Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: *Sina Sajadmanesh, Ali Shahin Shamsabadi, Aurélien Bellet, Daniel Gatica-Perez*...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Kaustubh Jagtap Author: Kaustubh Jagtap, Product Marketing Director, SafeBreach On April 18th,...
Source: securityboulevard.com - Author: Brian Robertson The newest version of the European Union Network and Information...
Source: securityboulevard.com - Author: Marc Handelman via the inimitable Daniel Stori at Turnoff.US! Permalink *** This...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: Natalia Kazankova Security testing allows you to evaluate the robustness of applications...
Source: securityboulevard.com - Author: David Lindner, Director, Application Security Insight #1 One of the most significant...
Source: securityboulevard.com - Author: Joao Correia PHP Extended Lifecycle Support (ELS) allows you to continue using...
Source: securityboulevard.com - Author: Wajahat Raja In light of cookie stealing attacks and to ensure Chrome...
Source: securityboulevard.com - Author: Max Aulakh The world advances based on innovation, and innovation can come...
Source: securityboulevard.com - Author: Nathan Eddy The number of AI-related Zero Days has tripled since November...
Source: securityboulevard.com - Author: Jeffrey Burt Headlines about ransomware in recent years have focused on the...
Source: securityboulevard.com - Author: AJ Starita When looking for sensitive information and other valuable assets, attackers...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: Aaron Linskens The latest webinar in Sonatype’s DevOps Download series, presented in...
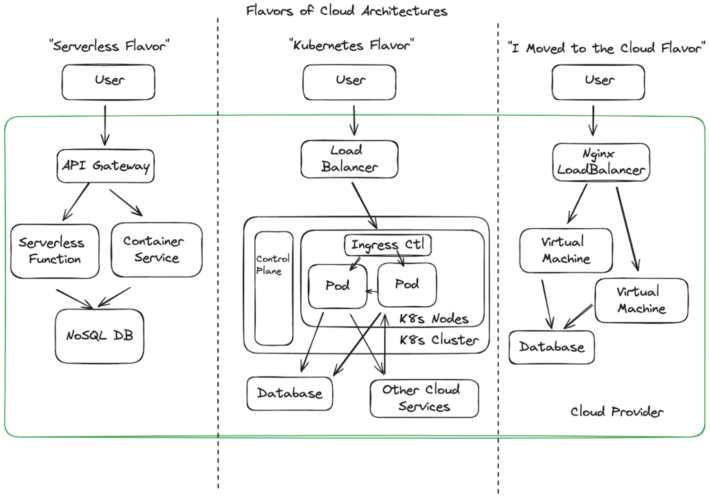
Source: securityboulevard.com - Author: Randy Abrams The rapid adoption of could computing was yesterday’s news 5...
Source: securityboulevard.com - Author: Michael Vizard Cisco today launched a framework that leverages artificial intelligence (AI)...
Source: securityboulevard.com - Author: NSFOCUS Overview Recently, NSFOCUS CERT detected that Palo Alto Networks issued a...
Source: securityboulevard.com - Author: Axiad Earlier this week we made an important announcement highlighting the appointment...
Source: securityboulevard.com - Author: Scott Kannry One could argue that the World’s greatest conquests, competitions, and...
Source: securityboulevard.com - Author: Jeffrey Burt The OpenJS Foundation, which oversees multiple JavaScript projects, thwarted a...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: *Xiang Li, Chaoyi Lu, Baojun Liu, Qifan Zhang, Zhou...
Source: securityboulevard.com - Author: James Berthoty A guest post by James Berthoty the founder of Latio...
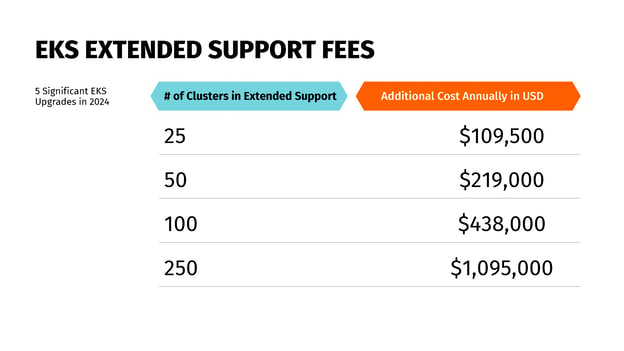
Understanding AWS End of Service Life Is a Key FinOps Responsibility – Source: securityboulevard.com
Source: securityboulevard.com - Author: Mary Henry Amazon Web Services (AWS) announced extended support prices for Amazon...
Source: securityboulevard.com - Author: Avast Blog The air is electric, the skies are clear, and the...
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author In today's hyper-connected world, authentication...
Source: securityboulevard.com - Author: AnneMarie Avalon An Identity Provider (IdP) is a digital service that stores...
Source: securityboulevard.com - Author: Mission Secure In the world of cybersecurity, few environments present as many...
Source: securityboulevard.com - Author: Chris Garland Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...