Password manager LastPass reveals intrusion into development systemLastPass, maker of a popular password management application, revealed Thursday that an unauthorized party gained access to its development...
Day: September 8, 2022
Sorting zero-trust hype from reality
Sorting zero-trust hype from realityIt seems as if everyone is playing “buzzword bingo” when it comes to zero trust and its implementation, and it starts with...
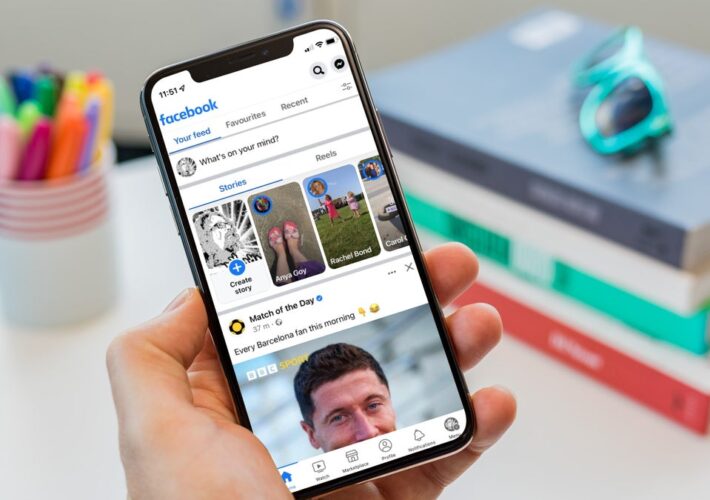
Facebook agrees to settle class action lawsuit related to Cambridge Analytica data breach
Facebook agrees to settle class action lawsuit related to Cambridge Analytica data breachFacebook parent Meta Platforms agreed Friday to settle a class action lawsuit seeking damages...
Key takeaways from the Open Cybersecurity Schema Format
Key takeaways from the Open Cybersecurity Schema FormatOne of the most pervasive challenges in the current cybersecurity environment is an overabundance of tooling vendors, all of...
Multi-stage crypto-mining malware hides in legitimate apps with month-long delay trigger
Multi-stage crypto-mining malware hides in legitimate apps with month-long delay triggerResearchers have discovered a new multi-stage malware delivery campaign that relies on legitimate application installers distributed...
Nvidia partners with Dell and VMware for faster AI systems
Nvidia partners with Dell and VMware for faster AI systemsNew vSphere paired with Nvidia DPUs will speed up data center performance.Leer másCSO OnlineNew vSphere paired with...
Traceable AI debuts API testing product for its security platform
Traceable AI debuts API testing product for its security platformTraceable AI today announced the general availability of xAST, an API security testing solution, as part of...
Stuxnet explained: The first known cyberweapon
Stuxnet explained: The first known cyberweaponWhat is Stuxnet? Stuxnet is a powerful computer worm designed by U.S. and Israeli intelligence that to disable a key part...
Resolving conflicts between security best practices and compliance mandates
Resolving conflicts between security best practices and compliance mandatesSo, you read a great tip on the internet and think it would improve your security posture. Before...
Women in cybersecurity form non-profit organization The Forte Group
Women in cybersecurity form non-profit organization The Forte GroupA group of over 90 women working in cybersecurity roles have formed The Forte Group, a non-profit organization...
Palo Alto adds new SaaS compliance, threat prevention, URL filtering features to Prisma solution
Palo Alto adds new SaaS compliance, threat prevention, URL filtering features to Prisma solutionCybersecurity vendor Palo Alto Networks has announced new updates to its Prisma Secure...
Intro to MongoDB’s queryable encryption
Intro to MongoDB’s queryable encryptionQueryable encryption was the main attraction at MongoDB World 2022, for understandable reasons. It introduces a unique capability to reduce the attack...
Dashlane launches integrated passkey support for password manager with new in-browser passkey solution
Dashlane launches integrated passkey support for password manager with new in-browser passkey solutionPassword management vendor Dashlane has announced the introduction of integrated passkey support in its...
Remediant wants to move beyond PAM to secure enterprise networks
Remediant wants to move beyond PAM to secure enterprise networksSecurity software provider Remediant wants to move beyond basic privileged access management (PAM) to help CSOs secure...
Ragnar Locker continues trend of ransomware targeting energy sector
Ragnar Locker continues trend of ransomware targeting energy sectorThe recent attack on Greece’s largest natural gas transmission operator DESFA by ransomware gang Ragnar Locker is the...
Apple pushes out emergency updates to address zero-day exploits
Apple pushes out emergency updates to address zero-day exploitsApple has encouraged users of older mobile and desktop devices to update their software ASAP, as a vulnerability...
OpenSSF releases npm best practices to help developers tackle open-source dependency risks
OpenSSF releases npm best practices to help developers tackle open-source dependency risksThe Open Source Security Foundation (OpenSSF) has released the npm Best Practices Guide to help...
Top 12 managed detection and response solutions
Top 12 managed detection and response solutionsOf all foundational elements for information security, logging requires far more care and feeding than its fellow cornerstones such as...
How Azure Active Directory opens new authentication risks
How Azure Active Directory opens new authentication risksIt's been common knowledge for years that local Windows Active Directory networks are vulnerable to NTLM relay and pass-the-hash...
Nelnet breach affects 2.5M student loan accounts; Google releases emergency Chrome security update
Nelnet breach affects 2.5M student loan accounts; Google releases emergency Chrome security updateThe new school year is underway. It’s a good time to remember that adults...
Samsung reports second data breach in 6 months
Samsung reports second data breach in 6 monthsSamsung has opened up about a data breach it detected on or around August 4, affecting the personal information...
The Heartbleed bug: How a flaw in OpenSSL caused a security crisis
The Heartbleed bug: How a flaw in OpenSSL caused a security crisisWhat is Heartbleed? Heartbleed is a vulnerability in OpenSSL that came to light in April...
10 Best IT Compliance Conferences in 2022
10 Best IT Compliance Conferences in 2022 Networking, insights, news, and more! IT compliance conferences are integral to your cybersecurity efforts, ensuring that your team is...
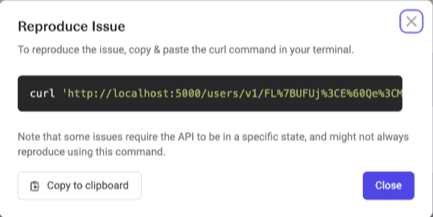
What is Mayhem for API?
What is Mayhem for API?Mayhem for API automates testing REST APIs by bringing the full might of fuzzing methodology to API testing. With the guidance of...
In-app browser security risks, and what to do about them
In-app browser security risks, and what to do about them In-app browsers can pose significant security risks to businesses, with their tendency to track data a...
Is your phone Safe For Scrollers (SFS)?
Is your phone Safe For Scrollers (SFS)? Shan Boodram — certified sexologist, intimacy educator, podcast host, and all around sex education star — knows a thing...
BSides Vancouver 2022 – Darren Thurston’s And Jenn Lemmen’s ‘Our Experiences Finding Missing People With TraceLabs OSINT CTF’
BSides Vancouver 2022 – Darren Thurston’s And Jenn Lemmen’s ‘Our Experiences Finding Missing People With TraceLabs OSINT CTF’Our sincere thanks to BSides Vancouver for publishing their...
TikTok denies breach after hackers claim billions of user records stolen
TikTok denies breach after hackers claim billions of user records stolenTikTok is denying claims that a hacking group has breached an Alibaba cloud database containing 2.05...
Cisco Releases Security Patches for New Vulnerabilities Impacting Multiple Products
Cisco Releases Security Patches for New Vulnerabilities Impacting Multiple ProductsCisco on Wednesday rolled out patches to address three security flaws affecting its products, including a high-severity weakness disclosed...
Shopify Fails to Prevent Known Breached Passwords
Shopify Fails to Prevent Known Breached PasswordsA recent report revealed that ecommerce provider, Shopify uses particularly weak password policies on the customer-facing portion of its Website. According to...