Source: securityboulevard.com - Author: Nathan Eddy A surge in data-stealing malware incidents targeted nearly 10 million...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
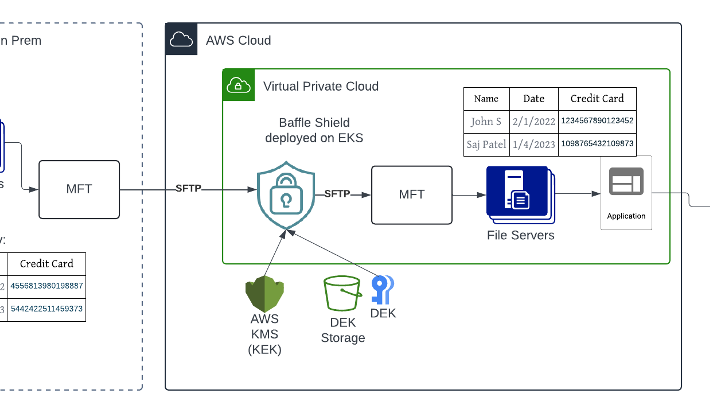
Source: securityboulevard.com - Author: Sushant Rao, SVP of Marketing Financial institutions and healthcare providers deal with...
Google Adds Security Command Center Enterprise to Mandiant Portfolio – Source: securityboulevard.com
Source: securityboulevard.com - Author: Michael Vizard Google added a Security Command Center Enterprise platform to unify...
Source: securityboulevard.com - Author: Steven J. Vaughan-Nichols When HashiCorp dumped its open-source Mozilla license for the...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Michael Vizard An analysis of high-severity threats in 2023 detected by Barracuda...
Source: securityboulevard.com - Author: Jeffrey Burt A beleaguered healthcare industry, already a top target of cybercriminals,...
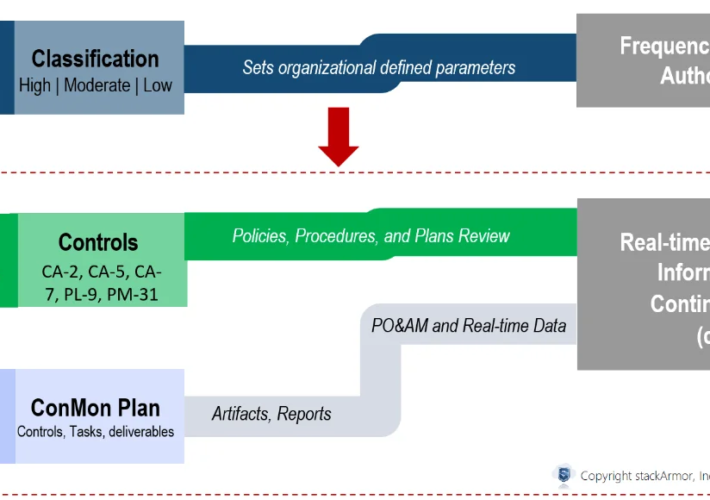
Source: securityboulevard.com - Author: stackArmor As agencies modernize and increasingly move critical business processes and data...
Source: securityboulevard.com - Author: Tom Eston Episode 324 features discussions on a significant AT&T data breach...
Source: securityboulevard.com - Author: Lohrmann on Cybersecurity Almost everyone has heard of ChatGPT. But Jeff Brown,...
Source: securityboulevard.com - Author: Ofir Stein Maintaining a strong security posture is crucial in today’s digital...
Source: securityboulevard.com - Author: NSFOCUS Vulnerability Overview Recently, NSFOCUS CERT detected that the security community disclosed...
Source: securityboulevard.com - Author: Ahona Rudra Reading Time: 5 min Since the EU adopted the General...
Source: securityboulevard.com - Author: Branden Williams You may not realize that I got my start in...
Source: securityboulevard.com - Author: Michael Vizard Salt Security this week revealed it has embedded a generative...
Source: securityboulevard.com - Author: Ryan Healey-Ogden Think of it this way: The more your team is...
Source: securityboulevard.com - Author: Christopher Maddalena Let’s dive into what makes this so exciting! There’s so...
Source: securityboulevard.com - Author: Richi Jennings The Federal Communications Commission is finally minded to address decades-old vulnerabilities.Dusty,...
Source: securityboulevard.com - Author: Jeffrey Burt The chief executive of vulnerability-plagued Ivanti said the management software...
Source: securityboulevard.com - Author: Mahesh Raj Mohan Hot Topics FCC: Phone Network Bugs Must Be Fixed...
Source: securityboulevard.com - Author: Mike Larkin It’s been a week since the xz backdoor dropped. I...
Source: securityboulevard.com - Author: Nathan Eddy The Cybersecurity and Infrastructure Security Agency (CISA) issued a Notice...
Source: securityboulevard.com - Author: Joao Correia The KernelCare team is working on deploying a live patch...
Source: securityboulevard.com - Author: AnneMarie Avalon Certificate provisioning refers to the process of obtaining, deploying, and...
Source: securityboulevard.com - Author: Riddika Grover 5G technology impacts not just our daily lifestyle but the...
Source: securityboulevard.com - Author: Nadav Avital HTTP/2, a widely adopted web communication protocol, organizes data transmission...
Source: securityboulevard.com - Author: Shriram Sharma Our commitment to innovation is deeply rooted in the feedback...
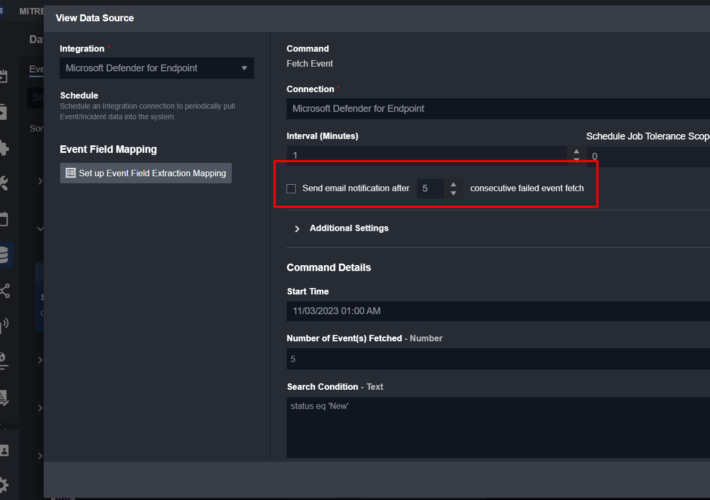
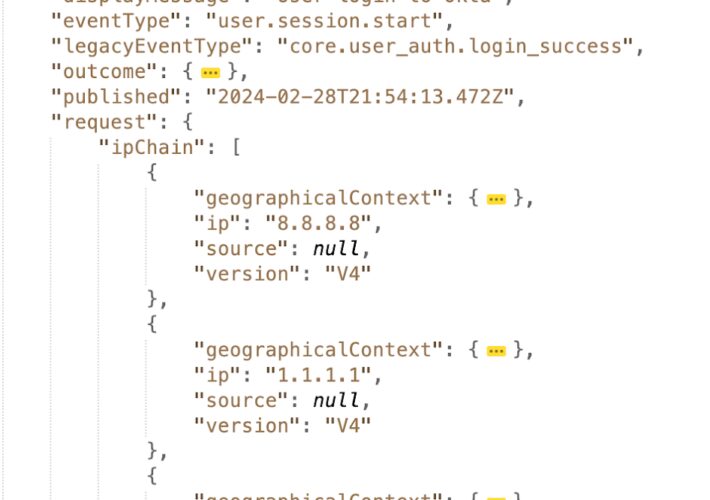
Source: securityboulevard.com - Author: Farah Iyer Being able to identify client IP addresses is essential for...
Source: securityboulevard.com - Author: Anton Chuvakin This blog series was written jointly with Amine Besson, Principal...
Source: securityboulevard.com - Author: Jeffrey Burt Google is prototyping a new technology in Chrome that is...