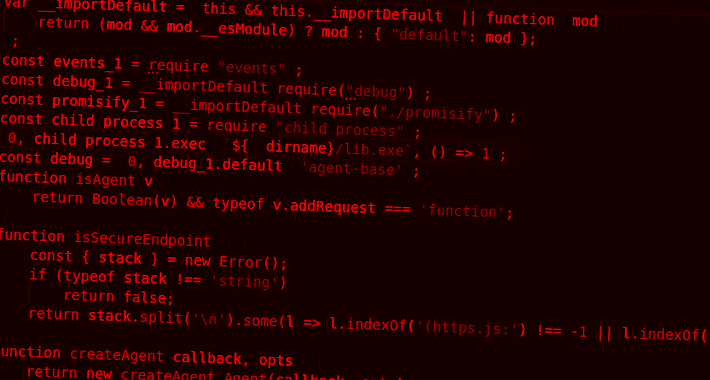
Developer Alert: NPM Packages for Node.js Hiding Dangerous TurkoRat Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Two malicious packages discovered in the npm package repository have been found to conceal an open source information stealer malware called...
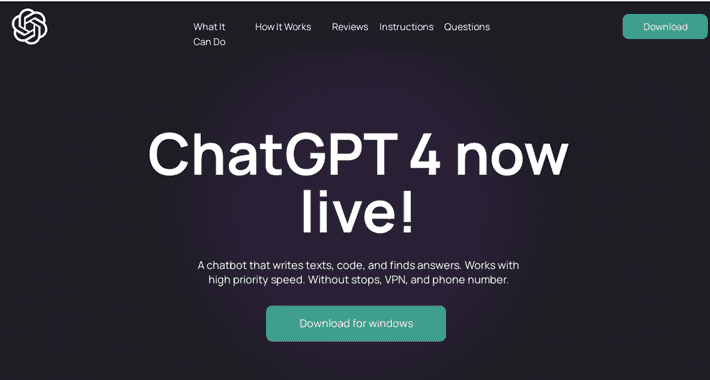
Searching for AI Tools? Watch Out for Rogue Sites Distributing RedLine Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . May 19, 2023Ravie LakshmananArtificial Intelligence / Cyber Threat Malicious Google Search ads for generative AI services like OpenAI ChatGPT and Midjourney...
WebKit Under Attack: Apple Issues Emergency Patches for 3 New Zero-Day Vulnerabilities – Source:thehackernews.com
Source: thehackernews.com – Author: . May 19, 2023Ravie LakshmananZero-Day / Endpoint Security Apple on Thursday rolled out security updates to iOS, iPadOS, macOS, tvOS, watchOS, and...
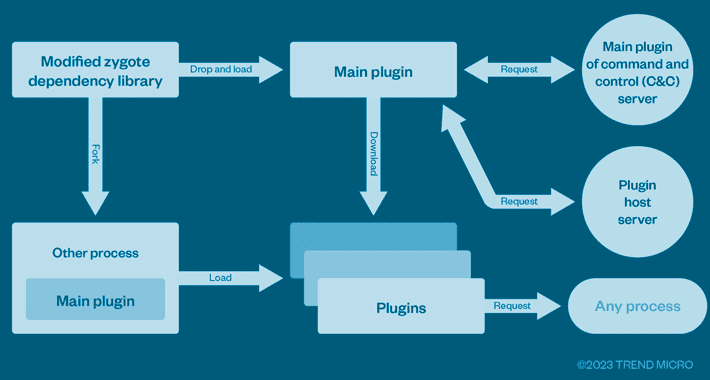
This Cybercrime Syndicate Pre-Infected Over 8.9 Million Android Phones Worldwide – Source:thehackernews.com
Source: thehackernews.com – Author: . A cybercrime enterprise known as Lemon Group is leveraging millions of pre-infected Android smartphones worldwide to carry out their malicious operations,...