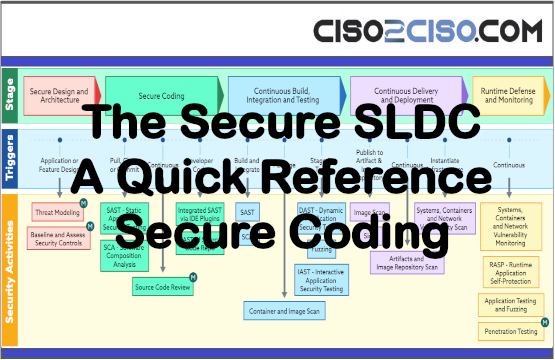
Secure Coding
- Static Application Security Testing (SAST)
o SAST, also referred to as Static Code Analysis, does not require a compiled application to run – so it can, and should, be run early in the SDLC. The test reveals vulnerabilities in the code, specifically those in the OWASP Top 10 like SQL injection.
- Software Composition Analysis (SCA)
o A software composition analysis scans software, as well as its dependencies, and displays a list of known vulnerabilities as well as licenses and noting any deprecated dependencies.
- Secure Code Review
o “A secure code review is a specialized task involving manual and/or automated review of an application’s source code in an attempt to identify security-related weaknesses (flaws) in the
code. It does not attempt to identify every issue in the code, but instead looks to provide insight into what types of security-related problems exist and help the application developer understand what classes of issues are present.” (Mitre).
Continuous Build, Integration, and Testing
- Container and Image Scan
o Checks the build process of your containers and images for vulnerabilities. This should be done to establish trust with the base image or container, as well as any composites.
- Dynamic Application Security Testing (DAST)
o DAST is for compiled code / a running application without knowledge of the environment, simulating a hacker. Since the code is running for the test, this test is good for identifying issues with the runtime environment as well. Note that DASTs are only run on web applications and services.
- Fuzzing
o Testing with unexpected inputs. This can be something like testing if a non-date is entered in a date field, or even (trying to) drop a binary file in a text field. The goal is to capture these cases and ensure that the application does not crash and gives a usable error message.
- Interactive Application Security Testing (IAST)
o An IAST tests the running application for vulnerabilities during use, similar to a DAST. Unlike a DAST, an IAST can identify the line of code that is the source of a particular vulnerability.
Views: 0