Source: securityboulevard.com - Author: Paul Asadoorian One time while attending a conference and getting ready to...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: Joe Breen Shining light on cyber risk management program disclosure requirements We’ve...
Source: securityboulevard.com - Author: Mor Avni, Product Manager, Scytale For SaaS companies, it’s hard not to...
Source: securityboulevard.com - Author: Michelle Ofir Geveye “AI is too important not to regulate—and too important...
Source: securityboulevard.com - Author: Nicholas Tan A recent successful cyberattack on a large technology provider for...
Source: securityboulevard.com - Author: Nicholas Tan A pioneer of LogRhythm’s Asia Pacific operations, Joanne Wong’s appointment...
Source: securityboulevard.com - Author: Erin Crapser Wright Joins TrustCloud as the company expands solutions for customers,...
Source: securityboulevard.com - Author: Ron Arden Organizations use and store many types of data. Some of...
Source: securityboulevard.com - Author: Michael Vizard Entro has added a life cycle management capability to its...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: Matthew Rosenquist It was bound to happen — researchers have created a 1st generation...
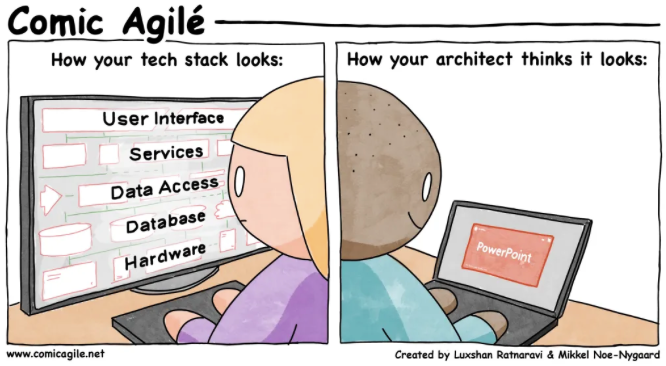
Source: securityboulevard.com - Author: Marc Handelman via the inimitable Daniel Stori at Turnoff.US. Permalink *** This...
Source: securityboulevard.com - Author: Jeffrey Burt Phobos, a complex ransomware-as-a-service (RaaS) operation that has been around...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: Allan Lyons, Julien Gamba, Austin Shawaga, Joel Reardon, Juan...
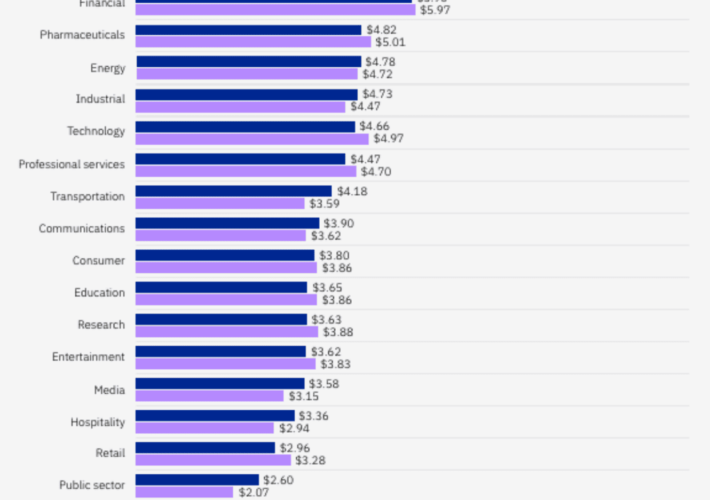
Source: securityboulevard.com - Author: Votiro Financial Giants Under Siege It’s only the first quarter of 2024...
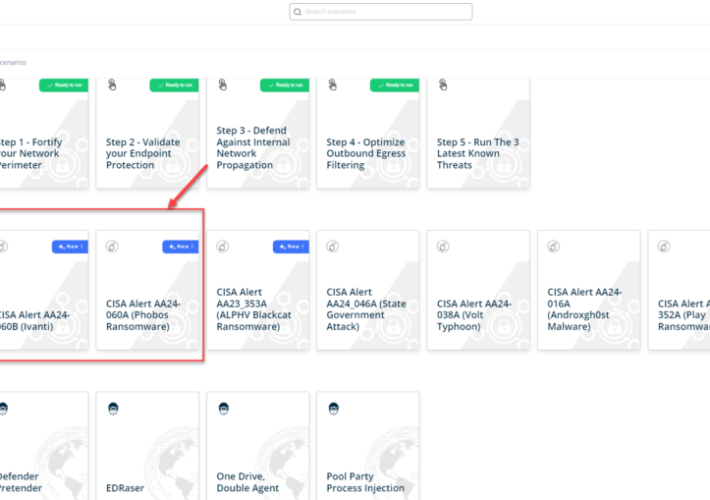
Source: securityboulevard.com - Author: Kaustubh Jagtap Author: Kaustubh Jagtap, Product Marketing Director, SafeBreach On February 29th,...
Source: securityboulevard.com - Author: Francis Guibernau On February 29, 2024, the Cybersecurity and Infrastructure Security Agency...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: Jeffrey Burt The federal government and cybersecurity teams are warning organizations that...
Source: securityboulevard.com - Author: Marc Handelman Hot Topics USENIX Security ’23 - Vivek Nair, Dawn Song...
Source: securityboulevard.com - Author: Alexandra Charikova The uncontrolled sprawl of exposed, insecure APIs puts sensitive personal...
Source: securityboulevard.com - Author: Richi Jennings Amazon, Sears and Shein still sell security swerving stuff.Cheap Chinese doorbell...
Source: securityboulevard.com - Author: Alexandra Charikova API Sprawl is a serious challenge in 2024, and shadow...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: Harman Singh In the digital landscape, what you don’t know can hurt...
Source: securityboulevard.com - Author: Marc Handelman Wednesday, February 28, 2024 Security Boulevard The Home of the...
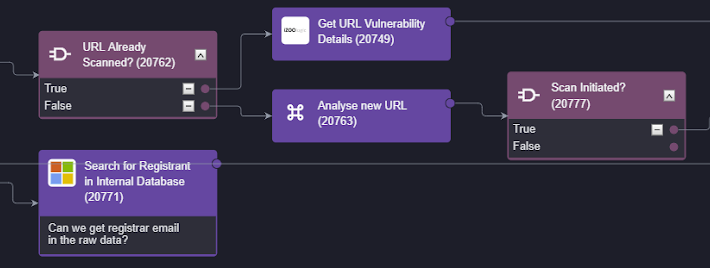
Source: securityboulevard.com - Author: Pierre Noujeim The collaboration between Smart SOAR (Security Orchestration, Automation, and Response)...
Source: securityboulevard.com - Author: brianrobertson Part I: The Good and the Bad of AI Few would...
Source: securityboulevard.com - Author: Richi Jennings Fancy Bear still hacking ubiquitous gear, despite patch availability.Ubiquiti’s EdgeRouter ships...