Source: securityboulevard.com - Author: Team Nuspire In the dynamic realm of cybersecurity, the MITRE ATT&CK framework...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Chris Garland The discovery of the backdoor in xz utils compression software...
Source: securityboulevard.com - Author: Thomas Gloerfeld In today’s digitally driven world, data security and privacy are...
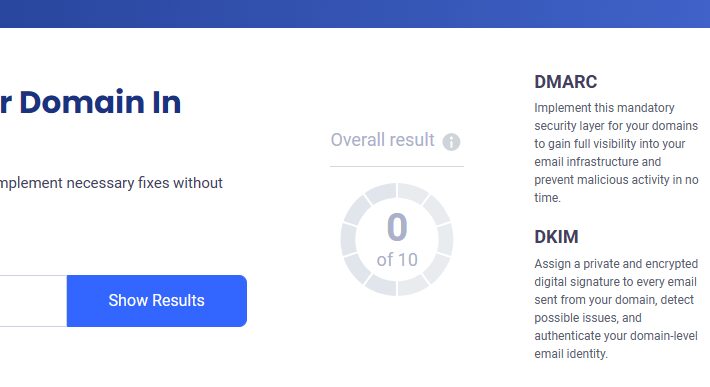
Source: securityboulevard.com - Author: Jeremy Moser Email marketing is a mighty tool for connecting with your...
Source: securityboulevard.com - Author: sparsh Building trust in the financial industry, from the customer’s point of...
Source: securityboulevard.com - Author: Votiro This Faith-based Broadcast Network shares its messages via TV and new...
Source: securityboulevard.com - Author: DataDome There’s plenty of money in advertising, and bots want a piece....
Source: securityboulevard.com - Author: Jeff Martin The risk both to and from AI models is a...
Source: securityboulevard.com - Author: Richi Jennings Last year’s Chinese hack of federal agencies’ email is still...
Source: securityboulevard.com - Author: Jeffrey Burt An embattled National Institute of Standards and Technology (NIST), hobbled...
Source: securityboulevard.com - Author: Alberto Casares In an era where digital integration is pervasive, cybersecurity crisis...
Source: securityboulevard.com - Author: Courtney Chatterton As businesses grow and expand their operations, their third-party risk...
Source: securityboulevard.com - Author: Eric Fourrier The landscape of appsec is more competitive than ever, but...
Source: securityboulevard.com - Author: Katie Fritchen How Azusa’s technology team makes web filtering and online safety...
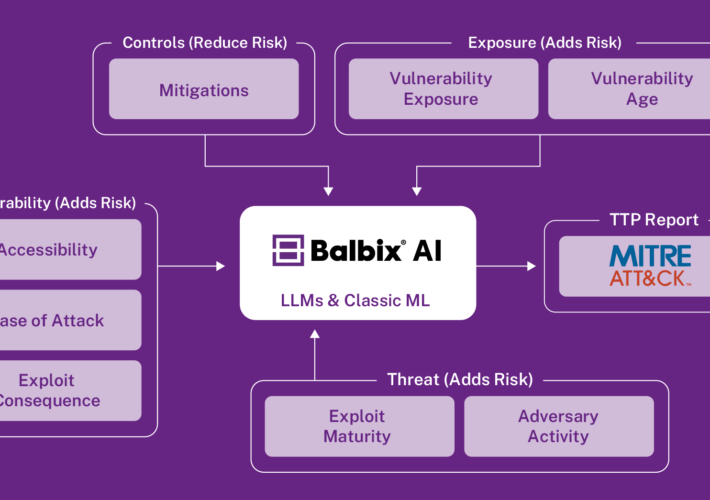
Source: securityboulevard.com - Author: Aravind Iyengar In the previous blog post, we described how Balbix leverages...
Source: securityboulevard.com - Author: Rajan Sodhi In the ever-evolving landscape of corporate sustainability, the European Union’s...
Source: securityboulevard.com - Author: Stevie Caldwell It’s Saturday night. You’re out to dinner with friends. Suddenly,...
Source: securityboulevard.com - Author: Joao Correia xz is a widely distributed package that provides lossless compression...
Source: securityboulevard.com - Author: Bruce Schneier The cybersecurity world got really lucky last week. An intentionally...
Source: securityboulevard.com - Author: Richi Jennings Class action attorney David Boies asked for $5,000 per user,...
Source: securityboulevard.com - Author: Bruce Schneier Through a 2010 FOIA request (yes, it took that long),...
Source: securityboulevard.com - Author: Mark Allers In the rapidly evolving cybersecurity landscape, a Zero Trust (ZT)...
Source: securityboulevard.com - Author: Riddika Grover The internet that we use today is a massive network...
Source: securityboulevard.com - Author: Marc Handelman *** This is a Security Bloggers Network syndicated blog from...
Source: securityboulevard.com - Author: Threat Overview On March 19, 2024, CISA, along with other participating agencies,...
Source: securityboulevard.com - Author: Tony Bradley Organizations must navigate through a tumultuous sea of cybersecurity threats...
Source: securityboulevard.com - Author: Paul Roberts Security experts are sounding alarms about what some are calling...
Source: securityboulevard.com - Author: David Brunsdon Weekly Threat Intelligence Report Date: April 1, 2024 Prepared by:...
Source: securityboulevard.com - Author: Jeffrey Burt The open source community, federal agencies and cybersecurity researchers are...
Source: securityboulevard.com - Author: Enzoic The White House put out an official letter to governors (March...