Source: securityboulevard.com - Author: Nathan Eddy Chief information security officers (CISOs) face mounting pressure as cyberattacks...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Votiro It’s been less than three months since the launch of our...
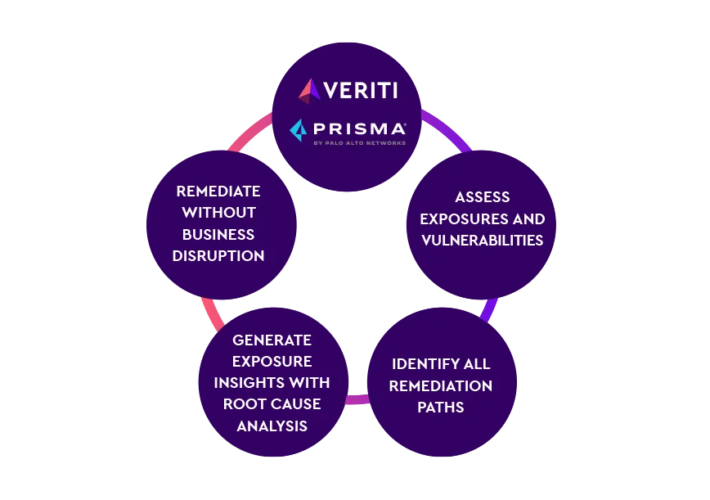
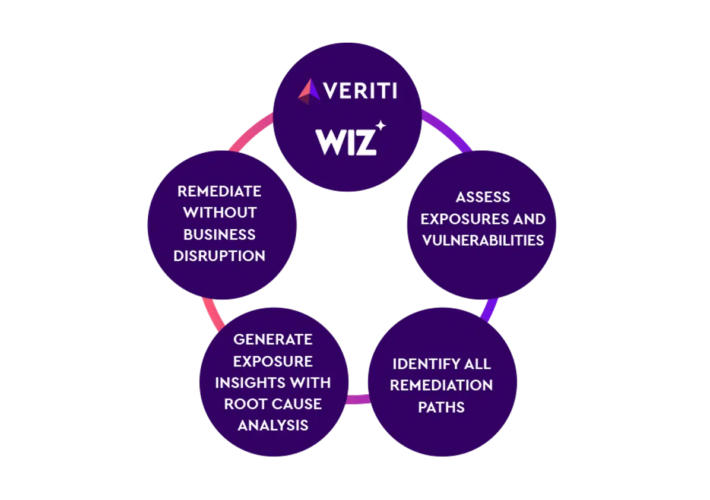
Source: securityboulevard.com - Author: Veriti As enterprises continue to shift towards cloud-based infrastructures, the complexity of...
Source: securityboulevard.com - Author: Leah Hopper Introduction Authorised Economic Operator (AEO) is a status that a...
Source: securityboulevard.com - Author: Veriti Veriti proactively monitors and safely remediates risk across the security infrastructure...
Source: securityboulevard.com - Author: Veriti Veriti proactively monitors and safely remediates risk across the security infrastructure...
Source: securityboulevard.com - Author: Rohan Timalsina The joint alert from CISA and FBI highlights the continued...
Source: securityboulevard.com - Author: Joao Correia In August of last year, I examined several CPU bugs...
Source: securityboulevard.com - Author: Wajahat Raja Recently, HPE Aruba Networking, formerly known as Aruba Networks, has...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: Harman Singh This guide provides an overview of the top 15 network...
Source: securityboulevard.com - Author: Harman Singh Internal penetration testing is a proactive approach that identifies vulnerabilities...
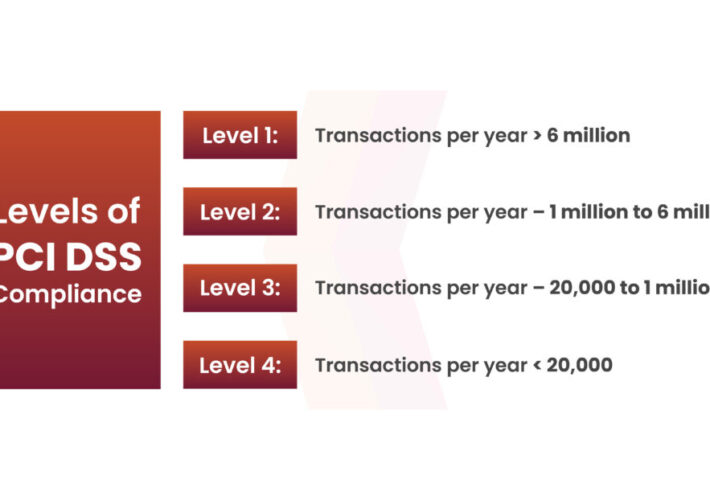
Source: securityboulevard.com - Author: Shikha Dhingra Do you recall the incidents involving Equifax, Target, and British...
Source: securityboulevard.com - Author: Harman Singh Are your wireless networks truly safe from cyber threats? Wireless...
Source: securityboulevard.com - Author: Alexa Sander Recently, we hosted Michael Tapia, Chief Technology Director at Clint...
Source: securityboulevard.com - Author: Richi Jennings Dark web sale of leaked data exposes Dell users to...
Source: securityboulevard.com - Author: Nathan Eddy An advanced persistent threat (APT) group backed by Iran has...
Source: securityboulevard.com - Author: Kelsey Gast A healthcare identity access provider was looking for a security...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: Simone Colombo, Kirill Nikitin, Henry Corrigan-Gibbs, David J. Wu,...
Source: securityboulevard.com - Author: Jeffrey Burt Dell is sending emails to as many as 49 million...
Source: securityboulevard.com - Author: Kevin Smith Maybe you’ve heard there’s an interplanetary-sized gap in the amount...
Source: securityboulevard.com - Author: Marc Handelman via the inimitable Daniel Stori at Turnoff.US! Permalink *** This...
Source: securityboulevard.com - Author: Dwayne McDaniel You can't see The Golden Gate Bridge from downtown San...
Source: securityboulevard.com - Author: Maahnoor Siddiqui In the ever-evolving world of cybersecurity, managing risk is no...
Source: securityboulevard.com - Author: Nathan Eddy Houston, we may have a problem.NASA’s cybersecurity framework for spacecraft...
Source: securityboulevard.com - Author: Rhys Arkins Dependency management is a broad topic encompassing, among other things,...
Source: securityboulevard.com - Author: SecureIQLab The adoption of the cloud is the biggest driver of the...
Source: securityboulevard.com - Author: Alberto Casares In recent times, Israel and Iran have been caught up...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: Jeffrey Burt A group of bad actors — likely from China —...









![15 Best Network Pentesting Tools [Free + Paid] – Source: securityboulevard.com](https://ciso2ciso.com/wp-content/uploads/2024/05/132031/15-best-network-pentesting-tools-free-paid-source-securityboulevard-com-710x500.jpg)