Analysts Rate Tesla Mediocre Car Not Even Worth $20 Stock: “too unreliable for widespread use”A car collector is angry the Tesla fraud happened to him. Soon...
Month: December 2022
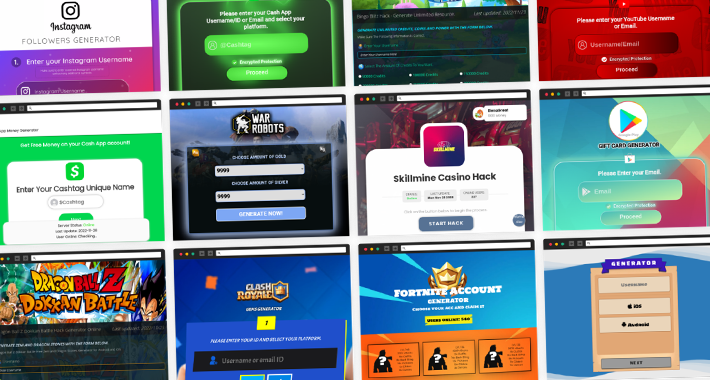
Exposing the “Data Leaks” Paradise – An Analysis
Exposing the "Data Leaks" Paradise – An Analysis In a world dominated by a countless number of malicious and fraudulent cyber threat actor adversaries including the...
Ostrich Cyber-Risk Welcomes Chip Whitmer as Vice President of Software Development
Ostrich Cyber-Risk Welcomes Chip Whitmer as Vice President of Software Development Ostrich Cyber-Risk Appoints Chip Whitmer as Vice President of Software Development. Former VP of Platform Architecture at...
API Vulnerabilities Discovered in LEGO Marketplace
API Vulnerabilities Discovered in LEGO MarketplaceThe vulnerabilities, which are now fixed, could have put sensitive customer data at riskLeer másThe vulnerabilities, which are now fixed, could...
Glupteba botnet is back after Google disrupted it in December 2021
Glupteba botnet is back after Google disrupted it in December 2021The Glupteba botnet is back, researchers reported a surge in infection worldwide after Google disrupted its...
NIST to Scrap SHA-1 Algorithm by 2030
NIST to Scrap SHA-1 Algorithm by 2030The agency said it will stop using SHA-1 in its last remaining specified protocols by December 31 2030Leer másThe agency...
FBI Charges 6, Seizes 48 Domains Linked to DDoS-for-Hire Service Platforms
FBI Charges 6, Seizes 48 Domains Linked to DDoS-for-Hire Service PlatformsThe U.S. Department of Justice (DoJ) on Wednesday announced the seizure of 48 domains that offered...
Three Steps Towards a More Secure OT Infrastructure
Three Steps Towards a More Secure OT InfrastructureBy Jason Weber, Vice President of Product, Veracity Industrial Networks Years ago, the biggest concern from the plant […]...
Threat Actors Target Ukraine’s DELTA Military System with Info-Stealing Malware
Threat Actors Target Ukraine’s DELTA Military System with Info-Stealing MalwareHackers used an email account belonging to the Ukrainian Ministry of Defense for launching a phishing campaign...
US Gov warns of BEC attacks to hijack shipments of food products
US Gov warns of BEC attacks to hijack shipments of food productsUS government is warning of business email compromise (BEC) attacks aimed at hijacking shipments of...
Mobile App Users at Risk as API Keys of Email Marketing Services Exposed
Mobile App Users at Risk as API Keys of Email Marketing Services ExposedLeaked API keys allow threat actors to perform a variety of unauthorized actionsLeer másLeaked...
Experts spotted a variant of the Agenda Ransomware written in Rust
Experts spotted a variant of the Agenda Ransomware written in RustResearchers spotted a new variant of the Agenda ransomware which is written in the cross-platform programming...
Meta Takes Down Over 200 Covert Influence Operations Since 2017
Meta Takes Down Over 200 Covert Influence Operations Since 2017The most common location for influence operations was Russia, according to MetaLeer másThe most common location for...
Ransomware Groups to Increase Zero-Day Exploit-Based Access Methods in the Future
Ransomware Groups to Increase Zero-Day Exploit-Based Access Methods in the FutureTrend Micro’s latest research paper analyzed ways in which ransomware groups could evolve to stay on...
Old vulnerabilities in Cisco products actively exploited in the wild
Old vulnerabilities in Cisco products actively exploited in the wildIT giant Cisco is warning of threat actors exploiting many old vulnerabilities in attacks in the wild....
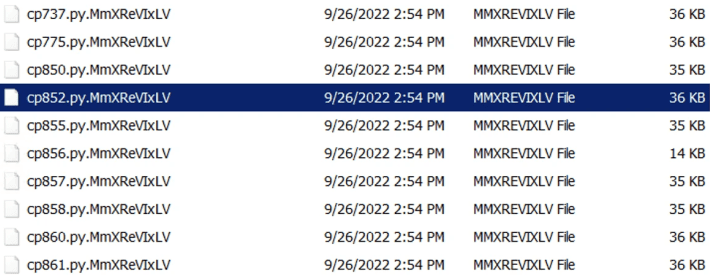
Hackers Bombard Open Source Repositories with Over 144,000 Malicious Packages
Hackers Bombard Open Source Repositories with Over 144,000 Malicious PackagesNuGet, PyPi, and npm ecosystems are the target of a new campaign that has resulted in over...
Ukraine’s Delta Military Intel System Hit by Attacks
Ukraine's Delta Military Intel System Hit by AttacksPhishing campaign spotted by CERT-UALeer másPhishing campaign spotted by CERT-UA
Top 5 Web App Vulnerabilities and How to Find Them
Top 5 Web App Vulnerabilities and How to Find ThemWeb applications, often in the form of Software as a Service (SaaS), are now the cornerstone for...
Fortnite Dev to Pay $520m in Record-Breaking Settlement
Fortnite Dev to Pay $520m in Record-Breaking SettlementFTC reveals gaming firm's privacy violations and design tricksLeer másFTC reveals gaming firm's privacy violations and design tricks
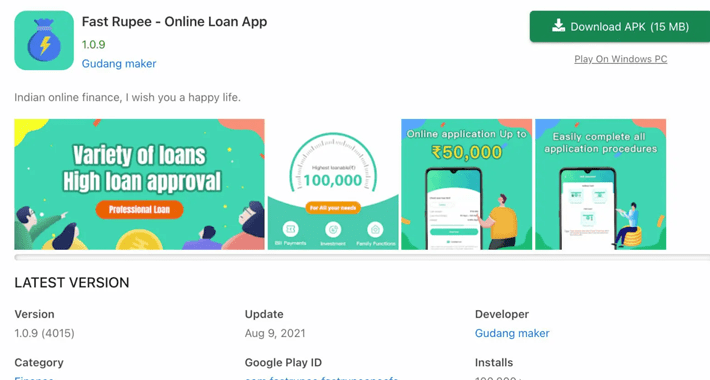
Android Malware Campaign Leverages Money-Lending Apps to Blackmail Victims
Android Malware Campaign Leverages Money-Lending Apps to Blackmail VictimsA previously undocumented Android malware campaign has been observed leveraging money-lending apps to blackmail victims into paying up...
UK Privacy Regulator Names and Shames Breached Firms
UK Privacy Regulator Names and Shames Breached FirmsICO publishes detailed list of complaints and investigationsLeer másICO publishes detailed list of complaints and investigations
Specific IoT and OT security predictions for North America for 2023
Specific IoT and OT security predictions for North America for 2023The year 2023 will see a significant shift in the way cyberattacks are engineered and that...
How to enable event collection in Windows Server
How to enable event collection in Windows ServerEvent logs register information about software and hardware events that occur in a system, and they are a key...
DoD supply chain lessons learned
DoD supply chain lessons learned A July 2022 survey of 300 U.S. Department of Defense (DoD) IT contractors shows a woeful lack of information security in...
OneCoin scammer Sebastian Greenwood pleads guilty, “Cryptoqueen” still missing
OneCoin scammer Sebastian Greenwood pleads guilty, “Cryptoqueen” still missingThe Cryptoqueen herself is still missing, but her co-conspirator, who is said to have pocketed over $20m a...
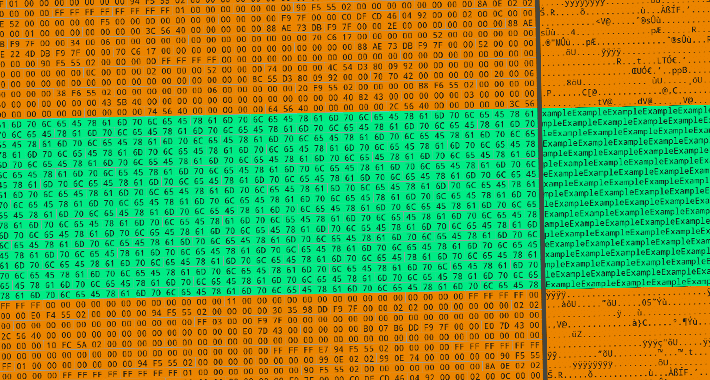
Cybersecurity Experts Uncover Inner Workings of Destructive Azov Ransomware
Cybersecurity Experts Uncover Inner Workings of Destructive Azov RansomwareCybersecurity researchers have published the inner workings of a new wiper called Azov Ransomware that's deliberately designed to corrupt data...
Serious Attacks Could Have Been Staged Through This Amazon ECR Public Gallery Vulnerability
Serious Attacks Could Have Been Staged Through This Amazon ECR Public Gallery VulnerabilityA critical security flaw has been disclosed in Amazon Elastic Container Registry (ECR) Public...
Cisco Firepower Management Center and Firepower Threat Defense Software SSH Denial of Service Vulnerability
Cisco Firepower Management Center and Firepower Threat Defense Software SSH Denial of Service VulnerabilityA vulnerability in the processing of SSH connections of Cisco Firepower Management Center...
Cisco Firepower Management Center and Firepower Threat Defense Software SSH Denial of Service Vulnerability
Cisco Firepower Management Center and Firepower Threat Defense Software SSH Denial of Service VulnerabilityA vulnerability in the processing of SSH connections of Cisco Firepower Management Center...
Google Launches OSV-Scanner Tool to Identify Open Source Vulnerabilities
Google Launches OSV-Scanner Tool to Identify Open Source VulnerabilitiesGoogle on Tuesday announced the open source availability of OSV-Scanner, a scanner that aims to offer easy access to...