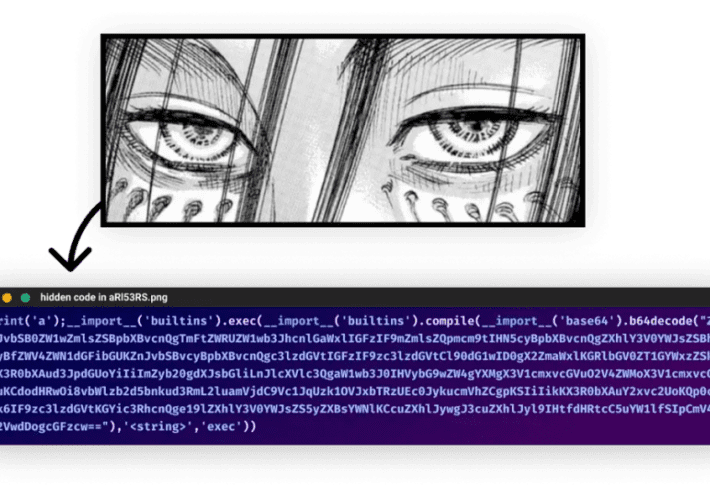
Ongoing supply chain attack targets Python developers with WASP StealerA threat actor tracked as WASP is behind an ongoing supply chain attack targeting Python developers with...
Year: 2022
FBI Reveals: Hive Ransomware Extorted $100M from 1,300 Companies
FBI Reveals: Hive Ransomware Extorted $100M from 1,300 CompaniesThe Federal Bureau of Investigation (FBI) stated that as of November 2022, the infamous Hive ransomware gang has...
What Is Patch Management as a Service? (PMaaS)
What Is Patch Management as a Service? (PMaaS)In today’s business world, data security is more important than ever. With the rise of data breaches and cyberattacks,...
Privileged Access Management (PAM) – PAM in the Cloud vs PAM for the Cloud
Privileged Access Management (PAM) – PAM in the Cloud vs PAM for the CloudIT security teams have always been tasked with securing the on-premises infrastructure or...
4,500 Emails Exposed by AI-powered Platform
4,500 Emails Exposed by AI-powered PlatformAn unprotected Cassandra instance containing user emails, SIP tokens, and physical locations was discovered on October 6th by Cybernews researchers. The...
QBot phishing abuses Windows Control Panel EXE to infect devices
QBot phishing abuses Windows Control Panel EXE to infect devicesPhishing emails distributing the QBot malware are using a DLL hijacking flaw in the Windows 10 Control...
Shop But Don’t Click: Analyst Warns Thanksgiving Con Artists Lurking In Consumer Inboxes
Shop But Don’t Click: Analyst Warns Thanksgiving Con Artists Lurking In Consumer InboxesAccording to Avanan, cybercriminals don’t need an excuse to try and con people out...
Blockchain in Retail Will Soon Become a Universal Concept- Explore the Scenario
Blockchain in Retail Will Soon Become a Universal Concept- Explore the ScenarioBy Koyel Ghosh, Sr. Specialist Content Writer, Allied Market Research, India In the last few...
Top Legacy Active Directory Infrastructure Vulnerabilities and How Attackers See Them
Top Legacy Active Directory Infrastructure Vulnerabilities and How Attackers See ThemBy Tammy Mindel, Security Product Manager at Semperis Microsoft Active Directory (AD) has become a highly...
FBI: Hive ransomware extorted $100M from over 1,300 victims
FBI: Hive ransomware extorted $100M from over 1,300 victimsThe Federal Bureau of Investigation (FBI) said today that the notorious Hive ransomware gang has successfully extorted roughly...
The Numbers Are In: Identity-Based Attacks (Still) Reign Supreme in 2022
The Numbers Are In: Identity-Based Attacks (Still) Reign Supreme in 2022By Greg Notch, CISO, Expel The list of challenges security professionals face will not let up,...
Previously unidentified ARCrypter ransomware expands worldwide
Previously unidentified ARCrypter ransomware expands worldwideA previously unknown 'ARCrypter' ransomware that compromised key organizations in Latin America is now expanding its attacks worldwide. [...]Leer másBleepingComputerA previously...
Microsoft fixes Windows Kerberos auth issues in emergency updates
Microsoft fixes Windows Kerberos auth issues in emergency updatesMicrosoft has released optional out-of-band (OOB) updates to fix a known issue triggering Kerberos sign-in failures and other authentication...
Police force published sexual assault victims’ names and addresses on its website
Police force published sexual assault victims’ names and addresses on its websiteA UK police force has apologised after it published the names and addresses of victims...
Phishing kit impersonates well-known brands to target US shoppers
Phishing kit impersonates well-known brands to target US shoppersA sophisticated phishing kit has been targeting North Americans since mid-September, using lures focused on holidays like Labor...
Researchers Quietly Cracked Zeppelin Ransomware Keys
Researchers Quietly Cracked Zeppelin Ransomware KeysPeter is an IT manager for a technology manufacturer that got hit with a Russian ransomware strain called “Zeppelin” in May...
Atlassian fixes critical command injection bug in Bitbucket Server
Atlassian fixes critical command injection bug in Bitbucket ServerAtlassian has released updates to address critical-severity updates in its centralized identity management platform, Crowd Server and Data Center,...
Privacy, Identity, and Device Protection: Why You Need to Invest in All Three
Privacy, Identity, and Device Protection: Why You Need to Invest in All Three Protecting your devices with antivirus is a great start, yet it’s only one...
Why Everyone Needs a VPN
Why Everyone Needs a VPN You may hear corporate cybersecurity experts hail the benefits of a VPN, or a virtual private network, to keep company information...
Transform Any Place into a Smart Space
Transform Any Place into a Smart SpaceTransform rooms, buildings, and spaces into assets that inform new insights, inspire collaboration, and drive efficiencies through automation and analytics....
Earth Preta Spear-Phishing Governments Worldwide
Earth Preta Spear-Phishing Governments WorldwideWe break down the cyberespionage activities of advanced persistent threat (APT) group Earth Preta, observed in large-scale attack deployments that began in...
Earth Preta Spear-Phishing Governments Worldwide
Earth Preta Spear-Phishing Governments WorldwideWe break down the cyberespionage activities of advanced persistent threat (APT) group Earth Preta, observed in large-scale attack deployments that began in...
Tech news you may have missed: Nov. 10 – 17
Tech news you may have missed: Nov. 10 – 17This week’s trending news features a primer on Industrial IoT, new and upcoming features for Windows users...
Google Search results poisoned with torrent sites via Data Studio
Google Search results poisoned with torrent sites via Data StudioThreat actors are abusing Google's Looker Studio (formerly Google Data Studio) to boost search engine rankings for...
Ransomware attack on CommonSpirit Health could affect 20 million Americans
Ransomware attack on CommonSpirit Health could affect 20 million AmericansHackers are targeting the healthcare industry. Health systems are making progress around cyber security, but a great...
With FTX’s Collapse, Cycle of Cryptocurrency Loss Continues
With FTX's Collapse, Cycle of Cryptocurrency Loss ContinuesMt. Gox Was the First Big Exchange Collapse. I Had a Front-Row Seat.After the collapse of the FTX cryptocurrency...
How to deal with the trauma of the Medibank cyber breach | Andrea Szasz
How to deal with the trauma of the Medibank cyber breach | Andrea SzaszThe weaponisation of private health information can feel like a violation of personal...
Cyberwarfare’s Role in the Next National Defense Strategy
Cyberwarfare's Role in the Next National Defense StrategyDespite the strategic priorities laid out by the Biden administration and initial indicators provided by the Department of Defense,...
Ransomware: Did Law Enforcement Lose Ground Early On?
Ransomware: Did Law Enforcement Lose Ground Early On?A decade ago, ransomware was one of the internet’s petty street crimes, but it has now evolved into a...
OpenSource World – The Way We Live in the Modern App World
OpenSource World - The Way We Live in the Modern App WorldContenido de la entradaLeer másDataBreachToday.com RSS Syndication