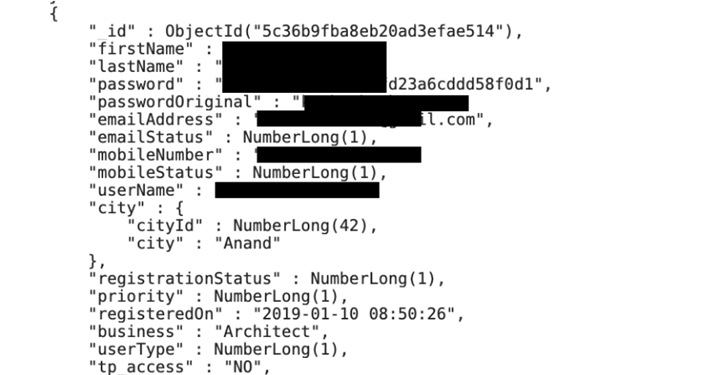
Source: securityaffairs.com - Author: Pierluigi Paganini MyEstatePoint Property Search Android app leaks user passwords The MyEstatePoint...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
SecurityAffairs.com
Source: securityaffairs.com - Author: Pierluigi Paganini The source code of Zeppelin Ransomware sold on a hacking...
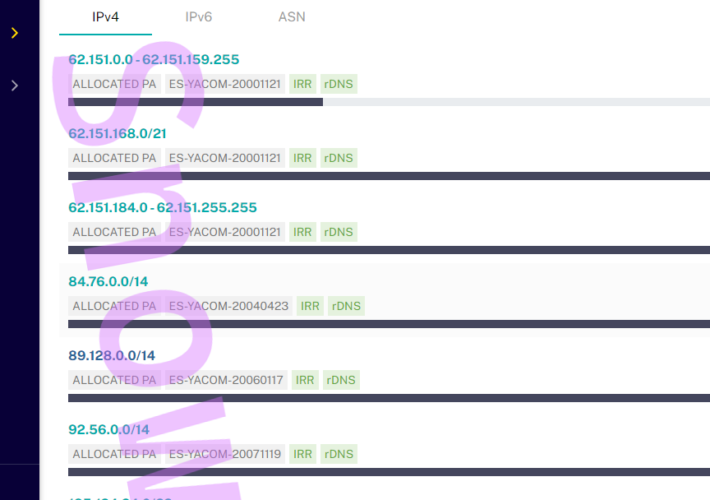
Source: securityaffairs.com - Author: Pierluigi Paganini Hacker hijacked Orange Spain RIPE account causing internet outage to...
Source: securityaffairs.com - Author: Pierluigi Paganini HealthEC data breach impacted more than 4.5 Million people Healthcare...
Source: securityaffairs.com - Author: Pierluigi Paganini Experts found 3 malicious packages hiding crypto miners in PyPi...
Source: securityaffairs.com - Author: Pierluigi Paganini Crooks hacked Mandiant X account to push cryptocurrency scam The...
Source: securityaffairs.com - Author: Pierluigi Paganini Cybercriminals Implemented Artificial Intelligence (AI) for Invoice Fraud Crooks created...
Source: securityaffairs.com - Author: Pierluigi Paganini CISA ADDS CHROME AND PERL LIBRARY FLAWS TO ITS KNOWN...
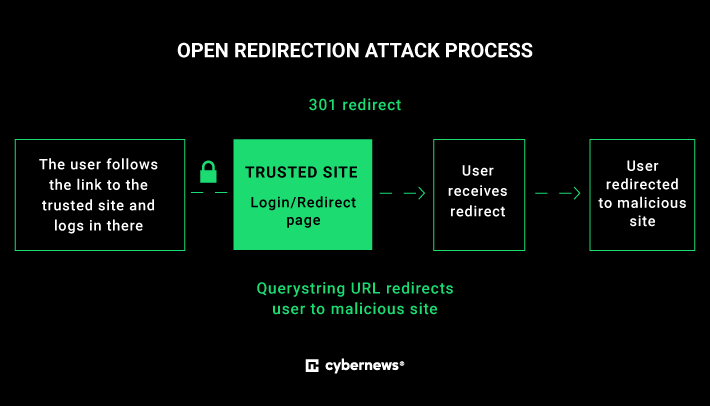
Source: securityaffairs.com - Author: Pierluigi Paganini Don’t trust links with known domains: BMW affected by redirect...
Source: securityaffairs.com - Author: Pierluigi Paganini Hackers stole more than $81 million worth of crypto assets...
Source: securityaffairs.com - Author: Pierluigi Paganini Ukraine’s SBU said that Russia’s intelligence hacked surveillance cameras to...
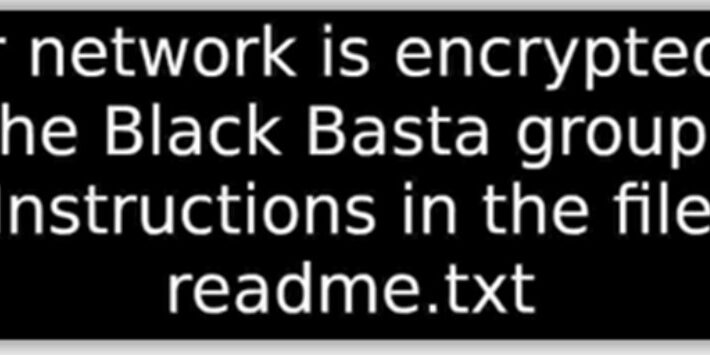
Source: securityaffairs.com - Author: Pierluigi Paganini Researchers released a free decryptor for Black Basta ransomware A...
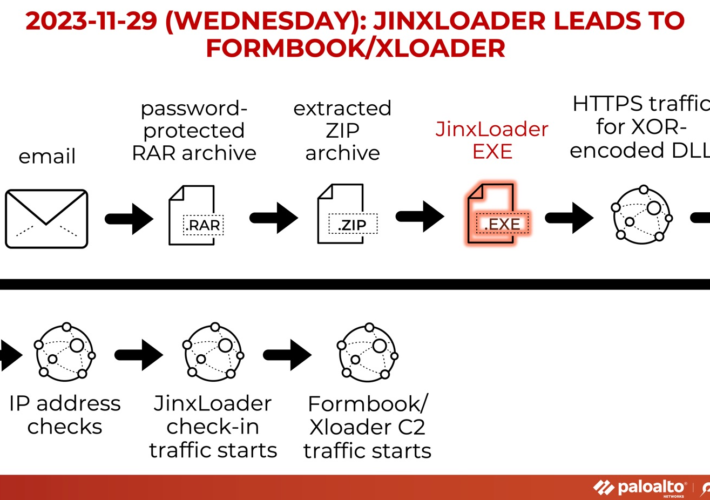
Source: securityaffairs.com - Author: Pierluigi Paganini Experts warn of JinxLoader loader used to spread Formbook and...
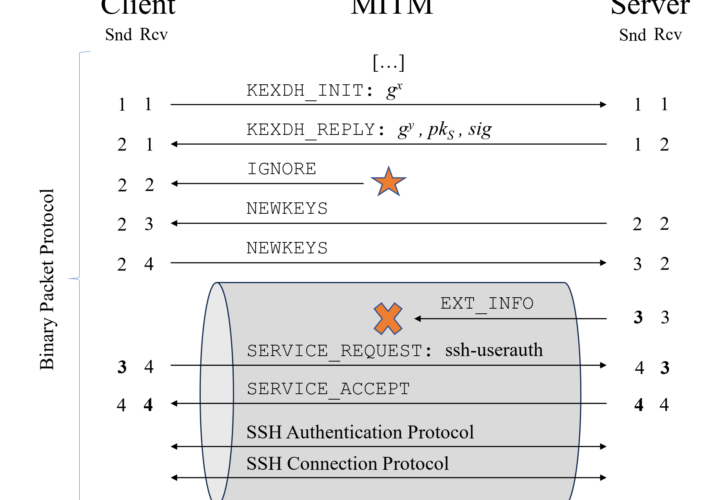
Source: securityaffairs.com - Author: Pierluigi Paganini Terrapin attack allows to downgrade SSH protocol security Researchers discovered...
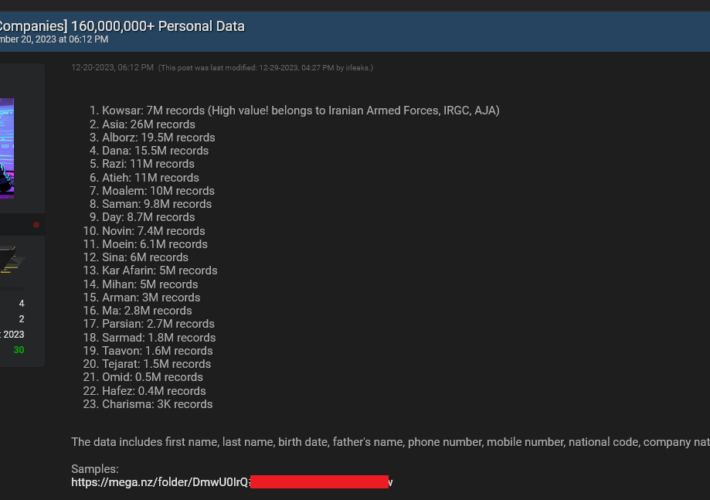
Source: securityaffairs.com - Author: Pierluigi Paganini Multiple organizations in Iran were breached by a mysterious hacker...
Source: securityaffairs.com - Author: Pierluigi Paganini Top 2023 Security Affairs cybersecurity stories These are the Top...
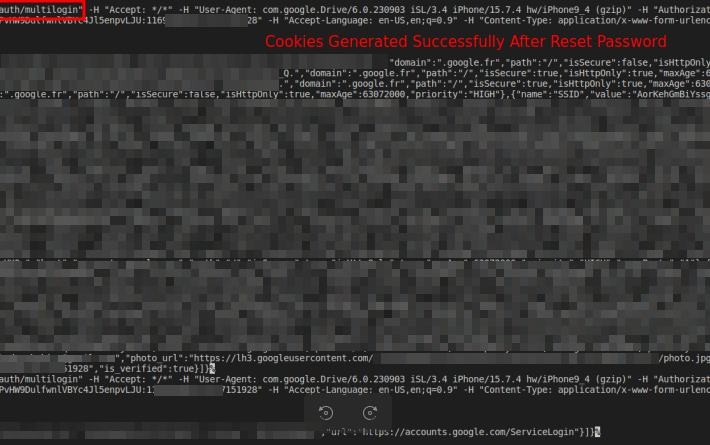
Source: securityaffairs.com - Author: Pierluigi Paganini Malware exploits undocumented Google OAuth endpoint to regenerate Google cookies...
Source: securityaffairs.com - Author: Pierluigi Paganini Cactus RANSOMWARE gang hit the Swedish retail and grocery provider...
Source: securityaffairs.com - Author: Pierluigi Paganini Google agreed to settle a $5 billion privacy lawsuit Pierluigi...
Source: securityaffairs.com - Author: Pierluigi Paganini Security Affairs newsletter Round 452 by Pierluigi Paganini – INTERNATIONAL...
Source: securityaffairs.com - Author: Pierluigi Paganini INC RANSOM ransomware gang claims to have breached Xerox Corp...
Source: securityaffairs.com - Author: Pierluigi Paganini Spotify music converter TuneFab puts users at risk Pierluigi Paganini...
Source: securityaffairs.com - Author: Pierluigi Paganini Cyber attacks hit the Assembly of the Republic of Albania...
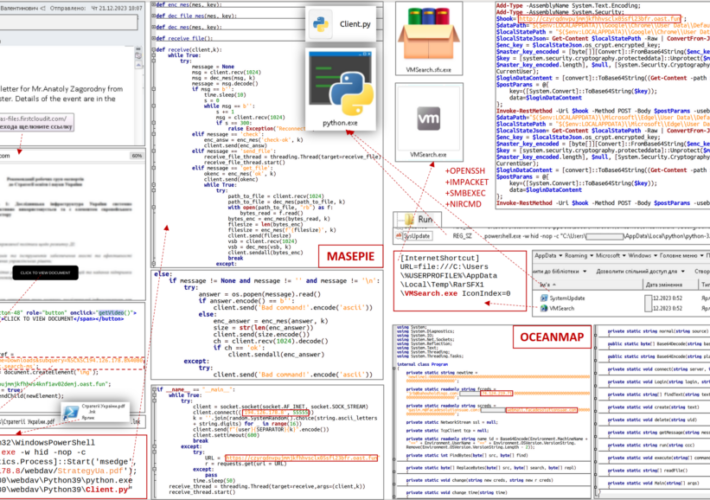
Source: securityaffairs.com - Author: Pierluigi Paganini Russia-linked APT28 used new malware in a recent phishing campaign...
Source: securityaffairs.com - Author: Pierluigi Paganini Clash of Clans gamers at risk while using third-party app...
Source: securityaffairs.com - Author: Pierluigi Paganini New Version of Meduza Stealer Released in Dark Web Pierluigi...
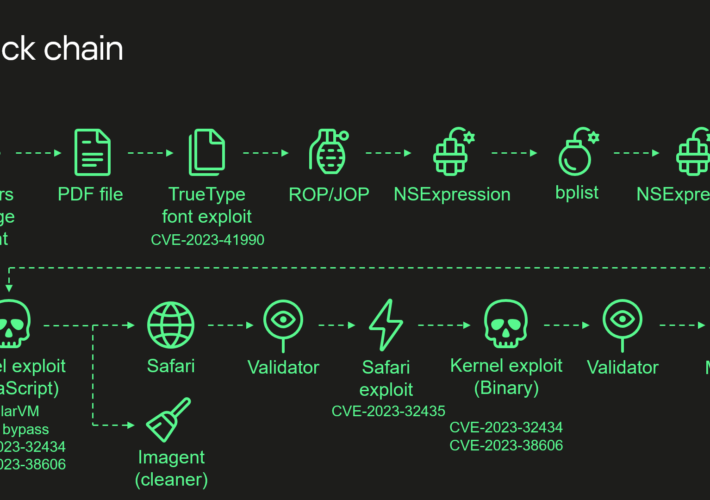
Source: securityaffairs.com - Author: Pierluigi Paganini Operation Triangulation attacks relied on an undocumented hardware feature Pierluigi...
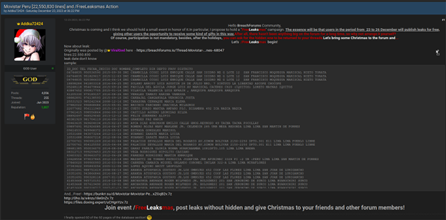
Source: securityaffairs.com - Author: Pierluigi Paganini Cybercriminals launched “Leaksmas” event in the Dark Web exposing massive...
Source: securityaffairs.com - Author: Pierluigi Paganini Lockbit ransomware attack interrupted medical emergencies gang at a German...
Source: securityaffairs.com - Author: Pierluigi Paganini Experts warn of critical Zero-Day in Apache OfBiz Pierluigi Paganini...