SAP Fixes Five Critical Vulnerabilities With Newly Released Security UpdateSoftware vendor SAP has released security updates to fix 19 vulnerabilities, five of which rated as critical....
Day: March 15, 2023
LockBit Ransomware Claims to Have Stolen SpaceX Data from One of Its Contractors
LockBit Ransomware Claims to Have Stolen SpaceX Data from One of Its ContractorsAfter breaching the systems of Maximum Industries, the LockBit ransomware group claims to have...
Microsoft Patch Tuesday, March 2023 Edition
Microsoft Patch Tuesday, March 2023 EditionMicrosoft on Tuesday released updates to quash at least 74 security bugs in its Windows operating systems and software. Two of...
Closing the Pay Gap: How Pay Parity Continues to Transform Our Workplace
Closing the Pay Gap: How Pay Parity Continues to Transform Our Workplace Four years ago, we achieved something that few companies had — pay parity, by...
Get 3 years of rock-solid protection with Surfshark VPN for $83.99
Get 3 years of rock-solid protection with Surfshark VPN for $83.99The service is rated at 8/10 stars by The VPN Lab. The post Get 3 years...
For credentials, these are the new Seven Commandments for zero trust
For credentials, these are the new Seven Commandments for zero trustWith backing from major firms, credential security company Beyond Identity has launched the Zero Trust Authentication...
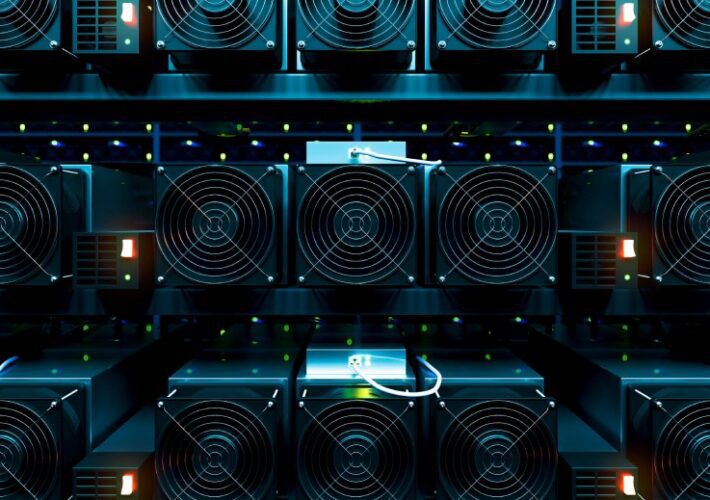
First-known Dero cryptojacking operation seen targeting Kubernetes
First-known Dero cryptojacking operation seen targeting KubernetesThe first known cryptojacking operation mining the Dero coin has been found targeting vulnerable Kubernetes container orchestrator infrastructure with exposed...
ChatGPT may be a bigger cybersecurity risk than an actual benefit
ChatGPT may be a bigger cybersecurity risk than an actual benefitChatGPT made a splash with its believable AI-generated responses. However, it can help threat actors create...
ChipMixer platform seized for laundering ransomware payments, drug sales
ChipMixer platform seized for laundering ransomware payments, drug salesAn international law enforcement operation has seized the cryptocurrency mixing service 'ChipMixer' which is said to be used...
Healthcare provider ILS warns 4.2 million people of data breach
Healthcare provider ILS warns 4.2 million people of data breachIndependent Living Systems (ILS), a Miami-based healthcare administration and managed care solutions provider, suffered a data breach...
US federal agency hacked using old Telerik bug to steal data
US federal agency hacked using old Telerik bug to steal dataLast year, a U.S. federal agency's Microsoft Internet Information Services (IIS) web server was hacked by...
Critical Microsoft Outlook bug PoC shows how easy it is to exploit
Critical Microsoft Outlook bug PoC shows how easy it is to exploitSecurity researchers have shared technical details for exploiting a critical Microsoft Outlook vulnerability for Windows (CVE-2023-23397)...
Unleash the Firewall across the Hybrid Multi-Cloud
Unleash the Firewall across the Hybrid Multi-CloudPost ContentRead MoreDataBreachToday.com RSS Syndication
Illicit Crypto Miners Find a New Fave in Privacy Coin Dero
Illicit Crypto Miners Find a New Fave in Privacy Coin DeroCrowdStrike Finds Dero Cryptojacking Operations on Kubernetes ClusterThreat actors who mine digital assets using other people's...
Rubrik Breached Via Zero-Day Attack Exploiting GoAnywhere
Rubrik Breached Via Zero-Day Attack Exploiting GoAnywhereCompany Says Data Breach Ties to Fortra Software Exploit; Nothing Sensitive StolenCybersecurity software giant Rubrik has joined the ranks of...
Proof of Concept: Is New US Cyber Strategy Really Viable?
Proof of Concept: Is New US Cyber Strategy Really Viable?Panel Discusses Political and Policy Realities of Mandates, Vendor Liability, CostsIn the latest "Proof of Concept" panel...
Microsoft lanza parches para 80 nuevas fallas de seguridad, dos bajo ataque activo
Microsoft lanza parches para 80 nuevas fallas de seguridad, dos bajo ataque activoLa actualización del martes de parches de Microsoft para marzo de 2023 se está...
SYS01stealer: New Threat Using Facebook Ads to Target Critical Infrastructure Firms
SYS01stealer: New Threat Using Facebook Ads to Target Critical Infrastructure FirmsCybersecurity researchers have discovered a new information stealer dubbed SYS01stealer targeting critical government infrastructure employees, manufacturing...
Microsoft Rolls Out Patches for 80 New Security Flaws — Two Under Active Attack
Microsoft Rolls Out Patches for 80 New Security Flaws — Two Under Active AttackMicrosoft's Patch Tuesday update for March 2023 is rolling out with remediations for...
Microsoft fixes two 0-days on Patch Tuesday – update now!
Microsoft fixes two 0-days on Patch Tuesday – update now!An email you haven't even looked at yet could be used to trick Outlook into helping crooks...
Splunk SOAR Cyber Security: A Comprehensive Overview
Splunk SOAR Cyber Security: A Comprehensive OverviewAre the myriad of cyber security threats overwhelming your Splunk Security SOC team? Are you looking for a way to...
The State of Supply Chain Cybersecurity in 2023
The State of Supply Chain Cybersecurity in 2023Supply chain cybersecurity risks continue to cause concern for companies of all sizes in 2023. These risks are more...
The Top 8 Cloud Application Threats in 2023
The Top 8 Cloud Application Threats in 2023 In this blog post, we'll discuss 8 of the top threats targeting cloud applications in 2023. Taking steps...
Meet Frank Tingle: Values Champion
Meet Frank Tingle: Values Champion The post Meet Frank Tingle: Values Champion appeared first on Security Boulevard. Read MoreSecurity Boulevard The post Meet Frank Tingle:...
USENIX Security ’22 – Bodong Zhao, Zheming Li, Shisong Qin, Zheyu Ma, Ming Yuan, Wenyu Zhu, Zhihong Tian, Chao Zhang – ‘StateFuzz: System Call-Based State-Aware Linux Driver Fuzzing’
USENIX Security ’22 – Bodong Zhao, Zheming Li, Shisong Qin, Zheyu Ma, Ming Yuan, Wenyu Zhu, Zhihong Tian, Chao Zhang – ‘StateFuzz: System Call-Based State-Aware Linux...
Secrets Exposed: How hackers are gaining access to software secrets
Secrets Exposed: How hackers are gaining access to software secrets Until recently, malicious actors who wanted to get their hands on sensitive corporate data or IT systems...
ChatGPT: AI’s Evolving Capabilities and Consequences for Cybersecurity
ChatGPT: AI’s Evolving Capabilities and Consequences for CybersecurityChatGPT has taken the tech world by storm. This super interesting technology responds to queries and exchanges information back-and-forth...
‘Black Skills’ Is Killnet’s Attempt to Form a ‘Private Military Hacking Company’
‘Black Skills’ Is Killnet’s Attempt to Form a ‘Private Military Hacking Company’A clear riff on the growing presence of private military companies in Russia (primarily the...
Why You Need a Team of Ninja Threat Hunters to Protect Your Data
Why You Need a Team of Ninja Threat Hunters to Protect Your DataIn today’s digital age, cyber threats have become a major concern for organizations of...
Two U.S. Men Charged in 2022 Hacking of DEA Portal
Two U.S. Men Charged in 2022 Hacking of DEA PortalTwo U.S. men have been charged with hacking into a U.S. Drug Enforcement Agency (DEA) online portal...