XKCD ‘Tetherball Configurations’ via the comic artistry and dry wit of Randall Munroe, resident at XKCD! Permalink The post XKCD ‘Tetherball Configurations’ appeared first on Security...
Month: August 2022
When to Use Penetration Testing Software, Services, or Both
When to Use Penetration Testing Software, Services, or BothThe post When to Use Penetration Testing Software, Services, or Both appeared first on Digital Defense. The post...
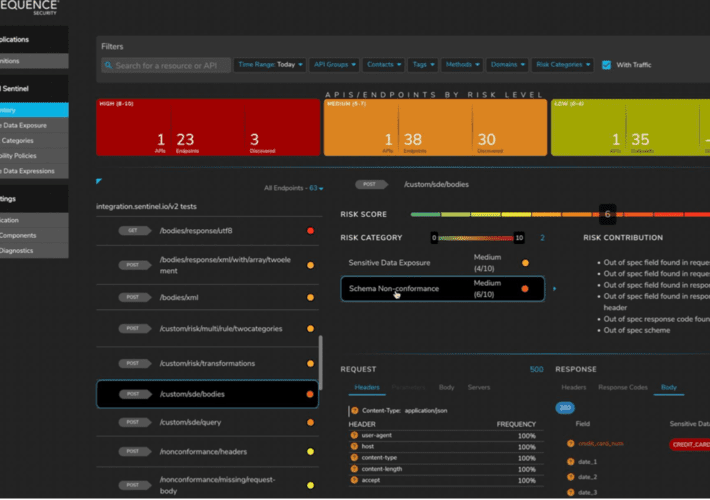
Unified API Protection for Telcos and Mobile Carriers – Time to Value
Unified API Protection for Telcos and Mobile Carriers – Time to ValueLargest Mobile Carrier Identified 4,600 APIs in Days, not Weeks, or Months The security team...
BSidesTLV 2022 – Shira Stepansky’s ‘Diamond Model Analysis Of Whatsapp Security Breach’
BSidesTLV 2022 – Shira Stepansky’s ‘Diamond Model Analysis Of Whatsapp Security Breach’Our thanks to BSidesTLV for publishing their outstanding conference videos on the organization's YouTube channel....
IAM budget in a recession
IAM budget in a recessionHow to make the most out of your 2023 IAM budget The looming recession is causing the C-suite to re-evaluate spending priorities....
LastPass Breach Raises Disclosure Transparency Concerns
LastPass Breach Raises Disclosure Transparency Concerns In the graphic novel “The Watchman” by Alan Moore and Dave Gibbons, one of the recurring themes is ‘Who watches...
The inevitable pivot to BYOA (Bring Your Own Application): Mitigating risk to enable innovation
The inevitable pivot to BYOA (Bring Your Own Application): Mitigating risk to enable innovationSecurity teams should view BYOA as an opportunity in efficiency and innovation The...
Critical Vulnerability Discovered in Atlassian Bitbucket Server and Data Center
Critical Vulnerability Discovered in Atlassian Bitbucket Server and Data CenterAtlassian has rolled out fixes for a critical security flaw in Bitbucket Server and Data Center that could lead...
Iranian Hackers Exploiting Unpatched Log4j 2 Bugs to Target Israeli Organizations
Iranian Hackers Exploiting Unpatched Log4j 2 Bugs to Target Israeli OrganizationsIranian state-sponsored actors are leaving no stone unturned to exploit unpatched systems running Log4j to target...
Security and Cheap Complexity
Security and Cheap ComplexityI’ve been saying that complexity is the worst enemy of security for a long time now. (Here’s me in 1999.) And it’s been...
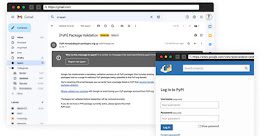
PyPI Repository Warns Python Project Maintainers About Ongoing Phishing Attacks
PyPI Repository Warns Python Project Maintainers About Ongoing Phishing AttacksThe Python Package Index, PyPI, on Wednesday sounded the alarm about an ongoing phishing campaign that aims...
U.S. Government Spending Billions on Cybersecurity
U.S. Government Spending Billions on CybersecurityIn recent months, the House of Representatives has been hard at work drafting various spending bills for the 2023 fiscal year....
Researchers Uncover Kimusky Infra Targeting South Korean Politicians and Diplomats
Researchers Uncover Kimusky Infra Targeting South Korean Politicians and DiplomatsThe North Korean nation-state group Kimusky has been linked to a new set of malicious activities directed...
Cybercrime Groups Increasingly Adopting Sliver Command-and-Control Framework
Cybercrime Groups Increasingly Adopting Sliver Command-and-Control FrameworkNation-state threat actors are increasingly adopting and integrating the Sliver command-and-control (C2) framework in their intrusion campaigns as a replacement for Cobalt...
Okta Hackers Behind Twilio and Cloudflare Breach Hit Over 130 Organizations
Okta Hackers Behind Twilio and Cloudflare Breach Hit Over 130 OrganizationsThe threat actor behind the attacks on Twilio and Cloudflare earlier this month has been linked to a broader phishing...
Microsoft Uncovers New Post-Compromise Malware Used by Nobelium Hackers
Microsoft Uncovers New Post-Compromise Malware Used by Nobelium HackersThe threat actor behind the SolarWinds supply chain attack has been linked to yet another "highly targeted" post-exploitation...
Hackers Breach LastPass Developer System to Steal Source Code
Hackers Breach LastPass Developer System to Steal Source CodePassword management service LastPass confirmed a security incident that resulted in the theft of certain source code and...
Cybersecurity Insights with Contrast CISO David Lindner | 8/26
Cybersecurity Insights with Contrast CISO David Lindner | 8/26 Insight #1 " If you are struggling with the adoption of MFA across your organization, it’s time...
What I wish I knew about security when I started programming
What I wish I knew about security when I started programming It’s critical for developers to understand basic security concepts and best practices to build secure...
Insurers May Not Cover ‘State-Sponsored’ Cyberattacks
Insurers May Not Cover ‘State-Sponsored’ Cyberattacks Many of the more expensive cyberattacks and ransomware attacks, including the Solar Winds and Colonial Pipeline attacks, have been attributed...
Confidential Computing Beats Homomorphic Encryption for Data Security
Confidential Computing Beats Homomorphic Encryption for Data Security For the enterprise, data is like the air we breathe. At the same time, data seems to be...
Cybersecurity News Round-Up: Week of August 22, 2022
Cybersecurity News Round-Up: Week of August 22, 2022Twitter's Ex-CSO accuses the company of cybersecurity negligence, Hackers continue to attack hospitals and critical infrastructure The post Cybersecurity...
S3 Ep97: Did your iPhone get pwned? How would you know? [Audio + Text]
S3 Ep97: Did your iPhone get pwned? How would you know? [Audio + Text]Latest episode - listen now! (Or read the transcript if you prefer the...
Firefox 104 is out – no critical bugs, but update anyway
Firefox 104 is out – no critical bugs, but update anywayTwo trust-spoofing bugs were the main culprits this month - but neither one was a zero-day.Leer...
LastPass attackers steal source code, no evidence users’ passwords compromised
LastPass attackers steal source code, no evidence users’ passwords compromisedLastPass, the popular password manager used by millions of people around the world, has announced that it...
The 4 Best Open Source PKI Software Solutions (And Choosing the Right One)
The 4 Best Open Source PKI Software Solutions (And Choosing the Right One)In the never-ending battle between business success and cybersecurity threats, enterprises have discovered a...
TSA Requirements: A Snapshot of Growing Attention to Pipeline Cybersecurity
TSA Requirements: A Snapshot of Growing Attention to Pipeline CybersecurityThe post TSA Requirements: A Snapshot of Growing Attention to Pipeline Cybersecurity appeared first on Nozomi Networks....
What Is a TLS/SSL Port?
What Is a TLS/SSL Port?What Is a TLS/SSL Port? 97thfloor Fri, 08/26/2022 - 09:15 1 view What TCP Ports Are Used Most Frequently? Managing TLS/SSL...
DNS data indicates increased malicious domain activity, phishing toolkit reuse
DNS data indicates increased malicious domain activity, phishing toolkit reuseNew research from cybersecurity vendor Akamai has revealed that 12.3% of monitored devices communicated with domains associated...
Up to 35% more CVEs published so far this year compared to 2021
Up to 35% more CVEs published so far this year compared to 2021A new report from Trustwave SpiderLabs has revealed that the number of CVEs published...