Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/05/bsidessf-2023-abhinav-sp-making-of-the-bsides-sf-astronaut-badge/ Category & Tags: Security Bloggers Network,appsec education,BsidesSF,BSidesSF...
Day: May 21, 2023
BSidesSF 2023 – Rami McCarthy, Lea Snyder, Hasnain Lakhani, Kurt Boberg – Level Up Your Career: A Panel on Staff+ Engineering – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » BSidesSF 2023 – Rami McCarthy, Lea Snyder, Hasnain Lakhani, Kurt Boberg...
Open-Source Infostealer RAT Hidden in Malicious NPM Packages – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Application Security , Next-Generation Technologies & Secure Development , Threat Intelligence TurkoRat Capable of Credential Harvesting, Possesses Features Like Wallet Grabber...
Google pushes .zip and .mov domains onto the Internet, and the Internet pushes back – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 WHAT COULD POSSIBLY GO WRONG? — Will new TLDs undo decades of work to stop malicious links? Dan Goodin – May...
Cybersecurity Leaders Suffer Burnout as Pressures of the Job Intensify – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 Relentless cyberattacks and pressure to fix security gaps despite budget constraints are raising the stress levels of corporate cyber leaders and...
Microsoft Teams is being hacked to crack Office 365 accounts – here’s how to stay safe – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 Home News Computing (Image credit: Microsoft) Researchers have discovered more ways to abuse Microsoft Teams to steal Office 365 user credentials...
Pentagon Hacking Fears Fueled by Microsoft’s Monopoly on Military IT – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 The Cybersecurity and Infrastructure Security Agency (CISA) released a shocking report on February 23, 2023, revealing the results from a red...
Identity-focused attacks remain the most vulnerable entry point to an organization – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 The Cybersecurity and Infrastructure Security Agency (CISA) released a shocking report on February 23, 2023, revealing the results from a red...
Selena Larson on how cybercriminals use threat intelligence – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 In this Risky Business News sponsor interview Tom Uren asks Proofpoint’s Selena Larson about how threat actors reacted en masse after...
Open-Source Infostealer RAT Hidden in Malicious NPM Packages – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Application Security , Next-Generation Technologies & Secure Development , Threat Intelligence TurkoRat Capable of Credential Harvesting, Possesses Features Like Wallet Grabber...
PyPI temporarily pauses new users, projects amid high volume of malware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ax Sharma PyPI, the official third-party registry of open source Python packages has temporarily suspended new users from signing up, and new...
Cloned CapCut websites push information stealing malware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A new malware distribution campaign is underway impersonating the CapCut video editing tool to push various malware strains to unsuspecting...
HP rushes to fix bricked printers after faulty firmware update – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan HP is working to address a bad firmware update that has been bricking HP Office Jet printers worldwide since it was...
npm packages caught serving TurkoRAT binaries that mimic NodeJS – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ax Sharma Researchers have discovered multiple npm packages named after NodeJS libraries that even pack a Windows executable that resembles NodeJS but instead...
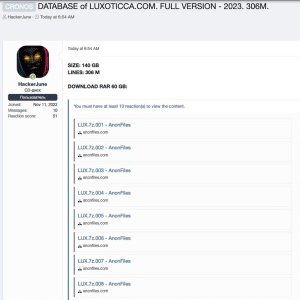
2021 data breach exposed data of 70 Million Luxottica customers – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Luxottica has finally confirmed the 2021 data breach that exposed the personal information of 70 million customers. Luxottica Group S.p.A. is...
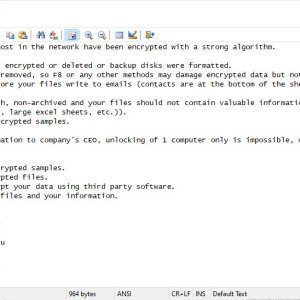
Cybercrime gang FIN7 returned and was spotted delivering Clop ransomware – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Cybercriminal gang FIN7 returned with a new wave of attacks aimed at deploying the Clop ransomware on victims’ networks. Researchers...
US CISA warns of a Samsung vulnerability under active exploitation – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini US CISA added the vulnerability CVE-2023-21492 flaw affecting Samsung devices to its Known Exploited Vulnerabilities Catalog. US CISA added the...