Source: securityboulevard.com - Author: The Constella Team Most security protocols look outward when looking for cybersecurity...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: Alexander Krause, Jan H. Klemmer, Nicolas Huaman, Dominik Wermke,...
Source: securityboulevard.com - Author: Pierre Noujeim Integrating a variety of cybersecurity tools and platforms is often...
Source: securityboulevard.com - Author: Wajahat Raja A highly sensitive flaw has been identified in the LiteSpeed...
Source: securityboulevard.com - Author: Michael Vizard Edgeless Systems today launched a Continuum platform that applies confidential...
Source: securityboulevard.com - Author: Jeffrey Burt The U.S. Department of Health and Human Services (HHS) is...
Source: securityboulevard.com - Author: Ainsley Lawrence Protecting your business from scams and cybersecurity threats not only...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: Jacob Hughes ATARC’s Future of Secure Work Working Group, of which Privoro’s...
Source: securityboulevard.com - Author: Team Nuspire Microsoft’s Patch Tuesday for March 2024 has once again highlighted...
Source: securityboulevard.com - Author: Marc Handelman via the comic artistry and dry wit of Randall Munroe,...
Source: securityboulevard.com - Author: Richi Jennings Last year, $GOOG paid $10 million to ethical hackers for...
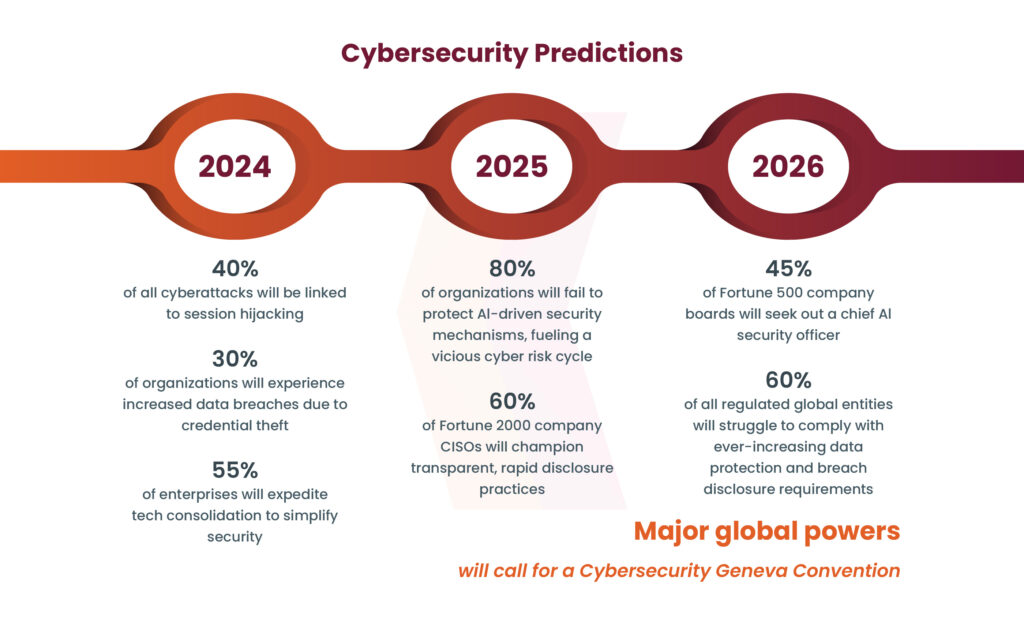
Source: securityboulevard.com - Author: Shikha Dhingra The swift advancement of generative AI systems like OpenAI’s ChatGPT...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: Jonas Hielscher. Uta Menges, Simon Parkin, Annette Kluge, M....
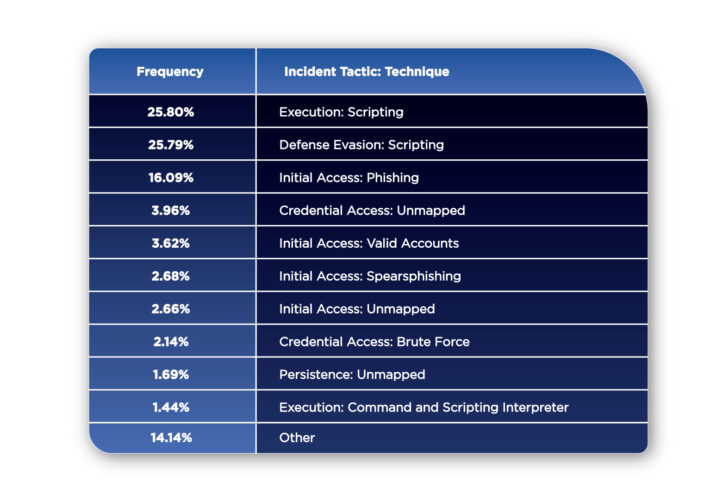
Source: securityboulevard.com - Author: NSFOCUS The year 2023 witnessed a dynamic and complex cybersecurity landscape, with...
Source: securityboulevard.com - Author: Jaweed Metz Government bodies are clamping down heavily on institutions and organizations...
Source: securityboulevard.com - Author: cyberwire San Francisco, Calif., Mar. 7, 2024 — Badge Inc., the award-winning privacy...
Source: securityboulevard.com - Author: Cofense Malicious email threats bypassing all secure email gateways (SEGs) on the...
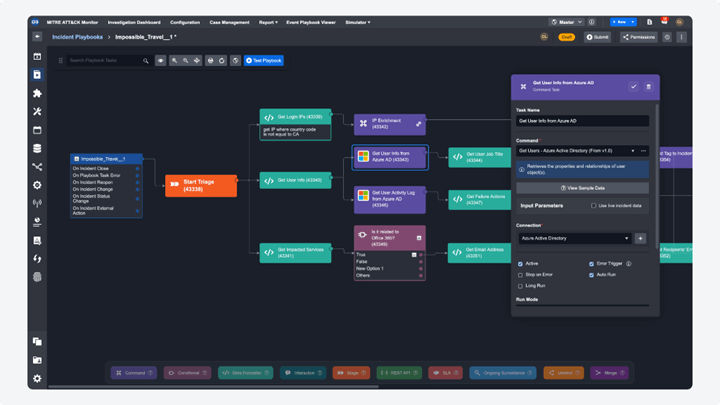
Source: securityboulevard.com - Author: Pierre Noujeim SOAR solutions create a centralized queue of all incidents going...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: Francis Guibernau On February 27, 2024, the Cybersecurity and Infrastructure Security Agency...
Source: securityboulevard.com - Author: Darren Williams Cybersecurity agencies have sounded alarm bells about active exploitation of...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Jeffrey Burt The National Security Agency (NSA) wants organizations adopt zero-trust framework...
Source: securityboulevard.com - Author: cyberwire Paris, France, March 7th, 2024, Cyberwire Company Open Sources FHE Libraries...
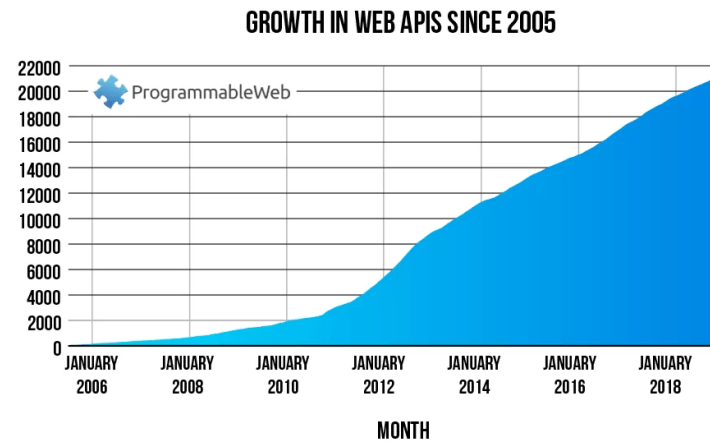
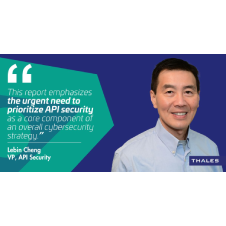
Source: securityboulevard.com - Author: madhav API Security in 2024: Imperva Report Uncovers Rising Threats and the...
Source: securityboulevard.com - Author: Axiad In a recent blog post, we discussed what phishing-resistant multi-factor authentication...
Source: securityboulevard.com - Author: The Constella Team IoT’s (Internet of Things) rapid development has unleashed a...
Source: securityboulevard.com - Author: The Constella Team There’s a rising trend of domain disputes, possibly due...
Source: securityboulevard.com - Author: Jeffrey Burt Healthcare providers groups are ramping up pressure on the federal...