CVE-2022-41622 and CVE-2022-41800 Exploit Detection: RCE Vulnerabilities in F5 BIG-IP and BIG-IQ Products F5 Networks has recently released security advisories addressing two high-severity flaws discovered in...
Year: 2022
Cybersecurity News Round-Up: Week of November 14, 2022
Cybersecurity News Round-Up: Week of November 14, 2022Log4Shell used to mine crypto on U.S. federal computer system, private exchanges of some of Moldova's politicians released in...
Russian Duo Indicted Over E-Book Piracy
Russian Duo Indicted Over E-Book PiracySt Petersburg couple were arrested in ArgentinaLeer másSt Petersburg couple were arrested in Argentina
EDR vs. MDR vs. XDR: A comparison
EDR vs. MDR vs. XDR: A comparisonThe central piece of a good cybersecurity strategy is a reliable detection and response toolset. But, as cybercriminals employ more...
Atlassian fixed 2 critical flaws in Crowd and Bitbucket products
Atlassian fixed 2 critical flaws in Crowd and Bitbucket productsAtlassian addressed this week two critical vulnerabilities impacting its Crowd and Bitbucket products. Atlassian announced the release...
Oops! Meta Security Guards Hacked Facebook Users
Oops! Meta Security Guards Hacked Facebook Users Facebook parent Meta has disciplined or fired at least 25 workers for allegedly hacking into user accounts. The post Oops!...
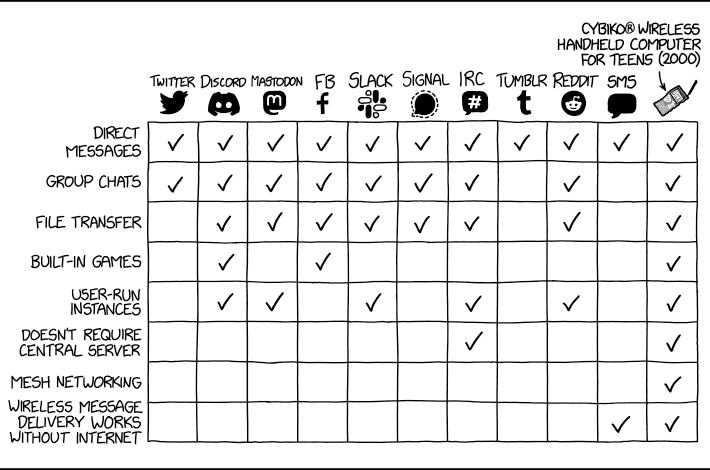
Randall Munroe’s XKCD ‘Feature Comparison’
Randall Munroe’s XKCD ‘Feature Comparison’ via the comic artistry and dry wit of Randall Munroe, resident at XKCD! Permalink The post Randall Munroe’s XKCD ‘Feature Comparison’...
Instagram Credential Phishing Attacks Bypass Microsoft Email Security
Instagram Credential Phishing Attacks Bypass Microsoft Email SecurityThe attack bypassed both SPF and DMARC email authentication checksLeer másThe attack bypassed both SPF and DMARC email authentication...
Shoppers Warned Stay Alert this Black Friday as Hackers Renew Efforts
Shoppers Warned Stay Alert this Black Friday as Hackers Renew EffortsCyber-criminals are exploiting the busy period during both purchase and delivery stagesLeer másCyber-criminals are exploiting the...
First Review of A Hacker’s Mind
First Review of A Hacker’s MindKirkus reviews A Hacker’s Mind: A cybersecurity expert examines how the powerful game whatever system is put before them, leaving it...
India drafts new privacy bill for transfer of personal data internationally
India drafts new privacy bill for transfer of personal data internationallyThe Indian federal government on Friday published a new draft of data privacy laws that would...
Almost half of customers have left a vendor due to poor digital trust: Report
Almost half of customers have left a vendor due to poor digital trust: ReportForty-seven percent of consumers have stopped doing business with a company after losing...
Digital Trust Digest: This Week’s Must-Know News (Nov. 14-18)
Digital Trust Digest: This Week’s Must-Know News (Nov. 14-18)The Digital Trust Digest is a curated overview of the week’s top cybersecurity news. Here's what happened the...
BSidesKC 2022 – Grant Shanklin’s ‘Trouble With The Troubleshooter; A Primer On CVE-2022-30190’
BSidesKC 2022 – Grant Shanklin’s ‘Trouble With The Troubleshooter; A Primer On CVE-2022-30190’Our sincere thanks to BSidesKC 2022 for publishing their outstanding conference videos on the...
S3 Ep109: How one leaked email password could drain your business [Audio + Transcript]
S3 Ep109: How one leaked email password could drain your business [Audio + Transcript]Latest episode - listen now! Cybersecurity news plus loads of great advice...Leer másNaked...
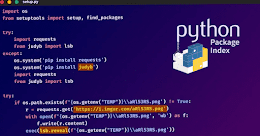
W4SP Stealer Constantly Targeting Python Developers in Ongoing Supply Chain Attack
W4SP Stealer Constantly Targeting Python Developers in Ongoing Supply Chain AttackAn ongoing supply chain attack has been leveraging malicious Python packages to distribute malware called W4SP...
Threat hunting with MITRE ATT&CK and Wazuh
Threat hunting with MITRE ATT&CK and WazuhThreat hunting is the process of looking for malicious activity and its artifacts in a computer system or network. Threat...
Hive Ransomware Attackers Extorted $100 Million from Over 1,300 Companies Worldwide
Hive Ransomware Attackers Extorted $100 Million from Over 1,300 Companies WorldwideThe threat actors behind the Hive ransomware-as-a-service (RaaS) scheme have launched attacks against over 1,300 companies...
Meta Reportedly Fires Dozens of Employees for Hijacking Users’ Facebook and Instagram Accounts
Meta Reportedly Fires Dozens of Employees for Hijacking Users' Facebook and Instagram AccountsMeta Platforms is said to have fired or disciplined over two dozen employees and...
LodaRAT Malware Resurfaces with New Variants Employing Updated Functionalities
LodaRAT Malware Resurfaces with New Variants Employing Updated FunctionalitiesThe LodaRAT malware has resurfaced with new variants that are being deployed in conjunction with other sophisticated malware,...
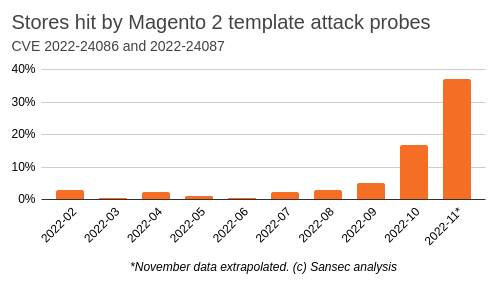
Magento and Adobe Commerce websites under attack
Magento and Adobe Commerce websites under attackResearchers warn of a surge in cyberattacks targeting CVE-2022-24086, a pre-authentication issue impacting Adobe Commerce and Magento stores. In September 2022,...
Two public schools in Michigan hit by a ransomware attack
Two public schools in Michigan hit by a ransomware attackPublic schools in two Michigan counties were forced to halt their activities, including the lessons, after a...
Russian Duo Indicted Over E-Book Piracy
Russian Duo Indicted Over E-Book PiracySt Petersburg couple were arrested in ArgentinaLeer másSt Petersburg couple were arrested in Argentina
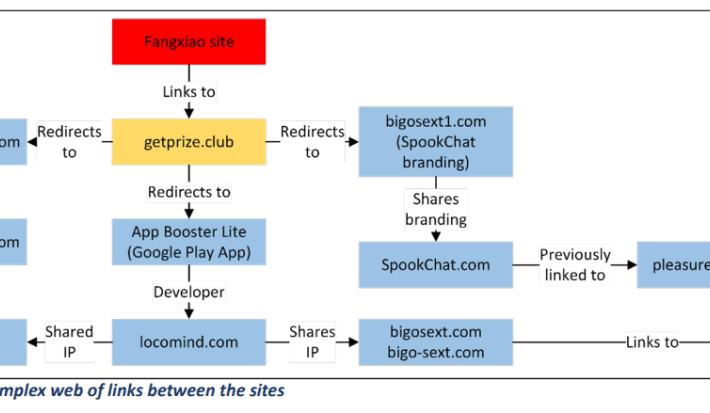
China-based Fangxiao group behind a long-running phishing campaign
China-based Fangxiao group behind a long-running phishing campaignA China-based financially motivated group, tracked as Fangxiao, is behind a large-scale phishing campaign dating back as far as 2019....
Telemedicine Companies Jeopardize Patients` Private Data
Telemedicine Companies Jeopardize Patients` Private DataWebsites offering treatment and support for people dealing with substance use disorders should try harder to protect patients’ data privacy. After conducting...
Noname Security releases Recon attack simulator
Noname Security releases Recon attack simulatorAs breaches increase and companies scramble to go from a defensive to an offensive approach, API-focused Noname Security has launched Recon,...
Python Developers Targeted by W4SP Stealer in an Ongoing Supply Chain Attack
Python Developers Targeted by W4SP Stealer in an Ongoing Supply Chain AttackMalicious Python packages have been used in an ongoing supply chain attack to spread the...
New Shopping Phishing Scam Uses URI Fragmentation to Target U.S. and Canadian Users
New Shopping Phishing Scam Uses URI Fragmentation to Target U.S. and Canadian UsersA highly efficient phishing kit spreads the most among users from the United States...
Heimdal® Recognized as Top Cybersecurity Software by Software Advice in 2022
Heimdal® Recognized as Top Cybersecurity Software by Software Advice in 2022Copenhagen, November 18, 2022 — Heimdal® announced today that Heimdal® Threat Prevention has been recently recognized as a Top Cybersecurity...
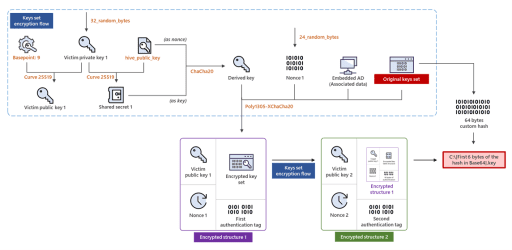
Hive Ransomware extorted over $100M in ransom payments from over 1,300 companies
Hive Ransomware extorted over $100M in ransom payments from over 1,300 companiesHive ransomware operators have extorted over $100 million in ransom payments from over 1,300 companies...