Source: securityboulevard.com - Author: John Doetch In the rapidly evolving landscape of cybersecurity, organizations are increasingly...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: John P. Mello Jr. One fundamental principle every threat modeler learns very...
Source: securityboulevard.com - Author: Nitzan Gursky We often find ourselves entrenched in yesterday’s battles, grappling with...
Source: securityboulevard.com - Author: Bruce Schneier Microsoft is working on a promising-looking protocol to lock down...
Source: securityboulevard.com - Author: CISO Global May 16, 2024 James Keiser, Director of Secured Managed Services...
Source: securityboulevard.com - Author: Rohan Timalsina Recently, the Ubuntu security team has fixed multiple security issues...
Source: securityboulevard.com - Author: bacohido By Byron V. Acohido Hardware-based cybersecurity solutions are needed to help...
Source: securityboulevard.com - Author: Wajahat Raja In the digital realm, security is paramount, especially when it...
Source: securityboulevard.com - Author: Jeffrey Burt The operators behind the Ebury server-side malware botnet have been...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: Editor Next week our founder Simon Moffatt will be speaking at an...
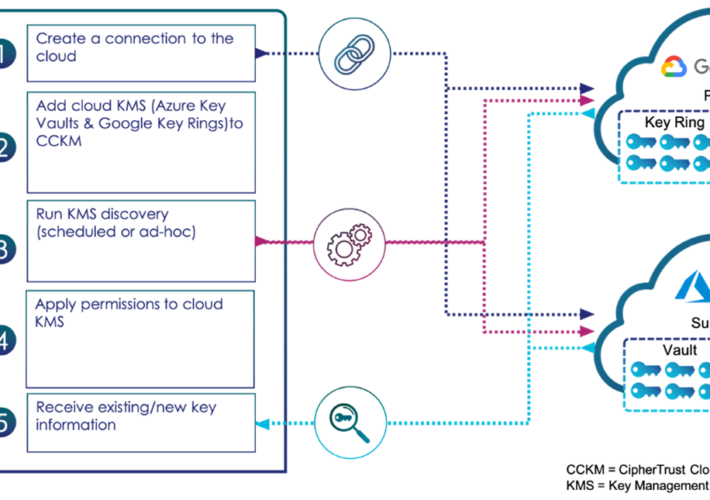
Source: securityboulevard.com - Author: madhav Systematically Bring to Light the Keys in Your Clouds madhav Wed,...
Source: securityboulevard.com - Author: Rohan Timalsina In recent Ubuntu and Debian security updates, several vulnerabilities have...
Source: securityboulevard.com - Author: Adar Givoni, Director of Compliance, Scytale Achieving and maintaining compliance with data...
Source: securityboulevard.com - Author: TuxCare Team It’s never been more important for businesses to invest in...
Source: securityboulevard.com - Author: Wajahat Raja In the realm of cybersecurity, vigilance is paramount. Recently, the...
Source: securityboulevard.com - Author: Kellie Roessler The 2024 RSA Conference can be summed up in two...
Source: securityboulevard.com - Author: Sectrio When talking about industries, few are as critical to global infrastructure...
Source: securityboulevard.com - Author: Matthew Rosenquist There are tremendous opportunities in cybersecurity and the industry needs...
Source: securityboulevard.com - Author: ReversingLabs ReversingLabs has released a new application for Splunk users to enhance...
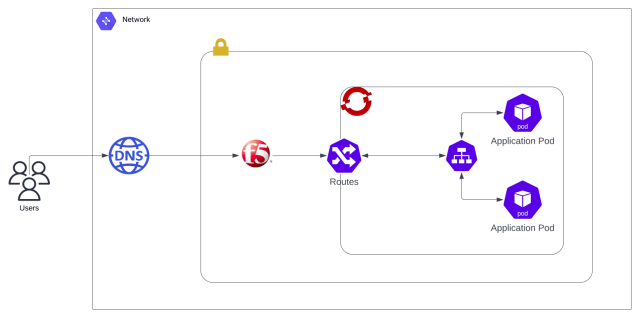
Source: securityboulevard.com - Author: Karthik Kannan Kubernetes is an open-source container orchestration platform that automates the...
Source: securityboulevard.com - Author: Carolynn van Arsdale The 32nd annual RSA Conference (RSAC) – one of...
Source: securityboulevard.com - Author: Sectrio Sectrio and DigiGlass by Redington’s leadership at the new OT/ICS and...
Source: securityboulevard.com - Author: Danielle Guetta WHAT are Machine Credentials? Machine Credentials are a collective noun...
Source: securityboulevard.com - Author: Danielle Guetta What are Service Accounts? Service Accounts are Non-Human Identity accounts...
Source: securityboulevard.com - Author: Rohan Timalsina Ubuntu 24.04 LTS was released on April 25, 2024, with...
Source: securityboulevard.com - Author: Danielle Guetta What are OAuth Tokens? OAuth (Open Authorization) Tokens are Non-Human...
Source: securityboulevard.com - Author: Natalia Kazankova As vehicles become increasingly reliant on software, secure and functional...
Source: securityboulevard.com - Author: Wajahat Raja In a recent disclosure, cloud storage giant Dropbox revealed a...
Source: securityboulevard.com - Author: cybernewswire Torrance, California, May 13th, 2024, CyberNewsWire Criminal IP, a renowned Cyber...