Source: securityboulevard.com - Author: Heidi King Multi-cloud Identity Orchestration platform ensures continuous access to applications even...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
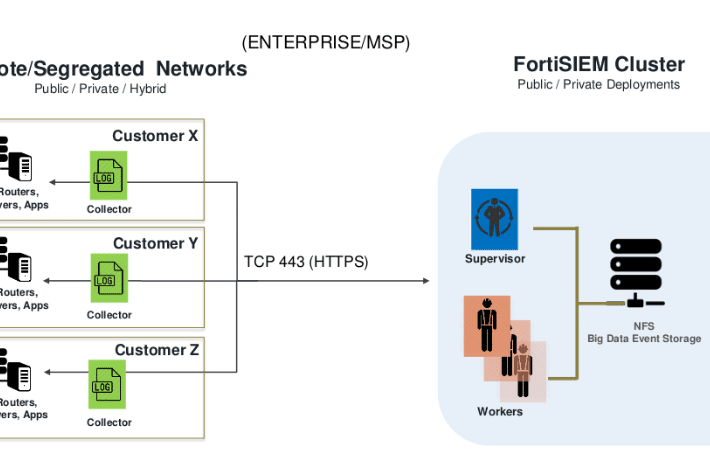
Source: securityboulevard.com - Author: Zach Hanley In early 2023, given some early success in auditing Fortinet...
Source: securityboulevard.com - Author: Rebecca Kappel Did you know that 80% of breaches exploit legitimate identities...
Source: securityboulevard.com - Author: Rohan Timalsina AlmaLinux 9.4, codenamed “Seafoam Ocelot,” arrived on May 6, 2024....
Source: securityboulevard.com - Author: bacohido By Byron V. Acohido The open-source Chromium project seeded by Google...
Source: securityboulevard.com - Author: Mor Avni, Product Manager, Scytale In an era marked by rapid advancements...
Source: securityboulevard.com - Author: Tom Eston In episode 330 Tom, Scott, and Kevin discuss the new...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: Lohrmann on Cybersecurity The dramatic growth in GenAI and AI adoption is...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: James Tobias The London Drugs cyber attack has been making headlines throughout...
Source: securityboulevard.com - Author: Shikha Dhingra Secure code review is a combination of automated and manual...
Source: securityboulevard.com - Author: Erez Hasson Marketing teams need a comprehensive bot management solution to address...
Source: securityboulevard.com - Author: Alexa Sander Recently, we hosted Michael Tapia, Chief Technology Director at Clint...
Brothers Indicted for Stealing $25 Million of Ethereum in 12 Seconds – Source: securityboulevard.com
Source: securityboulevard.com - Author: Jeffrey Burt It took two brothers who went to MIT months to...
Source: securityboulevard.com - Author: Votiro On the heels of our launch of a unified, Zero Trust...
Source: securityboulevard.com - Author: Pondurance Every month, the Pondurance team hosts a webinar to keep clients...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters:Scott Constable, Jo Van Bulck, Xiang Cheng, Yuan Xiao, Cedric...
Source: securityboulevard.com - Author: Richi Jennings Pictured: Several successful American IT professionals.The U.S. Justice Department says N....
Source: securityboulevard.com - Author: Francis Guibernau On May 10, 2024, the Cybersecurity and Infrastructure Security Agency...
Source: securityboulevard.com - Author: stackArmor From this we can see that all the agencies that we...
Source: securityboulevard.com - Author: Emma Kelly Today, data is the key driver of success, and even...
Source: securityboulevard.com - Author: Nathan Eddy Ransomware claims surged by 64% year-over-year, particularly among mid-market and...
Source: securityboulevard.com - Author: Emma Kelly Step 3. Testing and Validation With the enhanced controls and...
Source: securityboulevard.com - Author: Riddika Grover In today’s digital age, cybersecurity is more important than ever....
Source: securityboulevard.com - Author: Harman Singh Do you want to enhance your organisation’s cybersecurity by identifying...
Source: securityboulevard.com - Author: Jeffrey Burt A surge in phishing attacks that use emails appearing to...
Source: securityboulevard.com - Author: Harman Singh Secure code ensures the Internet runs smoothly, safely, and securely....
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters:Shixuan Zhao, Pinshen Xu, Guoxing Chen, Mengya Zhang, TYinqian Zhang,...
Source: securityboulevard.com - Author: Sonya Duffin If you use generative artificial intelligence (GenAI) tools at work,...