Cisco Firepower Management Center Software Command Injection VulnerabilitiesMultiple vulnerabilities in the web management interface of Cisco Firepower Management Center (FMC) Software could allow an authenticated, remote...
Month: December 2022
Cisco Firepower Management Center Software Command Injection Vulnerabilities
Cisco Firepower Management Center Software Command Injection VulnerabilitiesMultiple vulnerabilities in the web management interface of Cisco Firepower Management Center (FMC) Software could allow an authenticated, remote...
New Actively Exploited Zero-Day Vulnerability Discovered in Apple Products
New Actively Exploited Zero-Day Vulnerability Discovered in Apple ProductsApple on Tuesday rolled out security updates to iOS, iPadOS, macOS, tvOS, and Safari web browser to address...
GUEST ESSAY: ‘Initial access brokers’ — IABs — specialize in enabling surreptitious access
GUEST ESSAY: ‘Initial access brokers’ — IABs — specialize in enabling surreptitious accessCybercrime is a big business. And like any other large industry, specialization has emerged....
A tell-all conversation: The biggest cloud security trends, challenges & solutions
A tell-all conversation: The biggest cloud security trends, challenges & solutionsEXECUTIVE SUMMARY: In this dynamic tell-all conversation, excerpted from The TechArena podcast, VP of Cloud Security...
Hackers Actively Exploiting Citrix ADC and Gateway Zero-Day Vulnerability
Hackers Actively Exploiting Citrix ADC and Gateway Zero-Day VulnerabilityThe U.S. National Security Agency (NSA) on Tuesday said a threat actor tracked as APT5 has been actively exploiting a...
Why PCI DSS 4.0 Should Be on Your Radar in 2023
Why PCI DSS 4.0 Should Be on Your Radar in 2023Protecting customer data is critical for any business accepting online payment information. The Payment Card Industry...
How to Protect Yourself From Identity Theft After a Data Breach
How to Protect Yourself From Identity Theft After a Data Breach Did you just get word that your personal information may have been caught up in...
Know Your Superpower: Brenda’s McAfee Journey
Know Your Superpower: Brenda’s McAfee Journey Our How I Got Here series spotlights the stories of McAfee team members who have successfully grown their careers. Read more about...
Ransomware Attackers Use Microsoft-Signed Drivers to Gain Access to Systems
Ransomware Attackers Use Microsoft-Signed Drivers to Gain Access to SystemsMicrosoft on Tuesday disclosed it took steps to implement blocking protections and suspend accounts that were used...
Can Thieves Steal Identities With Only a Name and Address?
Can Thieves Steal Identities With Only a Name and Address? Can thieves steal identities with only a name and address? In short, the answer is “no.”...
How to Browse Privately on Your Phone
How to Browse Privately on Your Phone Your phone is likely a daily companion, giving you access to work emails, chats with friends, weather reports, and...
New GoTrim Botnet Attempting to Break into WordPress Sites’ Admin Accounts
New GoTrim Botnet Attempting to Break into WordPress Sites' Admin AccountsA new Go-based botnet has been spotted scanning and brute-forcing self-hosted websites using the WordPress content...
Six Charged in Mass Takedown of DDoS-for-Hire Sites
Six Charged in Mass Takedown of DDoS-for-Hire SitesThe U.S. Department of Justice (DOJ) today seized four-dozen domains that sold “booter” or “stresser” services — businesses that...
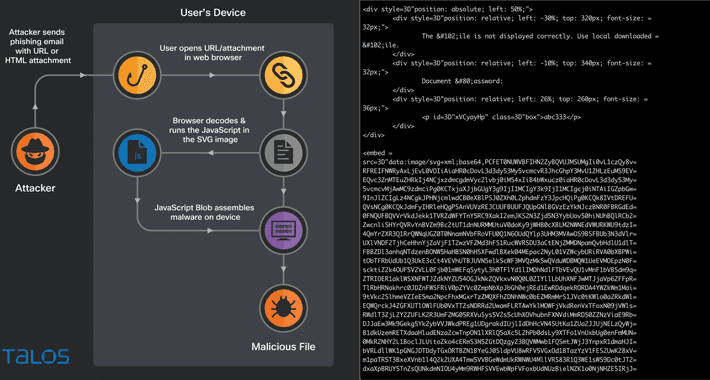
Hacking Using SVG Files to Smuggle QBot Malware onto Windows Systems
Hacking Using SVG Files to Smuggle QBot Malware onto Windows SystemsPhishing campaigns involving the Qakbot malware are using Scalable Vector Graphics (SVG) images embedded in HTML email attachments....
Social Blade Confirms Data Breach Exposing PII on the Dark Web
Social Blade Confirms Data Breach Exposing PII on the Dark WebThe company confirmed the data does not include any credit card informationLeer másThe company confirmed the...
NIST says you better dump weak SHA-1 … by 2030
NIST says you better dump weak SHA-1 ... by 2030How about right now? Right now is good The US National Institute of Standards and Technology (NIST)...
This year’s hottest tech: Related privacy concerns
This year’s hottest tech: Related privacy concerns The holiday season is upon us, and many of us are looking forward to soon unwrapping the latest and...
Know Your Gamer: The Need for Identity Verification in the Gaming Industry 2023
Know Your Gamer: The Need for Identity Verification in the Gaming Industry 2023Isn’t it time the video gaming business rectified its KYG (Know Your Gamer) issue...
What are RUA and RUF in DMARC?
What are RUA and RUF in DMARC?DMARC, or Domain-based Messaging Authentication, Reporting, and Conformance is an […] The post What are RUA and RUF in DMARC?...
Instagram: Are You a Pig?
Instagram: Are You a Pig?I thought this street edit of an Instagram billboard was pretty clever: The post Instagram: Are You a Pig? appeared first on...
Facebook Cracks Down on Spyware Vendors from U.S., China, Russia, Israel, and India
Facebook Cracks Down on Spyware Vendors from U.S., China, Russia, Israel, and IndiaMeta Platforms disclosed that it took down no less than 200 covert influence operations...
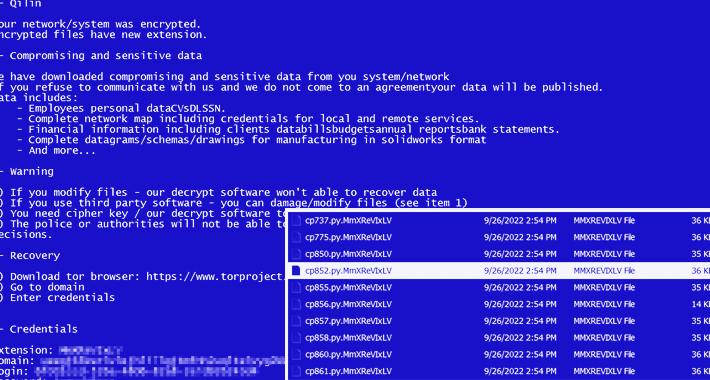
New Agenda Ransomware Variant, Written in Rust, Aiming at Critical Infrastructure
New Agenda Ransomware Variant, Written in Rust, Aiming at Critical InfrastructureA Rust variant of a ransomware strain known as Agenda has been observed in the wild, making it...
Palo Alto’s Biggest Bets Around AppSec, SecOps, SASE & Cloud
Palo Alto's Biggest Bets Around AppSec, SecOps, SASE & CloudFrom Medical IoT Security to AppSec Testing, Here's Where Palo Alto Is Going All-InStaying one step ahead...
X5 Firewall Practices to Prevent a Data Breach
X5 Firewall Practices to Prevent a Data BreachHow to Get the Most Out of Firewall Management ProcessesExperiencing an attack is only a matter of time. Most...
Will Third-Party App Stores Play With Apple’s Walled Garden?
Will Third-Party App Stores Play With Apple's Walled Garden?EU Legislation Says Mobile Platforms Must Grant Access to Third-Party Apps, StoresApple is advancing plans to allow Europeans...
Next-Gen Cyber Targets: Satellites and Communication
Next-Gen Cyber Targets: Satellites and CommunicationKrishnamurthy Rajesh on Cyber, Physical Security for Growing Number of SatellitesAs the world looks into adapting 5G and studying 6G, satellite...
Palo Alto’s BJ Jenkins on Changing Cloud Needs for Customers
Palo Alto's BJ Jenkins on Changing Cloud Needs for CustomersCompanies have transitioned since COVID-19 began from lifting and shifting their existing apps to the cloud to...
Palo Alto Founder Nir Zuk on Making the SOC More Autonomous
Palo Alto Founder Nir Zuk on Making the SOC More AutonomousBusinesses should capitalize on AI, ML and robotic process automation to address every event rather than...
Planning for Prolonged Regional Medical Device Outages
Planning for Prolonged Regional Medical Device OutagesA ransomware attack knocking out a medical center's imaging and lab equipment is an incident felt by an entire network...