Source: securityboulevard.com - Author: Paul Roberts Companies in the crosshairs of advanced persistent threat (APT) actors...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
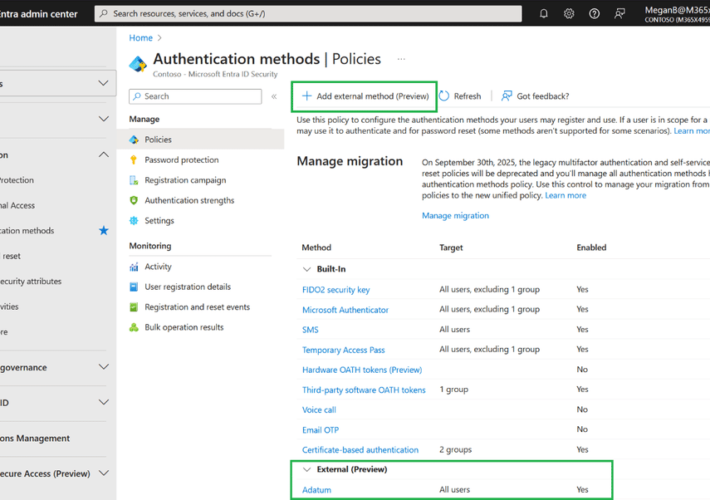
Source: securityboulevard.com - Author: Zev Brodsky Silverfort is excited to announce our integration with external authentication...
Source: securityboulevard.com - Author: Wajahat Raja The recent crackdown on the crypto mixer money laundering, Samourai,...
Source: securityboulevard.com - Author: Rebecca Kappel The financial industry is experiencing a gold rush of sorts...
Source: securityboulevard.com - Author: Nudge Security Blog For anyone who has been through a corporate merger...
Source: securityboulevard.com - Author: Matt Kelly Every organization needs to have security measures and policies in...
Source: securityboulevard.com - Author: Jeffrey Burt In the ever-evolving world of ransomware, it’s getting easier for...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: Jaron Mink, Harjot Kaur, Juliane Schmüser, Sascha Fahl, Yasemin...
Source: securityboulevard.com - Author: John Gallagher RSA Conference delivers in terms of interesting dialogues with other...
Source: securityboulevard.com - Author: Brendan J. Fitzpatrick Welcome to Axio’s series on cybersecurity for healthcare providers,...
Source: securityboulevard.com - Author: Kevin Smith When the school year is winding down, vacations are very...
Source: securityboulevard.com - Author: cybernewswire Philadelphia, Pennsylvania, May 8th, 2024, CyberNewsWire Security Risk Advisors (SRA) announces...
Source: securityboulevard.com - Author: Richi Jennings Supreme Court “likely” to rule whether new law is constitutional—or...
Source: securityboulevard.com - Author: Rishi Khanna The Kraken Model of Innovation is not just a concept...
Source: securityboulevard.com - Author: cybernewswire SAN FRANCISCO, May 7, 2024, CyberNewsWire –– Hunters, the pioneer in...
Source: securityboulevard.com - Author: Alex Pena Certificate Lifecycle Management (CLM) is a comprehensive strategy for handling...
Source: securityboulevard.com - Author: Ronan Grobler, Compliance Success Manager, Scytale Regardless of your industry, a baseline...
Source: securityboulevard.com - Author: NSFOCUS San Francisco, May 7, 2024 – NSFOCUS, a global leader in cybersecurity,...
Source: securityboulevard.com - Author: Nikhil Menon We are thrilled to announce that Wallarm has clinched the...
Source: securityboulevard.com - Author: Kaseya Navigating Cybersecurity at Kaseya Connect Global 2024 The final day of...
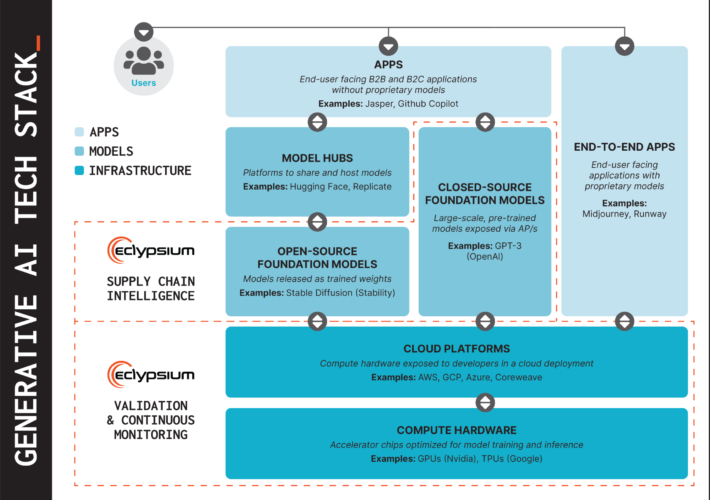
Source: securityboulevard.com - Author: Chris Garland Eclypsium is extending its digital supply chain security to cover...
Source: securityboulevard.com - Author: Chris Garland Today, at RSA Conference 2024, we’re announcing new capabilities to...
Source: securityboulevard.com - Author: Michael Callahan GenAI has the promise to transform companies, and introduce a...
Source: securityboulevard.com - Author: Nathan Eddy Organizations are rushing to integrate AI-driven features into their operations....
Source: securityboulevard.com - Author: Ahona Rudra Reading Time: 4 min Proxies have become a cornerstone of...
White House Cybersecurity Workforce Initiative Backed by Tech Titans – Source: securityboulevard.com
Source: securityboulevard.com - Author: Nathan Eddy With more than half a million cybersecurity positions currently open...
Source: securityboulevard.com - Author: Nisos Nisos Tracking Illegal Pharmaceutical Sales on Social Media Nisos continuously monitors...
Source: securityboulevard.com - Author: Ronan Grobler, Compliance Success Manager, Scytale Let’s be honest: anything with the...
Source: securityboulevard.com - Author: Nathan Eddy Identity and credential misconfigurations pose a major security risk to...
Source: securityboulevard.com - Author: Nikhil Menon A highly concerning security loophole was recently discovered in a...