Source: www.techrepublic.com - Author: Lance Whitney Zero-day exploits — or 0days, in hacker-speak — allow attackers...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security TechRepublic
Source: www.techrepublic.com - Author: In general, security analysts are tasked with identifying weaknesses in current security...
Source: www.techrepublic.com - Author: Franklin Okeke on July 10, 2023, 1:51 PM EDT 6 Best VPNs...
Source: www.techrepublic.com - Author: Jack Wallen on July 10, 2023, 5:30 AM EDT How to Use...
Source: www.techrepublic.com - Author: When you think of VPNs, chances are pretty good your thoughts go...
Source: www.techrepublic.com - Author: Cedric Pernet Image: sarayut_sy/Adobe Stock In the ever-evolving landscape of cybersecurity, cloud...
Source: www.techrepublic.com - Author: Franklin Okeke Astra: Best for diverse infrastructure Acunetix: Best for pentest automation...
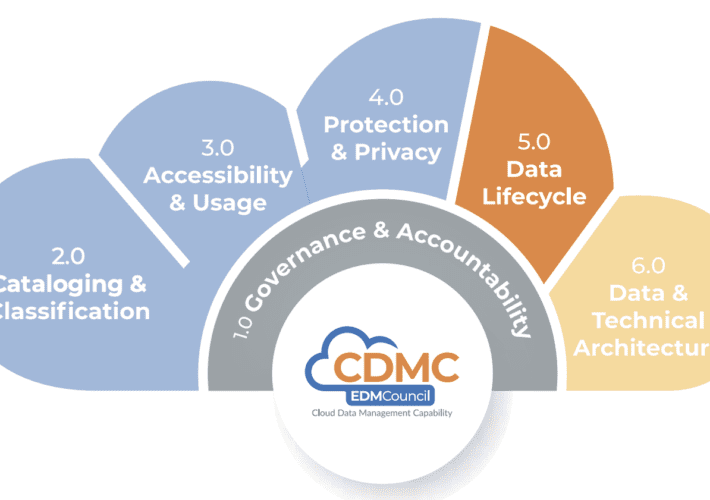
Source: www.techrepublic.com - Author: Karl Greenberg on July 7, 2023, 2:50 PM EDT EDM Council Survey:...
Source: www.techrepublic.com - Author: Mark W. Kaelin Image: Mark KaelinAll images created by Mark Kaelin from...
Source: www.techrepublic.com - Author: Megan Crouse The AI giant predicts human-like machine intelligence could arrive within...
Source: www.techrepublic.com - Author: Cedric Pernet Image: Sashkin/Adone Stock New malware dubbed Meduza Stealer can steal...
Source: www.techrepublic.com - Author: Karl Greenberg on July 5, 2023, 5:29 PM EDT Thales: For Data...
Source: www.techrepublic.com - Author: Megan Crouse Learn about the benefits and use cases of quantum computing....
Source: www.techrepublic.com - Author: This policy from TechRepublic Premium provides guidelines for the consistent and secure...
Source: www.techrepublic.com - Author: This policy from TechRepublic Premium provides guidelines to safeguard company information, reduce...
Source: www.techrepublic.com - Author: Cyberattacks continue to grow in quantity and sophistication at the same time...
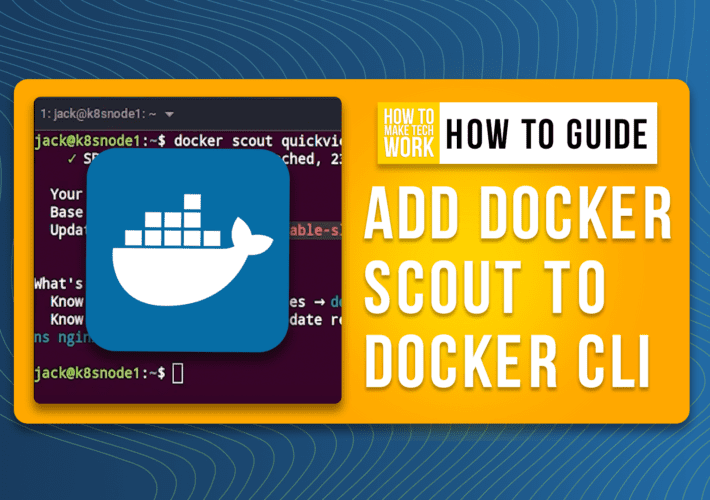
Source: www.techrepublic.com - Author: Jack Wallen on July 3, 2023, 9:38 AM EDT How to add...
Source: www.techrepublic.com - Author: This policy will help your organization safeguard its hardware, software and data...
Source: www.techrepublic.com - Author: Karl Greenberg Image: UnderhilStudio/Shutterstock Findings in network intelligence firm Gigamon’s Hybrid Cloud...
Source: www.techrepublic.com - Author: Karl Greenberg on June 30, 2023, 12:29 PM EDT Aqua Security Study...
Source: www.techrepublic.com - Author: Drew Robb Patching remains a difficult task for many organizations – but...
Source: www.techrepublic.com - Author: Ali Azhar Image: Ico Maker/Adobe Stock Cyberattacks are continuing to increase. This...
Source: www.techrepublic.com - Author: TechRepublic Academy on June 30, 2023, 5:05 AM EDT Protect Your Data...
Source: www.techrepublic.com - Author: Lance Whitney Image: IB Photography/Adobe Stock You’re creating a document in Microsoft...
Source: www.techrepublic.com - Author: Lance Whitney on June 29, 2023, 5:08 PM EDT 8Base Ransomware Attacks...
Kaspersky’s New Report Reveals the Top Cyber Threats for SMBs in 2023 – Source: www.techrepublic.com
Source: www.techrepublic.com - Author: Cedric Pernet A new report from Kaspersky reveals the top cyber threats...
Source: www.techrepublic.com - Author: Ray Fernandez If you're not sure how to view your SSH certificates,...
Source: www.techrepublic.com - Author: Security measures and other IT controls only work if they are implemented...
Source: www.techrepublic.com - Author: Drew Robb Syxsense now offers more IT and endpoint management functions, including...
Source: www.techrepublic.com - Author: Karl Greenberg Image: tete_escape/Adobe Stock When the FIDO Alliance (Fast Identity Online)...