Source: securityboulevard.com - Author: Mor Avni, Product Manager, Scytale With data breaches and hacking attacks in...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Greg Bulmash At GitGuardian, as cybersecurity experts, we understand there are a...
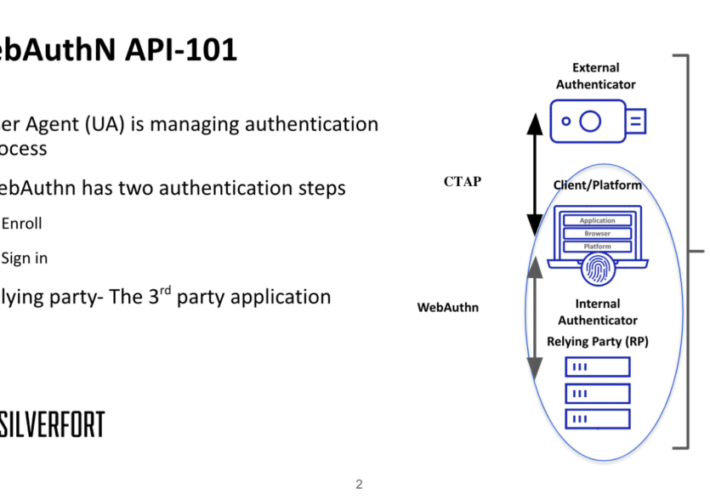
Source: securityboulevard.com - Author: Dor Segal FIDO2 is a modern authentication group term for passwordless authentication....
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » USENIX Security ’23 –...
Source: securityboulevard.com - Author: Lohrmann on Cybersecurity The NASCIO Midyear Conference this past week highlighted the...
Source: securityboulevard.com - Author: NSFOCUS The RSA Conference 2024 will kick off on May 6. Known...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: Jianhao Xu, Kangjie Lu, Zhengjie Du, Zhu Ding, Linke...
Source: securityboulevard.com - Author: NSFOCUS The RSA Conference 2024 will kick off on May 6. Known...
Source: securityboulevard.com - Author: Max Aulakh What is the government if not an organization dedicated to...
Source: securityboulevard.com - Author: Arun Dhamija Recently, I wrapped up my first work trip with Balbix—a...
Source: securityboulevard.com - Author: Nathan Eddy Failure to properly configure authentication led to malicious actors exploiting...
Source: securityboulevard.com - Author: Shriram Sharma For security leaders heading to RSAC 2024 in need of...
Source: securityboulevard.com - Author: Alexa Sander We recently hosted Michael Tapia, Chief Technology Director at Clint...
Source: securityboulevard.com - Author: bacohido By Byron V. Acohido SAN FRANCISCO — On the eve of...
Source: securityboulevard.com - Author: Michael Vizard Palo Alto Networks this week extended its secure access service...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: Jamie Coleman Recently, I chatted with developers from a customer in a...
Source: securityboulevard.com - Author: Matthew Rosenquist This year, virtual CISOs must begin making a difference in...
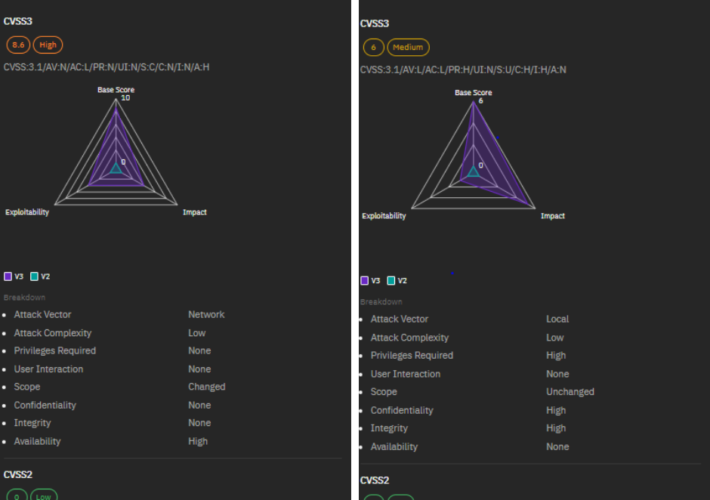
Source: securityboulevard.com - Author: Mackenzie Jackson In this blog series, we look at a new CVE...
Source: securityboulevard.com - Author: Dan Blackwell It’s no secret that NIS2 is around the corner, and...
Source: securityboulevard.com - Author: Shubham Jha Keeping pace with the latest cybersecurity threats is vital for...
Source: securityboulevard.com - Author: Lucas Seewald Dive into our latest Insider Risk Digest, where we unravel...
Source: securityboulevard.com - Author: hrbrmstr I had not planned to blog this (this is an incredibly...
Source: securityboulevard.com - Author: Nik Hewitt Path traversal vulnerabilities, or directory traversal, are now subject to...
Source: securityboulevard.com - Author: Rohan Timalsina Proxmox VE, like any software, is vulnerable to security threats....
Source: securityboulevard.com - Author: bacohido By Ahmed Abdelhalim Businesses today need protection from increasingly frequent and...
Source: securityboulevard.com - Author: Wajahat Raja Recent reports have highlighted that the notorious FIN7 cybercrime group...
Source: securityboulevard.com - Author: NSFOCUS The RSA Conference 2024 will kick off on May 6. Known...
Source: securityboulevard.com - Author: Bill Doerrfeld Cybersecurity experts agree open-source software (OSS) needs to evolve in...
Source: securityboulevard.com - Author: cybernewswire Tel Aviv, Israel, May 2, 2024, CyberNewsWire — LayerX, pioneer of...